.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

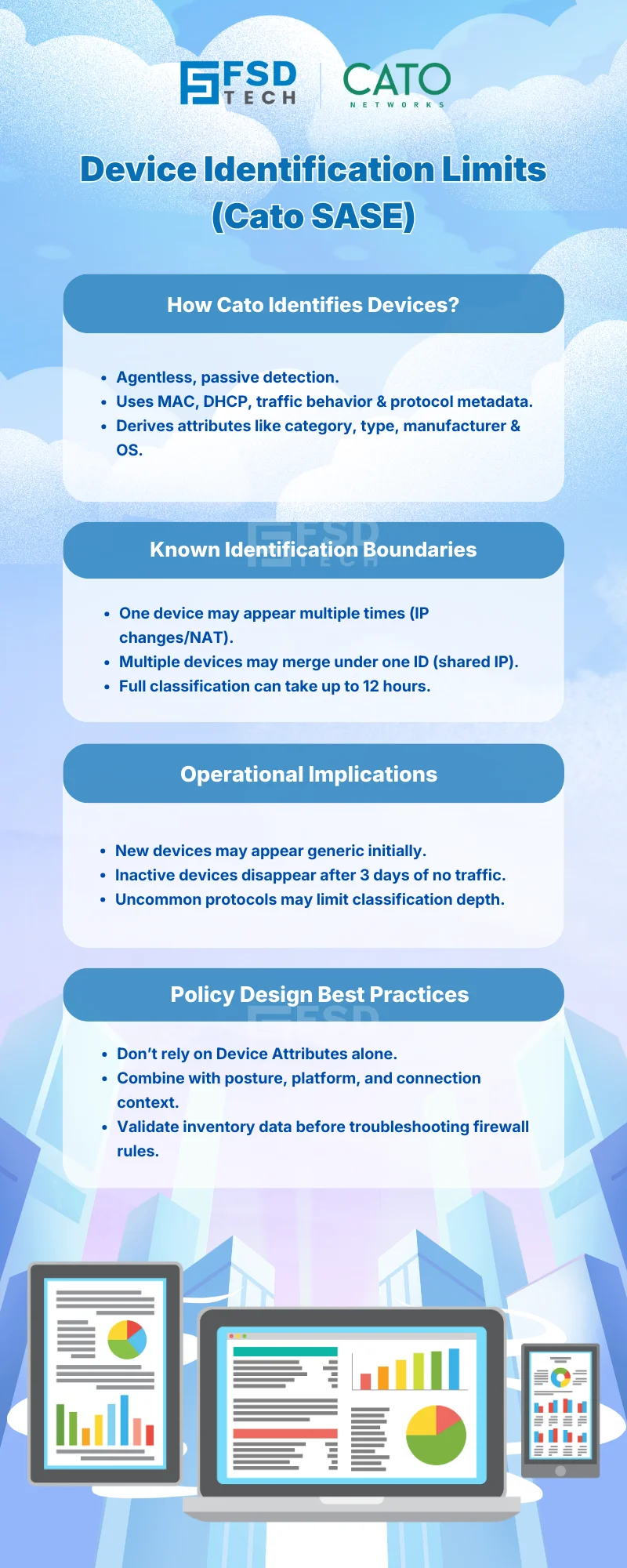
One of the strongest advantages of Cato Networks SASE is its ability to deliver broad, agentless visibility across IT, IoT, and OT environments using the Device Inventory engine.
However, like any large-scale, behavior-based detection system, device identification is not magic — it operates within documented technical boundaries.
Understanding these boundaries is not a weakness.
It is what allows security and network teams to:
This blog explains how Cato identifies devices, where limitations can occur, and how enterprises should account for them operationally.
Cato’s Device Inventory relies on passive detection, not agents or credentials.
Devices are identified and classified based on:
Using this data, Cato derives Device Attributes, including:
This approach allows Cato to discover devices you cannot install agents on, which is essential for modern enterprise networks.
Because identification is behavior-driven, not identity-asserted, certain scenarios can introduce ambiguity.
Cato documents these limitations clearly — and they are important to understand before building enforcement strategies.
A single physical device may appear multiple times in the Device Inventory when:
This can result in:
This does not indicate a security failure - it reflects how passive systems observe traffic over time.
Conversely, different devices may appear as one when:
In these cases:
Cato explicitly documents this as a known behavior of passive identification.
Device identification is not instantaneous.
Cato documents that:
This means:
Devices that:
Will not appear in the Devices page.
This prevents stale or inactive devices from cluttering operational views.
Accurate device identification depends on devices communicating using identifiable protocols such as:
Devices using uncommon or opaque protocols may:
This is expected behavior and documented by Cato.
Device Inventory limitations do not break security, but they do affect how policies should be designed.
Key implications:
Cato’s design assumes context-based decision making, not single-signal dependence.
Cato documentation and guidance consistently point to these best practices:
Device Attributes are ideal for:
They are not a replacement for user or client-based identity.
Stronger policies combine:
This reduces dependence on any single signal.
If a rule does not hit:
This avoids unnecessary policy rewrites.
Cato does not hide the realities of device identification — it documents them.
This transparency allows enterprises to:
In Zero Trust architectures, clarity beats false precision.
Need help designing reliable device-aware policies in Cato SASE? → Book a 30-minute Cato SASE architecture consultation with our experts.
Because passive detection can create multiple Device IDs when a device uses multiple IP addresses or changes network context within a short time window.
Yes. If multiple devices share an IP address within a 24-hour period, Cato may temporarily merge observations under one Device ID.
Cato documents that full identification and classification can take up to 12 hours, depending on traffic behavior.
Devices that have not generated WANbound or outbound traffic for three days are automatically removed from the active Devices view.
It can affect rules that rely exclusively on Device Attributes. This is why Cato recommends layered policy design and validating inventory data before adjusting rules.
No. They are an inherent characteristic of agentless, behavior-based discovery — and Cato documents them transparently so enterprises can design policies accordingly.
By combining Device Attributes with platform, posture, and connection context — and avoiding policies that depend on a single identification signal.
Device visibility at scale is not about perfection —
it’s about actionable accuracy with known boundaries.
By understanding how Cato Device Inventory works — and where its limits are — organizations gain the confidence to design resilient, scalable, and realistic device-aware security policies.
That’s how Cato SASE turns visibility into operational trust.

Anas is an Expert in Network and Security Infrastructure, With over seven years of industry experience, holding certifications Including CCIE- Enterprise, PCNSE, Cato SASE Expert, and Atera Certified Master. Anas provides his valuable insights and expertise to readers.
Share it with friends!
share your thoughts