.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
.jpg&w=3840&q=75)
Are you paying for real customers, or are you handing over your budget to scammers? If you run Pay-Per-Click (PPC) campaigns on platforms like Google Ads, your advertising budget faces a constant threat. This threat is called click fraud.
Click fraud can be understood as the act of illegitimately clicking on a PPC advertisement. This is done with the aim of either draining the advertiser's budget or gaining an unfair advantage over a competitor. It is nothing but a type of digital theft.
You are charged for every click, but when the click comes from a bot or a malicious user, you gain no actual business value. This misuse of advertising funds seriously affects your return on investment (ROI).
You need powerful tools and strategies to protect your marketing spend. This guide will fully explain click fraud detection software and how it works to protect your advertising campaigns. We will also discuss methods for ad fraud prevention.
The main keyword here is click fraud definition. Click fraud refers to the deceptive practice where a person, an automated script, or a computer program imitates a legitimate user clicking on a PPC ad. This fraudulent click causes the advertiser to pay a fee to the host platform (like Google or Facebook) for a click that holds no real potential for conversion or business.
This practice falls under the umbrella of what is click fraud in cyber security. While often related to financial loss, it also comprises the use of automated systems and botnets—a major security concern. In simple words, it is a sophisticated method of stealing advertising money.
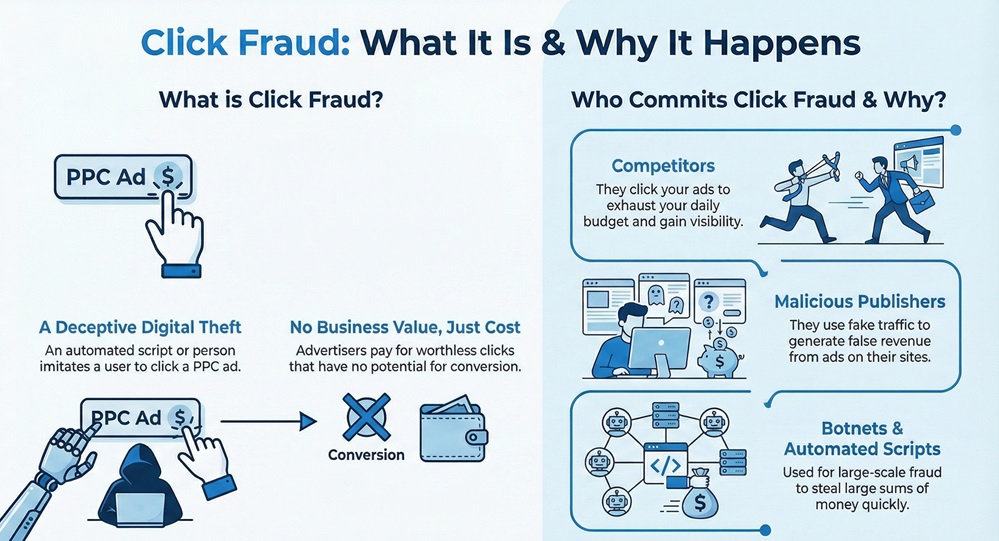
Now, the question arises, why would someone engage in click fraud? The motivations are mainly financial.
Also Read: What is a Botnet? How Botnet Attacks Work & Prevention
To understand how click fraud detection software works, you must first know how a real click differs from a fraudulent one. Let us now discuss the key differences.
| Basis for Comparison | Real Click | Click Fraud |
|---|---|---|
| Source | A genuine human user actively searching for your product or service. | Bots, scripts, click farms, or malicious competitors. |
| Intent | Intent to learn more, purchase, or sign up (conversion intent). | Intent to deplete the budget or generate false revenue (malicious intent). |
| Behavior | Natural movement, browsing multiple pages, and spending a reasonable time on the site. | High speed, single-page visits, immediate bounce, and often multiple clicks from the same IP address. |
| Data Trail | Complete user data, including browser type, device details, and typical browsing patterns. | Missing or falsified data, the use of Virtual Private Networks (VPNs) or proxies to hide the real location. |
Click fraud detection software is nothing but a specialized tool that actively monitors your PPC campaigns. It analyzes every single click in real-time. This software employs advanced algorithms and machine learning to identify and filter out fraudulent or invalid traffic before it costs you money. It acts as an essential shield for your marketing budget.
You can consider this software as the security guard for your advertisements. It examines the behavior and origin of every click to determine its legitimacy. Ad fraud detection tools use several parameters to perform this task.
This is where the software plays a vital role in ad fraud prevention. The process typically involves several sequential steps.
Also Read: Multi-Factor Authentication (MFA): All You Need to Know
When selecting an ad fraud detection tool, you need to look for specific features that guarantee comprehensive protection. These tools help you how to detect click fraud.
While click fraud detection software handles the technical heavy lifting, you also play a vital role in ad fraud prevention. This involves making smart choices within your advertising platform itself.
1. Adjusting Ad Platform Settings
You can use the built-in features of your ad platform to set up some basic defenses.
2. Monitoring and Analysis
Consistent analysis of your campaign performance helps you learn how to detect click fraud manually.
3. Campaign Structure
The way you structure your campaigns can also serve as a protective layer.
Also Read: Cyber Threat Intelligence (CTI) in Cybersecurity
While discussing click fraud, it is important to briefly touch upon a related, but different, cyber threat: phishing. The question of what if you click on a phishing link is relevant because both attacks rely on a malicious click.
Phishing aims at stealing your sensitive personal data (passwords, credit card numbers) by tricking you into entering the information on a fake website or downloading malware. The criminal is targeting you directly.
If you accidentally click on a phishing link, immediately take these actions:
Understanding the threat model of phishing reinforces the need for robust security, just as ad fraud prevention protects your financial assets.
So, with the above discussion, we can say that click fraud is a sophisticated, costly threat that actively drains your vital PPC budget. It is nothing but digital theft targeting your marketing investment. You cannot rely on ad platforms alone; you must implement specialized click fraud detection software. This tool uses real-time behavioral analysis and pattern recognition to identify fraudulent clicks. Its ability to automatically block malicious IP addresses ensures effective ad fraud prevention.
By integrating the best click fraud software and maintaining smart campaign targeting, you stop wasting money on bots and competitors. You secure your funds and ensure your ads reach actual customers. Take proactive control of your advertising budget today and ensure every click works toward your business growth.
Worried About Ad Fraud? Reach out to us for immediate help
So, with the above discussion, we can say that click fraud is a real and costly problem for any business using paid advertising. Protecting your budget is not an option; it is a necessity for your business growth.

Let us now address common questions you may have about click fraud.
Click fraud costs businesses billions of dollars worldwide every year. According to various reports, a significant percentage of all paid search traffic—often estimated between 10% and 20%—is fraudulent. Therefore, if you spend $10,000 per month on PPC, you could potentially be losing up to $2,000 every month on fake clicks.
Yes, Google, as well as other major ad platforms, has built-in systems to detect and filter out invalid clicks. However, sophisticated fraud often bypasses these general systems. Click fraud detection software provides a more in-depth, customizable, and real-time defense layer, working in addition to Google's basic protection. This specialized software is often more advanced at catching automated bot clicks.
No, the software operates by placing a small piece of code on your website or integrating directly via an Application Programming Interface (API). The process of click analysis and blocking happens incredibly fast—in milliseconds—and does not noticeably affect the loading speed of your pages.
You typically see results almost immediately. Within the first 24 to 48 hours of implementation, the software often identifies and blocks a large number of fraudulent sources that were already clicking your ads. The savings will become clear in your daily reporting.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts