.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

Slow apps can ruin a good work day. You might feel frustrated when video calls freeze or files take too long to send. Have you ever wondered why some apps work well while others fail? There is a way to fix these issues for your whole team at once. You can stop the lag and keep your team happy with a simple change to your network.
With Cato Networks, you can take control without relying on scattered hardware appliances or difficult policy scripting. Everything is defined in one place and enforced in the cloud, at the Cato PoP closest to the user.
This guide breaks down how to implement bandwidth shaping and Quality of Service (QoS) policies in Cato’s current CMA interface. You’ll walk away knowing where to configure, what to prioritize, and how to fine-tune performance based on real data.
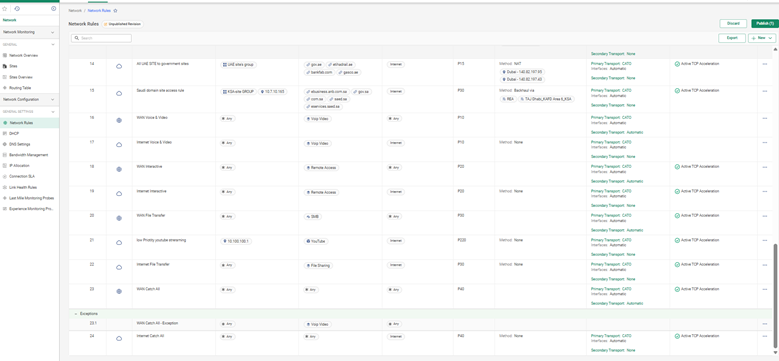
Here’s where you’ll find the bandwidth management options in the updated Cato platform:
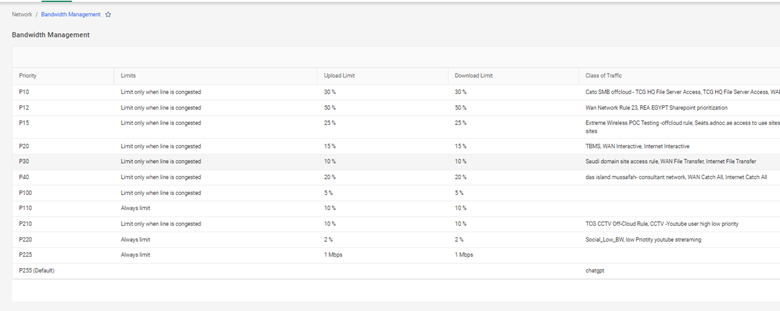
QoS Classes are your way of telling the network what matters most.
Each class can be defined with: - Priority (High / Medium / Low) - Minimum guaranteed bandwidth - Traffic shaping behavior for latency or jitter-sensitive flows
You can use predefined templates or create your own custom definitions.
Cato simplifies classification with auto-detection of over 5,000 known applications. You don’t need to build traffic rules from scratch.
This allows you to ensure, for example, that Teams gets high-priority treatment even when the network is under load.
A financial firm set Teams, Zoom, and Bloomberg to the Real-Time class. File-sharing apps were demoted to Bulk. They saw a 35% reduction in jitter complaints overnight.
Not every office or region needs the same policy. Cato’s site-level shaping gives you flexibility across locations.
From Network > Site Configuration > Bandwidth Management, you can: - Set max bandwidth per uplink/downlink - Allocate minimums for each QoS class - Choose whether shaping applies to inbound, outbound, or both directions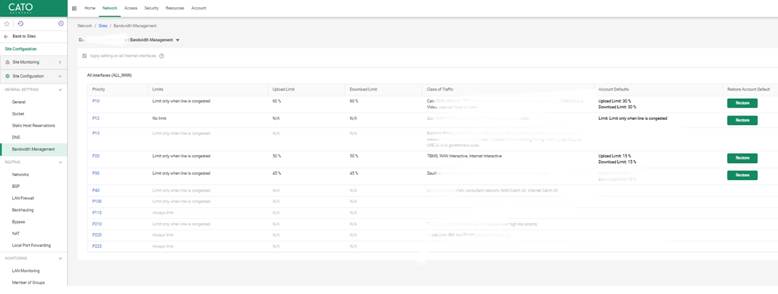
Your UAE headquarters may have a 1 Gbps fiber link. A remote warehouse in KSA may use a 50 Mbps LTE connection. You can: - Guarantee 15% of bandwidth for VoIP everywhere - Restrict OneDrive and Google Drive only at low-bandwidth locations - Let Salesforce traffic burst during non-business hours
Policy without visibility is just guesswork. The QoS Dashboard in Analytics gives a clear view of: - Per-class bandwidth usage - Packet drops or queuing delay - Trends across time and by site or app
You can simulate load conditions using the built-in Traffic Generator Tool under Network > Tools.
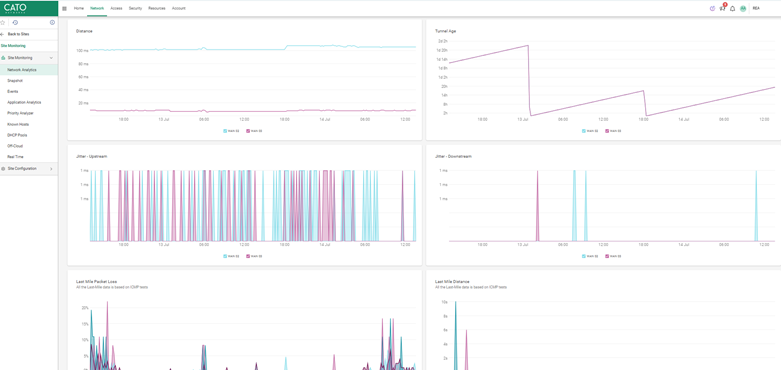
Enable alerts for dropped packets or class saturation. Use the REST API to stream traffic metrics to your NOC tools or SIEM dashboards.
Contact Our Cato SASE Experts Today
Yes. Cato allows identity-aware QoS policies using AD/SAML.
Yes. Cato’s cloud-native engine recalculates priorities dynamically.
Yes. Apply global defaults, then override as needed per location.
Both directions can be shaped individually.
Yes. Cato maintains a dynamic application catalog. You can also add custom tags.

Anas is an Expert in Network and Security Infrastructure, With over seven years of industry experience, holding certifications Including CCIE- Enterprise, PCNSE, Cato SASE Expert, and Atera Certified Master. Anas provides his valuable insights and expertise to readers.
Share it with friends!
share your thoughts