
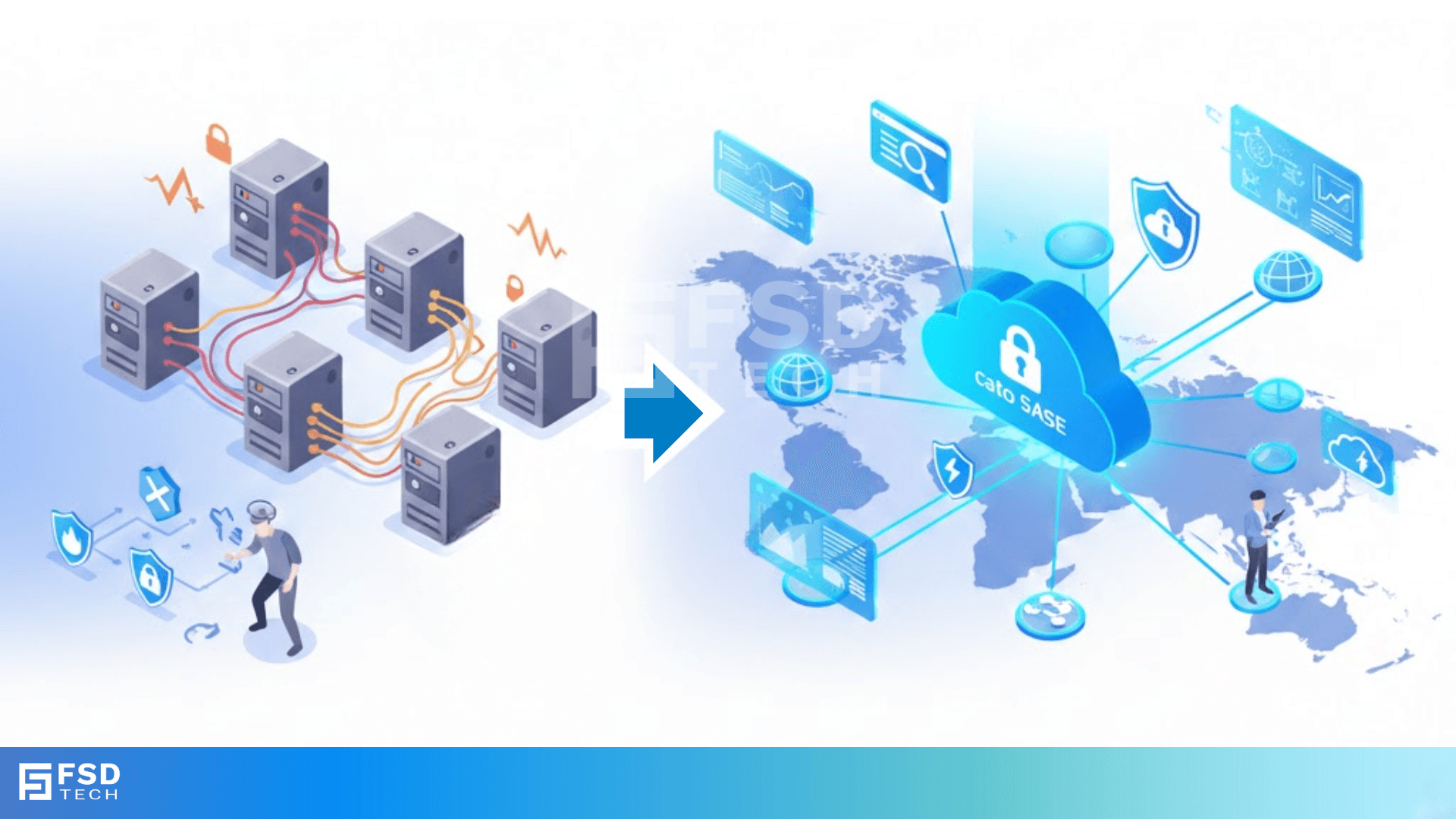
Cato ZTNA in Practice: Combining Identity, Device, and Context in One Policy Engine
Explore how UAE and Dubai enterprises implement Cato ZTNA using a unified policy engine that combines identity, device posture, and contextual signals—deliverin...
🕓 February 25, 2026











.png&w=3840&q=75)
.webp&w=3840&q=75)

