.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

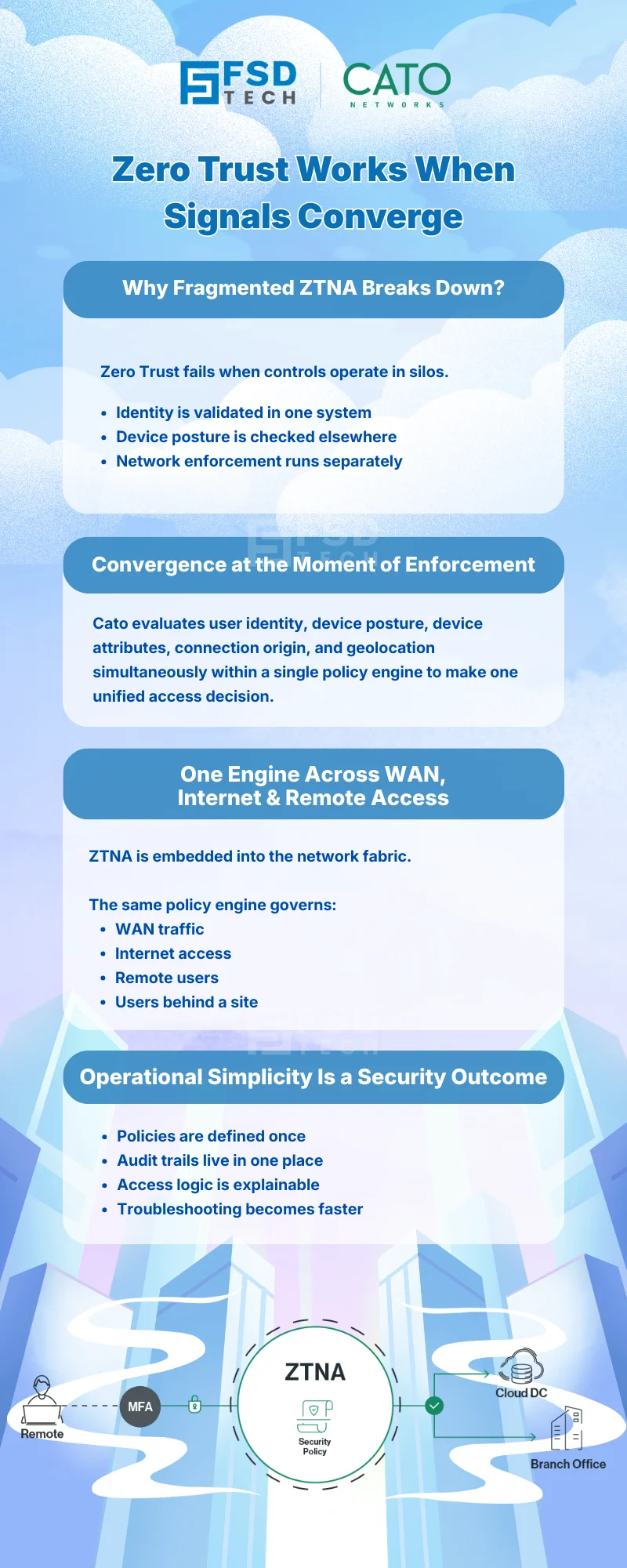
Zero Trust Network Access (ZTNA) is often described as a strategy.
What matters to enterprises, however, is execution.
The real value of ZTNA is not in individual controls—identity, device posture, location, or firewall rules—but in how these signals come together at the moment of enforcement.
Cato SASE operationalizes ZTNA by unifying identity, device context, and network enforcement into one coherent policy engine, applied consistently whether users are remote or working behind a site.
This blog explains how Cato delivers ZTNA in practice, not theory—and why this unified approach simplifies security while strengthening control.
Many Zero Trust implementations struggle because controls are fragmented:
This fragmentation leads to:
Cato takes a different approach: ZTNA enforcement happens at the network security layer, using a single policy engine that understands identity, device, and context together.
In Cato SASE, identity is established through:
Once identity is established:
This eliminates the traditional split between “remote access security” and “internal network security.”
Zero Trust does not stop at who the user is—it extends to what they are using.
Cato integrates device context through:
This allows policies to reflect real-world risk, such as:
Device context is evaluated at policy enforcement time, not bolted on afterward.
Cato ZTNA policies can incorporate multiple contextual dimensions simultaneously:
These signals are evaluated together, using clear and predictable logic, inside a single firewall rulebase.
The result: access decisions are precise, explainable, and consistent.
A defining advantage of Cato SASE is that ZTNA enforcement is not split across tools.
The same policy engine governs:
There is no need to:
This dramatically reduces policy sprawl and administrative overhead.
Security teams benefit from:
ZTNA in Cato is not an overlay—it is embedded into how the network operates.
This makes Zero Trust:
By combining identity, device, and context into a single policy engine, Cato enables organizations to:
ZTNA becomes a practical operating model, not a theoretical goal.
Need help implementing identity-, device-, and context-aware access in Cato SASE → Schedule your 30-minute Zero Trust strategy session now.
Cato SASE implements ZTNA by enforcing access decisions using a unified policy engine that evaluates identity, device posture, and contextual signals directly within WAN and Internet firewall rules.
In Cato SASE, identity is established by the Cato Client acting as an identity agent, allowing firewall policies to consistently enforce access based on user identity across all locations.
Cato SASE integrates Device Posture Profiles into firewall rules, enabling access decisions based on endpoint compliance alongside identity and network context.
No. Cato ZTNA applies the same identity- and device-aware policies to both remote users and devices connecting behind a site, ensuring consistent enforcement everywhere.
Cato SASE centralizes identity, device context, and network enforcement into a single policy engine, eliminating duplicated rules and reducing operational complexity.
Yes. Cato SASE allows organizations to incrementally tighten posture, device, and context requirements within the same policy framework as Zero Trust maturity increases.

Anas is an Expert in Network and Security Infrastructure, With over seven years of industry experience, holding certifications Including CCIE- Enterprise, PCNSE, Cato SASE Expert, and Atera Certified Master. Anas provides his valuable insights and expertise to readers.
Share it with friends!
share your thoughts