.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

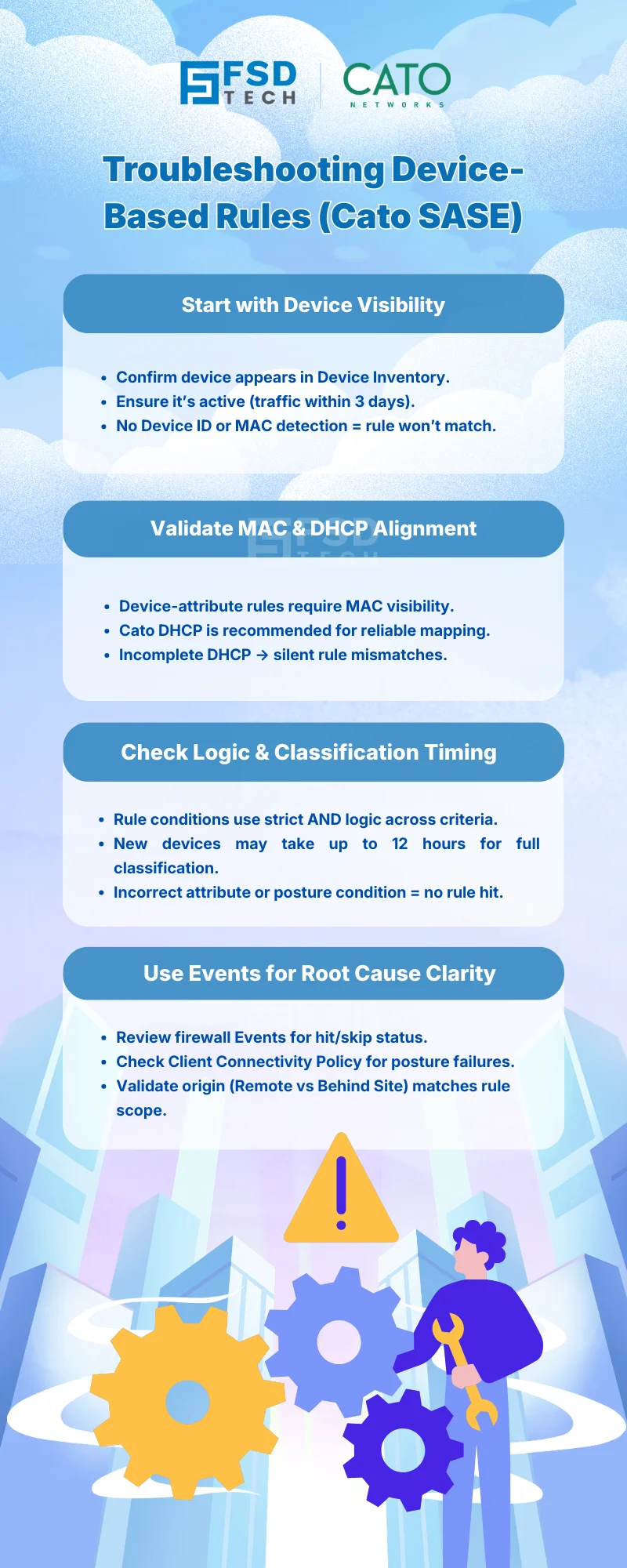
Device-based firewall enforcement is one of the most powerful capabilities in Cato Networks SASE.
It allows organizations to control access based on what the device is, where it connects from, and how it behaves — not just who the user is.
But when a WAN or Internet Firewall rule doesn’t hit, the issue is rarely “the firewall is broken.”
In almost every real-world case, the root cause is:
This blog walks through how to systematically troubleshoot device-based firewall rules in Cato SASE, using only official mechanisms and guidance.
Before troubleshooting, it’s critical to understand how Cato evaluates device-aware rules.
In both WAN and Internet Firewalls:
This evaluation model is precise - but unforgiving if misunderstood.
Device-based firewall rules only apply to devices that Cato can identify.
First checks:
If the device is missing from inventory:
This is expected behavior, not an error.
Cato explicitly documents that:
Firewall rules using Device Attributes are enforced only for devices whose MAC address was detected.
Common causes of MAC visibility issues:
Best practice (documented by Cato):
Without MAC visibility:
Device Inventory is behavior-based, not instantaneous.
Cato documents:
If a rule is applied immediately after onboarding:
This is normal and resolves as data matures.
If the device exists but the rule still doesn’t hit:
Check the Quick View in Device Inventory:
Known documented behaviors:
These conditions directly affect rule matching.
One of the most common issues is logical misalignment, not platform failure.
Key logic rules:
If a rule includes:
All must match simultaneously
Example:
Windows AND Device Profile A AND Remote user
If one fails → rule does not hit.
Examples:
But:
Multiple attribute types = AND
(OS = Windows AND Manufacturer = Dell)
Misunderstanding this is a frequent root cause.
Cato uses two different enforcement mechanisms, often confused:
If a rule uses Device Posture Profiles:
If the client is missing or unsupported:
Cato provides explicit visibility, not guesswork.
Check:
For posture enforcement:
Many rules fail due to origin mismatch.
Cato evaluates:
If a rule is scoped to:
But traffic originates:
The rule will never match - correctly.
Cato-aligned best practices include:
Having trouble with device-based firewall rules in Cato SASE? → Book a 30-minute Cato SASE architecture consultation with our experts.
Most commonly because the device is missing from Device Inventory, lacks MAC visibility, or fails one of the AND-based device conditions.
Only if the rule uses Device Posture Profiles. Rules based on Device Attributes do not require the Cato Client.
Because attributes may still be populating, detection latency applies, or the rule logic combines multiple conditions that are not all met.
By reviewing Client Connectivity Policy events in the Events page, which explicitly log posture failures.
Yes. Without MAC detection, Device Attribute–based firewall enforcement will not apply.
Yes. Cato documents these behaviors and provides design guidance to build resilient, layered policies.
No - because Cato provides clear inventory views, event logging, and documented logic, allowing teams to resolve issues systematically.
Device-based firewall enforcement in Cato SASE is deterministic, transparent, and auditable - when used as designed.
Most issues are not platform failures, but context misunderstandings.
By aligning policy design with how Cato actually identifies and evaluates devices, organizations gain:
That’s how Cato SASE turns device awareness into predictable control.

Anas is an Expert in Network and Security Infrastructure, With over seven years of industry experience, holding certifications Including CCIE- Enterprise, PCNSE, Cato SASE Expert, and Atera Certified Master. Anas provides his valuable insights and expertise to readers.
Share it with friends!
share your thoughts