.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
.webp&w=3840&q=75)
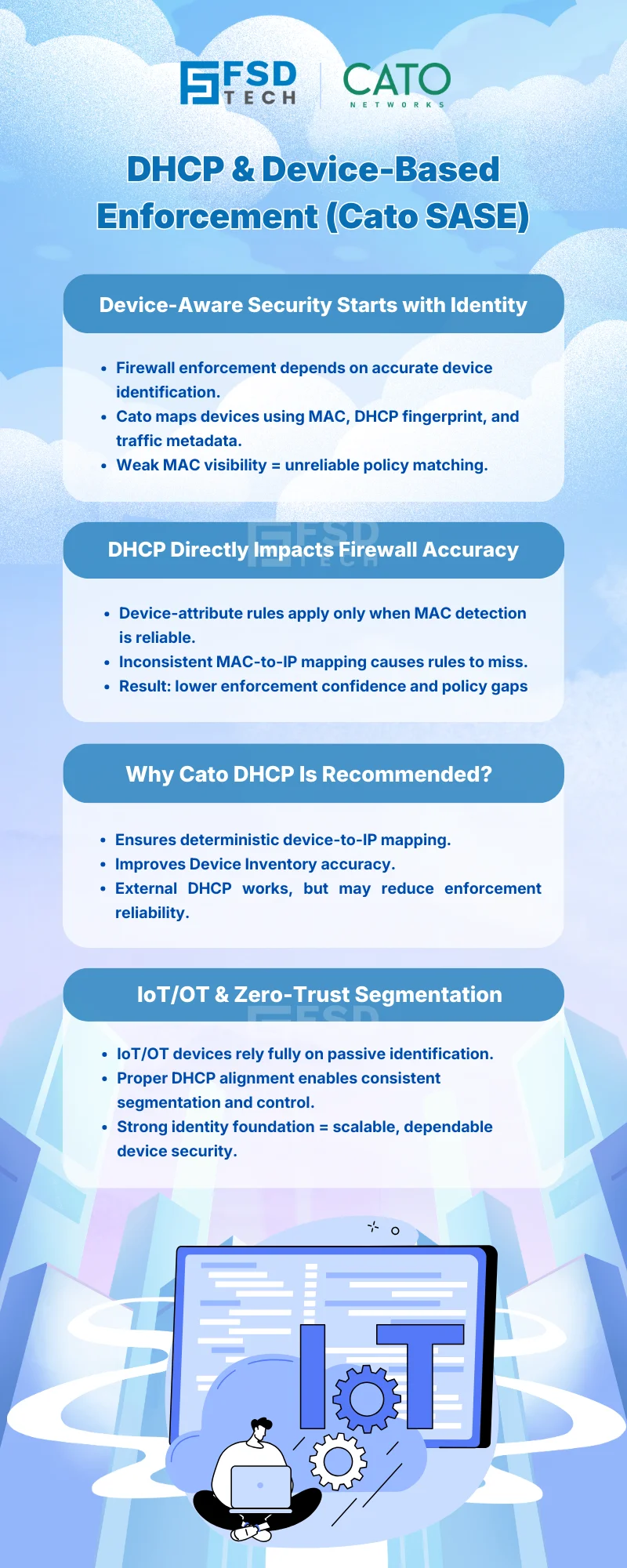
Most security discussions focus on policies: firewall rules, segmentation logic, and Zero Trust conditions.
But in device-aware security, enforcement quality depends on something far more foundational:
Can the platform reliably identify the device behind the traffic?
In Cato Networks SASE, that reliability is closely tied to DHCP configuration, because device-based firewall enforcement depends on accurate MAC address detection and device identity mapping.
This is why DHCP is not a “network hygiene detail” in Cato — it is a core dependency for device-aware policy enforcement.
Cato’s Device Inventory engine passively identifies devices by analyzing:
This data is then used to populate Device Attributes such as:
These attributes are what security teams reference in WAN and Internet Firewall rules when enforcing device-based controls.
If MAC address visibility is incomplete or inconsistent, enforcement becomes unreliable.
Cato officially documents a critical requirement:
Device Attribute–based firewall rules are enforced only for devices whose MAC address has been detected.
This means:
Then:
This is why DHCP configuration directly impacts policy accuracy, not just device visibility.
Cato supports multiple DHCP deployment models, but they are not equal from an enforcement standpoint.
When using Cato DHCP:
This is the recommended configuration when organizations intend to:
When using external DHCP servers or relay:
Cato documents this clearly as a limitation, not a bug.
For organizations using external DHCP, this requires:
IoT and OT devices typically:
For these environments:
Without consistent DHCP-based identification:
This makes DHCP configuration a security prerequisite for IoT/OT protection in Cato SASE.
Security teams often troubleshoot firewall rules assuming:
“The rule is wrong.”
In many cases, the rule logic is correct — the device identity is incomplete.
Common symptoms include:
Cato’s guidance is clear:
Before changing policy logic, validate device identification and DHCP behavior.
When DHCP is aligned with Cato’s enforcement model, organizations gain:
This turns device-aware security from a “best effort” approach into a repeatable operational model.
In Cato SASE, DHCP is not just about IP assignment.
It is:
Organizations that recognize this early avoid policy sprawl, enforcement gaps, and visibility blind spots as they scale.
Need help aligning DHCP, device discovery, and firewall enforcement in Cato SASE? → Schedule your 30-minute Zero Trust network design session today.
Because Cato SASE enforces Device Attribute–based firewall rules only for devices whose MAC addresses are reliably detected. DHCP plays a critical role in MAC-to-IP mapping and device identification accuracy.
Cato SASE does not require Cato DHCP, but it officially recommends using it when organizations rely on Device Attributes for firewall enforcement, as it provides more reliable MAC address detection.
Yes. When using external DHCP or relay, MAC visibility may be incomplete, which can cause device-based firewall rules to not match consistently.
Yes. IoT and OT devices rely entirely on passive identification. DHCP reliability directly affects how accurately these devices are classified and segmented in Cato SASE.
Admins should review the Device Inventory page to confirm MAC address detection and device attribution, then correlate with firewall rule hit counts and Events to confirm enforcement behavior.
Yes. Any firewall rule using Device Attributes — whether WAN or Internet — depends on accurate device identification, which is influenced by DHCP behavior.
Cato recommends using Cato DHCP, validating MAC address visibility, and designing device-based firewall policies only after confirming consistent device identification.
Strong device-aware security is not built only on policies — it is built on trustworthy identity foundations.
By aligning DHCP configuration with Cato’s Device Inventory and enforcement model, organizations ensure that every device-based policy decision is grounded in accurate, actionable context.
That’s how Cato SASE turns visibility into dependable control.

Anas is an Expert in Network and Security Infrastructure, With over seven years of industry experience, holding certifications Including CCIE- Enterprise, PCNSE, Cato SASE Expert, and Atera Certified Master. Anas provides his valuable insights and expertise to readers.
Share it with friends!
share your thoughts