.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
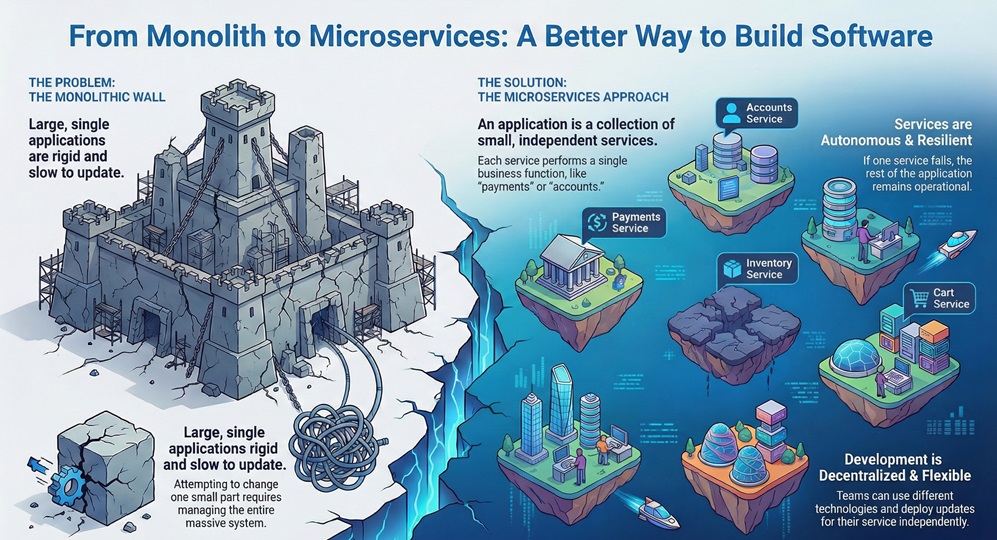
If you build or manage modern applications, you know the pressure is constant. You need systems that scale instantly and resist failure. Perhaps you currently manage a massive, single application that slows down every time you try to update one small part.
This scenario is common and often leads development teams to search for a better way to structure their software. The solution many leading companies choose focuses on breaking that giant application into smaller, manageable pieces. This approach is what we call Microservices Architecture.
Microservices Architecture is nothing but a special way to build software. It takes a single, large application and breaks it into many independent services. Each service performs one specific business function. For example, one service handles customer accounts. Another service manages the shopping cart. A third service processes payments. This separation makes the entire system easier to develop, test, and deploy. You gain flexibility and speed when you adopt a Microservices Architecture.
Let us now discuss the fundamental question: What Microservices Architecture provides that traditional systems do not? It offers independence and resilience. Imagine a wall made of separate bricks instead of one huge slab of concrete. If one brick breaks, the rest of the wall remains standing. Similarly, if one service fails in a Microservices Architecture, the rest of your application continues to function smoothly. This isolation is a critical feature that modern digital platforms require.
We can understand what are microservices in software by focusing on their key characteristics. Each microservice is an independent application that communicates with others over a network. The defining principles of architecture of microservices ensure high performance and agility for development teams.
Microservices can be understood as small, autonomous business services. They perform a single function and manage their own data storage. This design choice provides a key advantage: decentralized governance. This means different teams can use different programming languages and databases suitable for their specific service.
To understand the best microservices architecture, you must know what defines a microservice. These key characteristics ensure that your application remains flexible and robust.
Microservices possess the following core traits:
Therefore, when you build a system using Microservices Architecture, you build a series of small, cooperating components instead of one large block.
Now, the question arises: Why Microservices Architecture has become the standard for companies like Netflix and Amazon? The answer lies in the benefits it provides for continuous delivery and rapid development. Microservices Architecture ensures a faster time to market for new features.
Due to the independent nature of the services, teams can work concurrently on different parts of the application. This efficiency significantly speeds up the development lifecycle. This architecture also directly addresses the issues that arise when a single application becomes too large and difficult to manage.
Also Read: What is Application Whitelisting in Cybersecurity?
Implementing a robust Microservices Architecture provides several crucial advantages for your business.
Taking into account these benefits, it is clear why adopting Microservices Architecture allows companies to innovate and adapt faster than their competitors.
To fully grasp the power of Microservices Architecture, we must contrast it with the traditional monolithic vs microservices approach. The monolithic structure is the conventional way applications have been built for decades.
A Monolithic application is built as a single, indivisible unit. All components, including the user interface, business logic, and data access layers, reside in one massive codebase. When you need to update one small function, you must rebuild and redeploy the entire application.
| Basis for Comparison | Monolithic Architecture | Microservices Architecture |
|---|---|---|
| Structure | Single, indivisible unit. | Collection of small, autonomous services. |
| Deployment | Requires deploying the entire application. | Each service deploys independently. |
| Scalability | Must scale the entire application. | Scales individual services as needed. |
| Technology | Fixed to one technology stack. | Allows multiple technologies (polyglot). |
| Fault Tolerance | Failure in one component can crash all. | Failure is isolated to one service. |
| Development | Slows down as the codebase grows large. | Remains agile and fast regardless of size. |
Microservices Architecture overcomes the limitations of the monolithic approach. While monolithic applications start simple, they become increasingly complex over time. They tend to slow down development velocity.
Also Read: What is Neuromorphic Computing? Future of AI & Hardware
Let us now list the specific distinctions in the monolithic vs microservices debate that favor the modern approach.
Therefore, building a system with Microservices Architecture helps your teams move faster and manage complexity better.
Understanding how microservices work is essential to implement them correctly. At its core, a microservice is a process that runs independently. It has a lightweight mechanism for communication with other services.
In simple words, the way Microservices Architecture functions is by replacing internal method calls (common in monolithic systems) with network calls. This means two separate services must be able to send data back and forth reliably and efficiently.
Now, the question is: how microservices communicate with each other? Since they run as separate processes, they rely on two main communication styles: synchronous and asynchronous.
1. Synchronous Communication
In this method, the client service sends a request to the server service and then pauses. It waits for the server service to process the request and send a response back.
However, this method creates a tight coupling. If the server service is down, the client service must wait, which can cause cascading failures.
2. Asynchronous Communication
This is the preferred style for building resilient Microservices Architecture. The client service sends a message and continues its work without waiting for an immediate response. It relies on a message broker or queue.
By choosing the right communication method, you ensure that how microservices communicate aligns with the necessary reliability and performance standards for your application.
Also Read: What is the Cyber Kill Chain? Critical Cybersecurity Model
A standard Microservices Architecture Diagram always includes an API Gateway. The API Gateway serves as the single entry point for all client requests.
The API Gateway is nothing but a dedicated service that accepts all requests from users (web browser, mobile app) and then routes them to the appropriate back-end microservice. It also handles essential functions like security, rate limiting, and load balancing. This component helps to hide the complexity of the internal Microservices Architecture from the outside world.
To actually build and run Microservices, developers rely on specific software frameworks and platforms. These tools provide the necessary features for service discovery, configuration, and inter-service communication.
The technology you choose dictates much of the implementation process. Let us explore some common and powerful platforms for Microservices Architecture.
Spring Boot is perhaps the most popular framework for building Java-based Microservices. Java is a mature language, and the Spring ecosystem provides all the tools developers need for a complete Microservices Architecture.
Spring Boot Microservices simplifies the setup of Java applications. It ensures that developers can focus purely on business logic rather than on complex configuration. Due to its robustness and extensive community support, it remains a common choice for enterprise-level applications. This platform assists in quickly creating production-ready, standalone Spring applications. It helps teams manage services, handle security, and integrate easily with cloud platforms.
Microsoft's .NET platform offers strong tools for building Microservices Architecture. Specifically, Microservices in .NET use .NET Core or the newer .NET framework. This platform is known for its high performance and robust developer tooling.
The .NET ecosystem provides excellent integration with Microsoft Azure cloud services. This makes it a perfect choice for organizations committed to the Microsoft stack. Using C#, developers can create high-speed, scalable services. The platform also includes built-in features for handling networking and serialization, which are essential for how microservices communicate.
For applications requiring speed, high concurrency, and a lightweight footprint, Microservices in Node JS are an excellent option. Node.js uses JavaScript, a language that allows developers to use the same language for both the front-end and back-end services.
Node.js is an efficient choice for creating I/O-intensive microservices. It is based on a non-blocking, event-driven model that handles many simultaneous connections without needing high memory. This efficiency allows Node.js services to deliver fast response times, which is a vital factor for achieving the best microservices architecture performance.
A well-designed Microservices Architecture requires careful planning and the use of established patterns. Understanding these concepts helps you avoid common pitfalls when moving from a monolithic application.
A proper Microservices Architecture Diagram is a visual map. It shows all the services, the API Gateway, the service discovery component, and the message broker. This map helps teams understand the flow of data and the dependencies between services.
Successful implementation relies on applying proven design patterns. These patterns solve recurring problems in distributed systems.
Managing transactions is often considered one of the hardest parts of Microservices Architecture. Since each service has its own data, a simple process like placing an order requires coordination across the Order Service, the Inventory Service, and the Payment Service.
The Saga pattern is used to coordinate these complex business workflows. It is to be noted that adopting Microservices Architecture means accepting the complexity of distributed transactions. This is a trade-off for the gains in scalability and fault isolation.
Microservices Architecture changes large applications into small, independent services that teams can build, update, and scale separately. This approach brings faster development, better fault isolation, easier maintenance, and the freedom to use the best tools for each job. Although it adds some complexity in operations and communication, the gains in speed, reliability, and flexibility make it worthwhile for most growing systems.
Companies that adopt microservices stay agile and respond quickly to new needs. Moving to this style is a practical step toward building software that lasts and performs well under real-world pressure.
Proactive Microservices Contact our team

· Fundamental Shift in Development: Microservices Architecture moves development away from large, rigid monolithic applications. It focuses instead on creating small, flexible, and powerful services.
· Enhanced Team Autonomy and Speed: This architectural shift provides development teams with the autonomy they need. This enables them to innovate quickly and meet the constantly evolving demands of the business.
· Targeted Scaling and Efficiency: Microservices allow you to scale specific business functions as required. You can choose the optimal technology stack for each service, improving resource efficiency.
· Guaranteed Platform Resilience: The architecture ensures that a single service failure does not crash the entire platform. This fault isolation is vital for maintaining stability in today's digital world.
· Alignment with Business Goals: Transitioning to a true Microservices Architecture is necessary for organizations seeking adaptability and responsiveness. It ensures that technology actively serves, rather than limits, your strategic business goals.
The primary difference refers to the structure and deployment. A Monolithic application is one codebase, deployed as a single unit. In contrast, Microservices Architecture comprises many small, independent services, each deployed separately. This fundamental difference dictates the team structure, scalability, and overall development speed.
Microservices are typically deployed using containerization technologies like Docker and orchestration platforms like Kubernetes. Kubernetes facilitates service discovery, load balancing, and auto-scaling, which are essential for managing a complex Microservices Architecture.
The most critical challenge is often the increased operational complexity. The transition requires new skills for monitoring, logging, and tracing across dozens or hundreds of services. How microservices communicate with each other also requires careful management of network latency and distributed transactions.
Yes, they can be written in different languages—a concept known as polyglot persistence or programming. This is a feature of the Microservices Architecture. It allows teams to choose the language (what is microservices in Spring Boot, what are microservices in Node JS, etc.) that is most efficient for that specific service’s function.
Service discovery is nothing but a mechanism that allows services to find the network location (IP address and port) of other services. It is needed because services in a Microservices Architecture are dynamic, meaning they frequently scale up or down. Service discovery ensures communication remains effective even when service locations change constantly.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts