.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
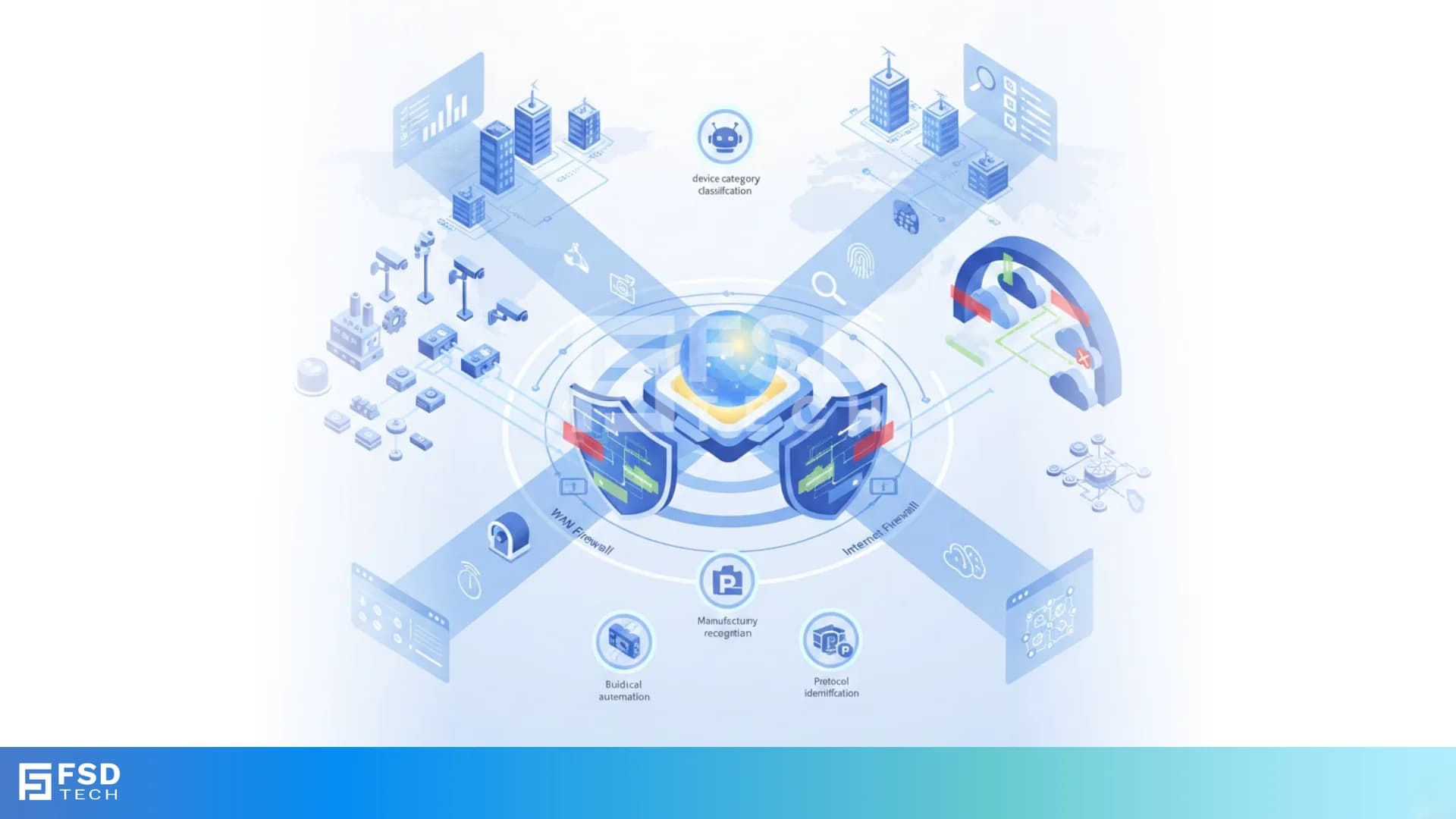
Cato Networks designed Cato SASE to solve a problem nearly every enterprise now faces:
how do you safely segment and control IoT and OT devices that you cannot install agents on-without adding more infrastructure or point products?
From building management systems and cameras to industrial controllers and medical equipment, IoT and OT devices now sit directly on corporate networks. They generate value - but they also expand the attack surface. Traditional network segmentation methods were never built for this scale or diversity.
Cato approaches this challenge differently: by applying device-aware policy enforcement directly inside the WAN and Internet firewalls, using passive discovery and unified policy control.
This blog explains how Cato enables practical IoT and OT segmentation—what traffic is controlled, where enforcement happens, and why this approach scales better than legacy network designs.
Unlike laptops or mobile endpoints, most IoT and OT devices:
This makes identity-based or client-based enforcement ineffective.
At the same time, these devices typically generate:
Effective segmentation must control both directions, without relying on VLAN sprawl, ACL complexity, or hardware firewalls at every site.
Cato uses passive device discovery as part of its Device Inventory service.
Instead of relying on agents, Cato identifies devices by analyzing:
Discovered devices are classified into attributes such as:
These attributes are then used directly in firewall policy enforcement.
The WAN Firewall controls traffic between users, sites, and internal resources across the Cato backbone.
With WAN Firewall rules, organizations can:
Result: segmentation that follows the device—not the physical network layout.
The Internet Firewall governs how devices access the public internet.
For IoT and OT environments, this enables:
This eliminates the need for static IP rules or device-specific firewall configurations.
Cato firewall rules apply clear, predictable logic:
This allows highly controlled segmentation without complexity.
Example logic:
Or:
Legacy IoT/OT segmentation depends on:
Cato replaces this with:
Segmentation becomes policy-driven, not topology-driven.
Cato provides visibility through:
Security teams gain confidence by knowing:
By using WAN and Internet firewalls for IoT and OT segmentation, organizations achieve:
Segmentation becomes a core security control, not an operational burden.
Simplify IoT and OT segmentation while strengthening Zero Trust enforcement.
Reserve your 30-minute Cato SASE strategy consultation now.

Cato uses passive device discovery through its Device Inventory service. Devices are identified and classified based on network traffic patterns, protocols, MAC addresses, and DHCP metadata. This allows segmentation policies to be enforced without installing agents or modifying the devices, which is critical for IoT and OT environments.
The WAN Firewall controls east–west traffic, such as communication between devices, sites, and internal applications.
The Internet Firewall controls north–south traffic, governing how devices access the public internet.
Together, they provide complete segmentation coverage for IoT and OT devices.
Yes. Using device-aware WAN Firewall rules, Cato can restrict IoT and OT devices so they communicate only with explicitly allowed systems. This prevents lateral movement into IT environments or between device categories, reducing the blast radius of a compromised device.
No. Cato enforces policies based on device identity and attributes, not IP addresses. This eliminates the need for static IP management and makes segmentation resilient to network changes.
Cato Internet Firewall rules can allow only specific destinations or categories for IoT devices while blocking all other internet access. OT devices that should not reach the internet can be completely restricted, reducing exposure to external threats.
Administrators can validate enforcement through:
These views provide clear evidence of which policies are applied and which traffic is allowed or blocked.
VLAN-based segmentation depends on physical topology, manual configuration, and ongoing maintenance.
Cato’s approach is policy-driven and centralized, enabling segmentation that scales across sites, users, and devices without increasing operational complexity.
Zero Trust requires continuous validation and least-privilege access.
By enforcing device-aware segmentation at the firewall level—regardless of location—Cato ensures that IoT and OT devices can access only what they are explicitly allowed, aligning directly with Zero Trust architecture principles.

Anas is an Expert in Network and Security Infrastructure, With over seven years of industry experience, holding certifications Including CCIE- Enterprise, PCNSE, Cato SASE Expert, and Atera Certified Master. Anas provides his valuable insights and expertise to readers.
Share it with friends!
share your thoughts