
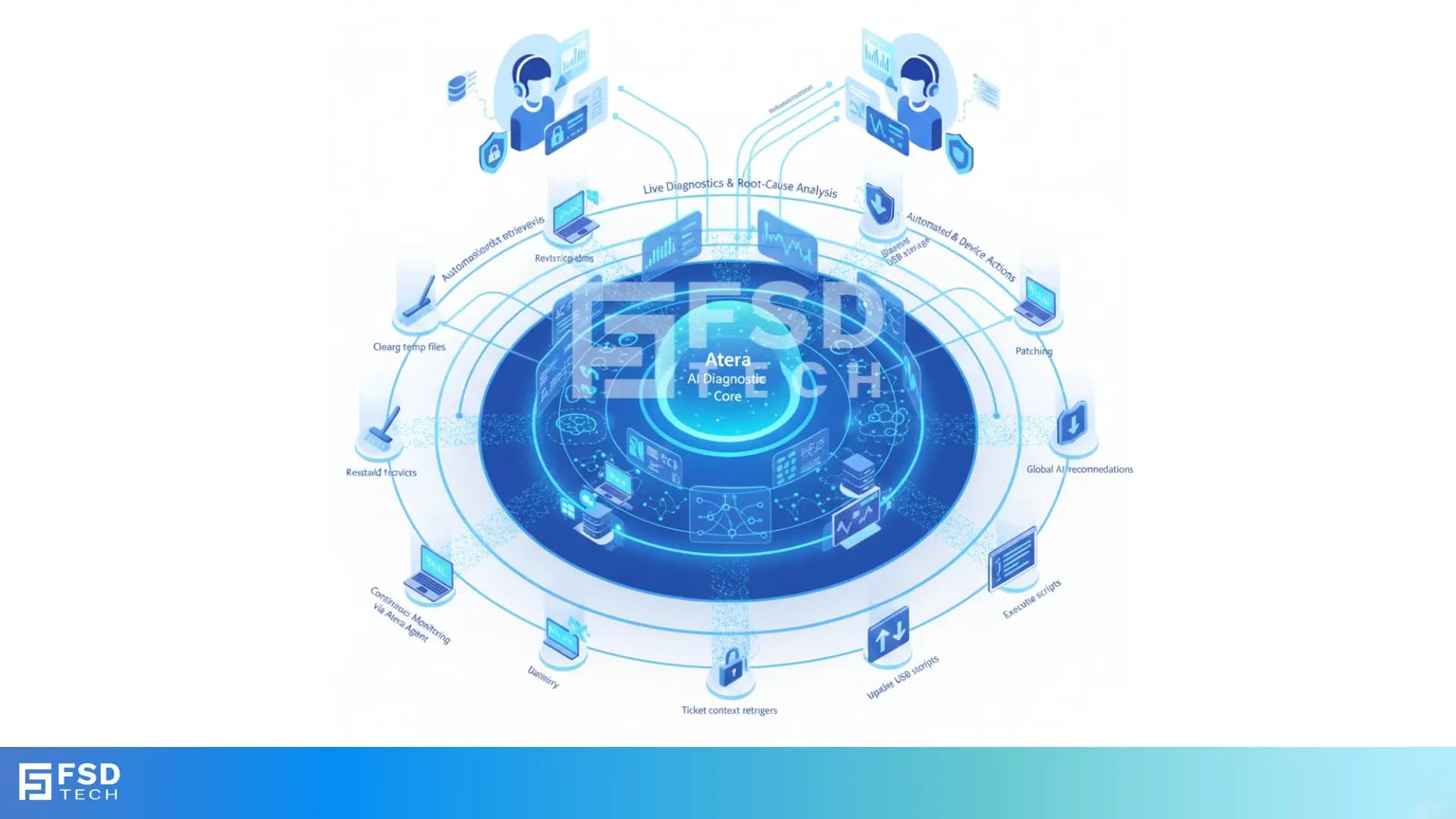
AI-Driven Remote Session Summaries in Atera: Turning Hands-On Support Into Instant Documentation
🕓 January 1, 2026

🕓 January 1, 2026
🕓 December 15, 2025

🕓 December 12, 2025
.webp&w=3840&q=75)
🕓 December 8, 2025

🕓 November 8, 2025

🕓 November 2, 2025

🕓 December 27, 2025

🕓 December 26, 2025

🕓 December 23, 2025

🕓 December 19, 2025
🕓 December 16, 2025

🕓 January 2, 2026

🕓 December 31, 2025

🕓 December 29, 2025

🕓 December 25, 2025

🕓 December 22, 2025

🕓 November 24, 2025
🕓 September 16, 2025
🕓 September 5, 2025

🕓 September 4, 2025

🕓 September 3, 2025
.jpg&w=3840&q=75)
🕓 September 2, 2025

🕓 December 27, 2025

🕓 December 23, 2025

🕓 December 19, 2025
🕓 December 16, 2025
🕓 December 11, 2025
.jpg&w=3840&q=75)
🕓 January 2, 2026

🕓 January 2, 2026

🕓 January 1, 2026

🕓 December 31, 2025

🕓 December 31, 2025
.jpg&w=3840&q=75)
Click fraud = illegitimate clicks draining PPC budgets via bots or competitors. Stop it with real-time detection software, IP blocking & campaign best pract...
🕓 January 2, 2026

BEC = targeted email scam impersonating executives/vendors for wire fraud or data theft. Stop it with verification protocols, DMARC & training – proactive d...
🕓 January 2, 2026

Phishing simulation = safe, mock phishing emails testing employee awareness. Measures click/report rates, delivers instant training – proactive way to harden yo...
🕓 January 1, 2026

Zero Trust = never trust, always verify every access request. Continuous authentication, least privilege & microsegmentation – essential shift from perimete...
🕓 December 31, 2025

RPA = software bots automating repetitive, rule-based tasks like data entry & invoices. Fast, error-free & scalable – frees humans for creative work, dr...
🕓 December 31, 2025

Quantum cryptography uses physics (QKD) to distribute unbreakable keys – detecting eavesdroppers instantly. Defends against quantum computers breaking RSA/ECC –...
🕓 December 30, 2025