.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

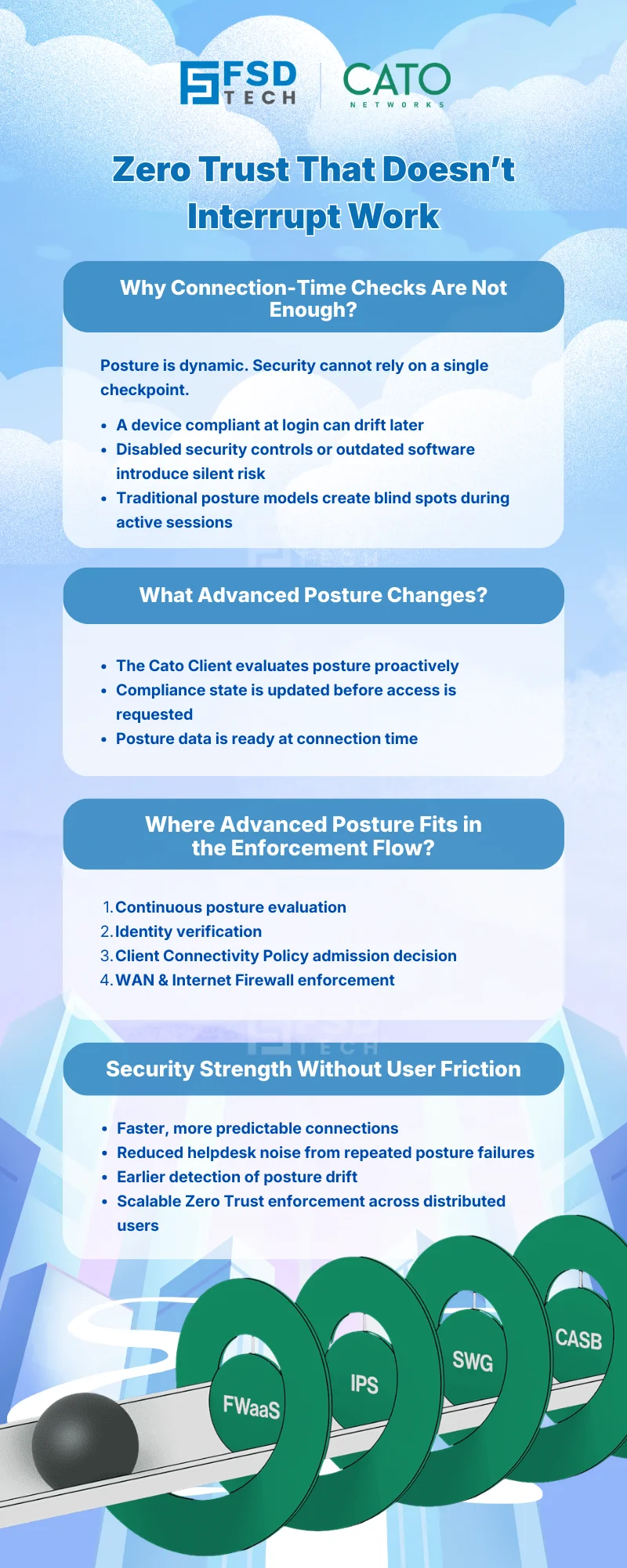
Zero Trust should not slow users down.
As organizations mature their Zero Trust strategies, a common challenge emerges: how to continuously verify device compliance without disrupting productivity. Frequent rechecks, slow connections, and repeated authentication prompts often create friction that users resent—and eventually try to bypass.
Cato SASE addresses this challenge with Advanced Posture in the Cato Client, enabling continuous endpoint compliance validation while keeping the user experience fast, predictable, and seamless.
This blog explains how Advanced Posture works, why it matters operationally, and how it strengthens Zero Trust enforcement without adding user friction.
Device compliance is not static.
An endpoint that is compliant at 9:00 AM may become non-compliant at 11:00 AM due to:
Traditional posture models rely heavily on connection-time checks, which create blind spots during active sessions. Once access is granted, posture drift can go undetected until the next reconnect—introducing risk without visibility.
Advanced Posture closes this gap by allowing compliance verification to continue beyond initial connection, ensuring Zero Trust remains enforced throughout the device lifecycle rather than at a single checkpoint.
Advanced Posture enables the Cato Client to evaluate device posture proactively and continuously, rather than only at the moment of connection.
This shifts posture enforcement from a reactive, connection-bound process to a pre-validated security state, aligning Zero Trust enforcement with real-world work patterns such as sleep, travel, and intermittent connectivity.
Without Advanced Posture:
With Advanced Posture enabled:
From the user’s perspective, access feels immediate.
From the security team’s perspective, enforcement remains uncompromised.
This balance is critical for long-term Zero Trust adoption.
Advanced Posture does not replace existing controls.
It strengthens and accelerates them.
This architecture ensures Zero Trust decisions are always based on current device state, not stale or delayed checks.
Advanced Posture delivers tangible operational value:
Fewer failed connections, retries, and user complaints.
Posture drift is detected earlier, not only at reconnect.
Security outcomes remain consistent across time, location, and network state.
Security teams can enforce stricter posture policies without degrading user experience as the organization grows.
Zero Trust is not defined by how strictly you block access—it’s defined by how consistently you verify trust conditions.
Advanced Posture supports this by:
This approach aligns security enforcement with how users actually work, rather than forcing security rituals onto every connection attempt.
Many Zero Trust initiatives fail not because of weak controls, but because of excessive friction.
Cato SASE avoids this trap by:
Advanced Posture ensures Zero Trust remains usable at scale, which is essential for enterprise-wide adoption and long-term success.
Build continuous compliance without slowing users down→ Book your 30-minute Cato SASE security consultation today.
Advanced Posture in Cato SASE allows the Cato Client to continuously evaluate device compliance even when the device is not actively connecting, ensuring posture data is available before access is requested.
Advanced Posture reduces connection delays in Cato SASE by pre-validating device compliance, allowing faster and smoother access without repeated posture checks during connection.
No. Advanced Posture in Cato SASE enhances existing device posture checks by running them proactively, while enforcement decisions are still applied through Client Connectivity Policy and firewall rules.
Advanced Posture strengthens Zero Trust in Cato SASE by maintaining continuous device compliance awareness, ensuring access decisions are always based on current posture, not outdated checks.
Yes. When enabled, Advanced Posture applies uniformly within Cato SASE environments, supporting consistent Zero Trust enforcement regardless of user location.
Advanced Posture allows Cato SASE to scale Zero Trust enforcement without increasing user friction, making continuous compliance practical across large, distributed workforces.

Anas is an Expert in Network and Security Infrastructure, With over seven years of industry experience, holding certifications Including CCIE- Enterprise, PCNSE, Cato SASE Expert, and Atera Certified Master. Anas provides his valuable insights and expertise to readers.
Share it with friends!
share your thoughts