
Troubleshooting Device-Based Firewall Rules in Cato SASE
Learn how to troubleshoot device-based firewall rules in Cato SASE. This guide explains inventory checks, MAC visibility, rule logic, and posture enforcement.
🕓 March 13, 2026

Learn how to troubleshoot device-based firewall rules in Cato SASE. This guide explains inventory checks, MAC visibility, rule logic, and posture enforcement.
🕓 March 13, 2026

Understand the device identification limitations in Cato SASE Device Inventory and how UAE and Dubai enterprises design resilient device-aware security policies...
🕓 March 8, 2026
.webp&w=3840&q=75)
Learn why DHCP configuration is critical for device-based firewall enforcement in Cato SASE. Discover how UAE and Dubai enterprises improve device identificatio...
🕓 March 7, 2026

Explore how UAE and Dubai enterprises use Cato SASE TLS Inspection to improve device classification accuracy—enabling stronger device-aware WAN and Internet Fir...
🕓 March 4, 2026

Explore how UAE and Dubai enterprises reduce IoT attack surface using Cato SASE Internet Firewall policies—enforcing device-aware, least-privilege internet acce...
🕓 March 2, 2026
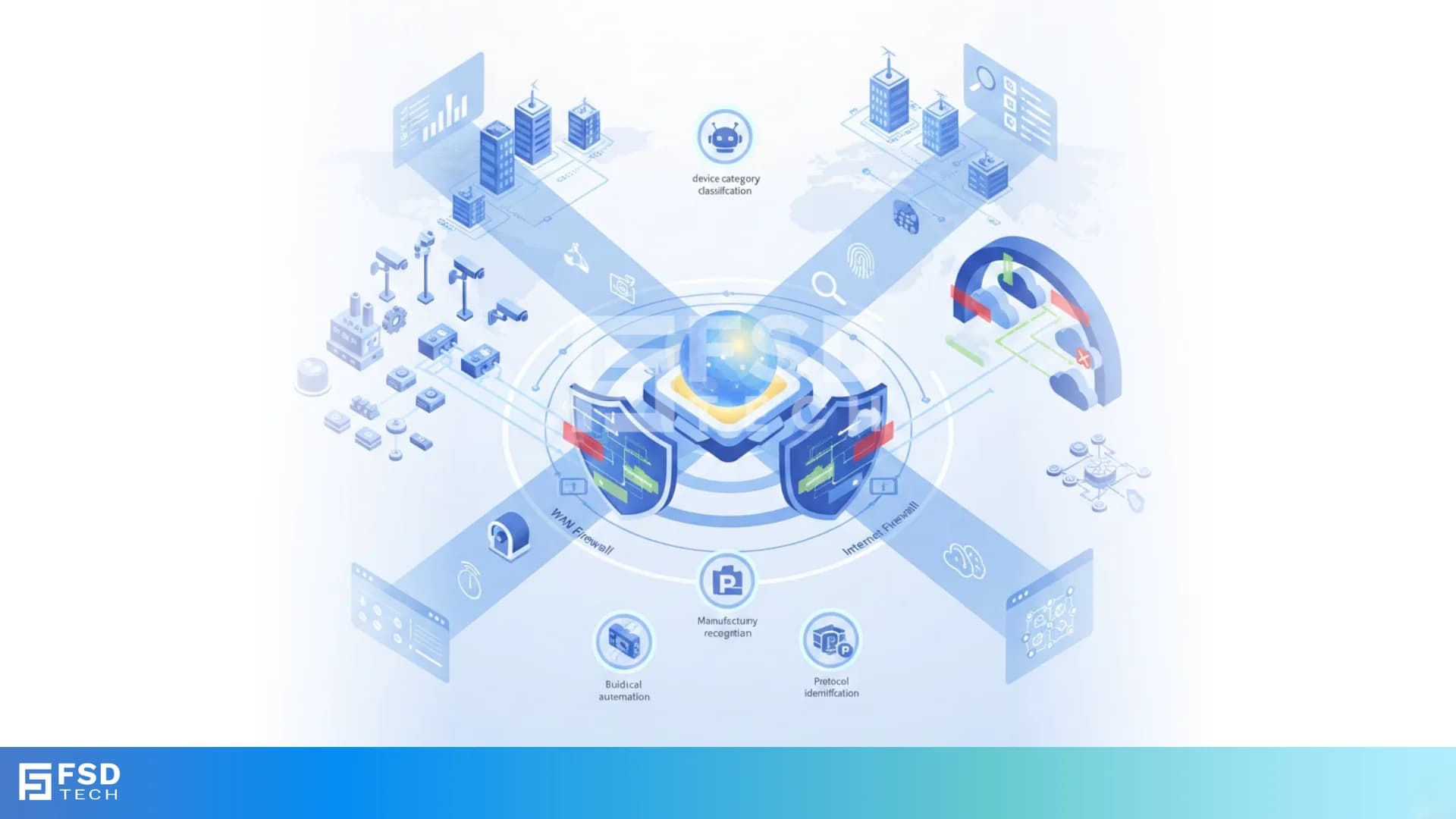
Explore how UAE and Dubai enterprises use Cato SASE to segment IoT and OT devices through WAN and Internet firewalls—enabling device-aware Zero Trust enforcemen...
🕓 March 1, 2026
.webp&w=3840&q=75)
Explore how UAE and Dubai enterprises use Cato SASE for agentless IoT and OT device discovery—achieving continuous visibility, Zero Trust alignment, and scalabl...
🕓 February 26, 2026

Explore how UAE and Dubai enterprises implement Cato ZTNA using a unified policy engine that combines identity, device posture, and contextual signals—deliverin...
🕓 February 25, 2026
.webp&w=3840&q=75)
Explore how UAE and Dubai enterprises use Cato SASE to manage unsupported or legacy clients through controlled Skip Check and Apply Check policies—balancing Zer...
🕓 February 24, 2026

Explore how UAE and Dubai enterprises use Cato SASE Advanced Posture to enable continuous device compliance and Zero Trust enforcement—reducing connection frict...
🕓 February 23, 2026