.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
.png&w=3840&q=75)
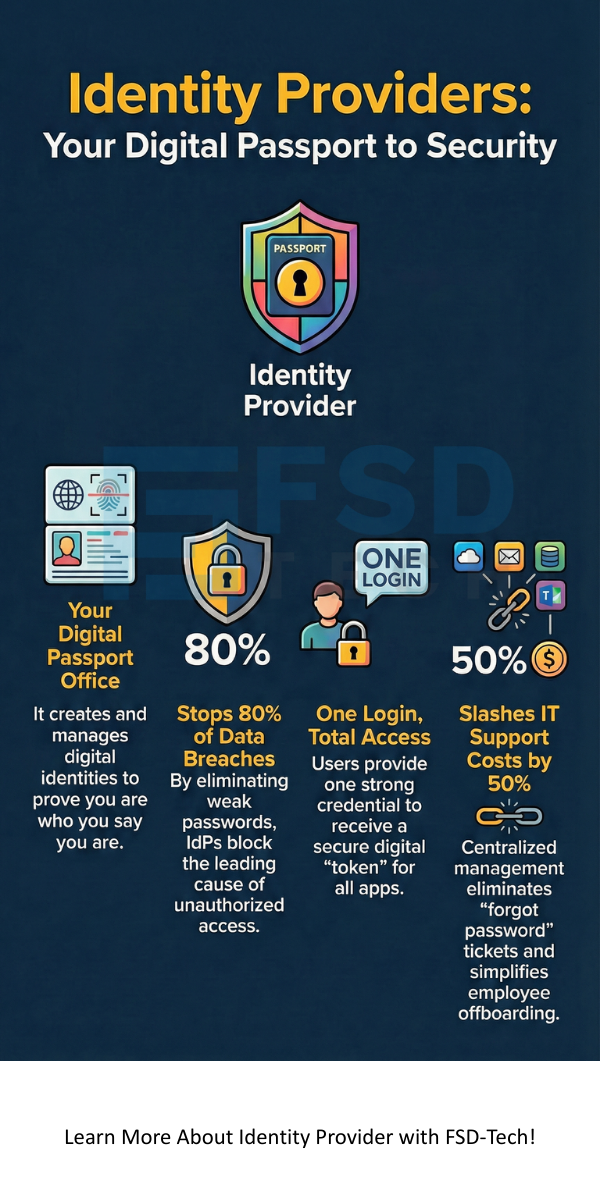
Have you ever wondered how you can log into ten different work apps without typing your password ten times? It feels like magic, but it is actually the work of an Identity Provider. In the tech world, we call this an IdP. Think of it as a digital passport office. It proves you are who you say you are so you can enter different digital "countries" or applications safely.
But why should you care about how these systems work? To be honest, the way we handle digital identities has changed fast. We no longer just sit in an office behind a physical firewall. We work from home, cafes, and airports. This shift makes the Identity Provider the new perimeter of security. It is the heart of a Zero Trust strategy, where we trust no one until they prove their identity.
An Identity Provider is a system that creates, maintains, and manages digital identity information. It tells other programs that a user is valid. When you try to access a cloud app, the app asks the IdP, "Hey, do I know this person?" The IdP checks your credentials—like a username or a thumbprint—and sends back a "yes" or "no."
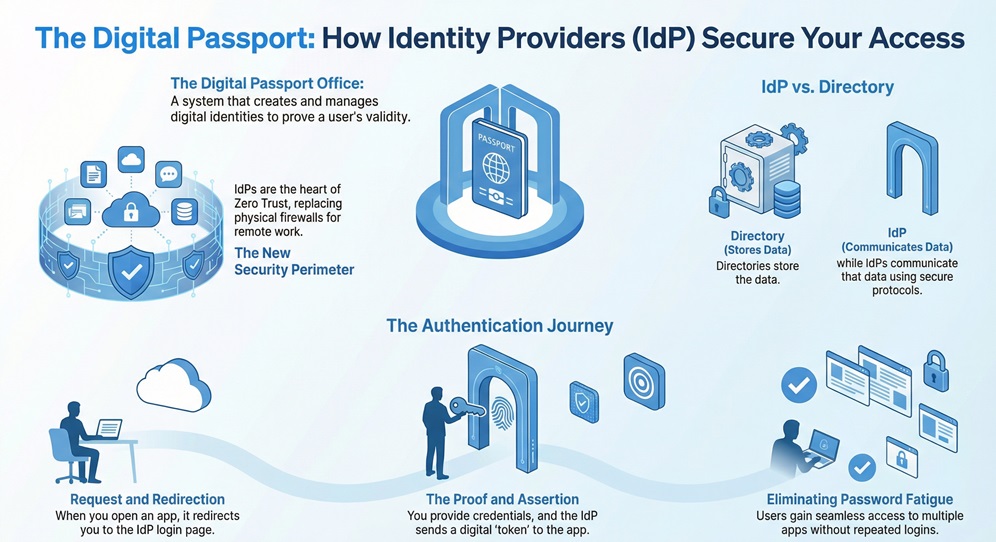
In my experience, people often confuse an IdP with a simple directory. While they are related, they aren't the same. A directory, like Active Directory (AD), holds the data. The Identity Provider is the service that actually communicates that data to other platforms using secure protocols.
The process is like showing your ID at a concert. You don’t give the security guard your birth certificate and social security card. You show them a state-issued license. They trust the state, so they trust you.
Does this sound familiar? You likely use this every day without realizing it. It saves time and stops "password fatigue."
Also Read: Threat Actors: Who is Behind Your Cyber Security Risks?
We've all been there—trying to remember if the password had an exclamation point or a capital "Q." When companies don't use a central Identity Provider, employees make weak passwords. This is a huge risk. An IdP allows for Single Sign-On (SSO), which means you only need one very strong password (and hopefully a second factor) to get everywhere.
In a Zero Trust world, the Identity Provider is king. It doesn't just check your password once. It looks at your location, your device health, and the time of day. If you usually log in from New York but suddenly appear in London five minutes later, the IdP will stop you.
Roughly 80% of data breaches involve weak or stolen credentials. By using an IdP, you shrink the "attack surface." You give hackers fewer doors to knock on.
Why do IT teams love these systems? It isn’t just about security; it’s about making life easier for everyone.
To talk to different apps, an IdP needs a common language. You might see these acronyms in your settings.
SAML (Security Assertion Markup Language)
This is the "old reliable" of the bunch. It uses XML to pass data between the Identity Provider and the service provider. It is very common in corporate tools like SAP Single Sign-On.
OIDC (OpenID Connect)
This is a newer, lighter language. It sits on top of OAuth 2.0. If you use "Sign in with Google" on a website, you are likely using OIDC. It’s great for mobile apps.
Identity Provider in the Cloud vs. On-Premise
Should you keep your IdP in your own basement or put it in the cloud? In my view, the cloud is winning for a reason.
On-Premise IdPs give you total control. However, they are hard to maintain. You have to handle updates, hardware, and security patches yourself.
Cloud IdPs (like Okta or Azure AD) are "Identity as a Service" (IDaaS). They scale automatically. If you have 10 employees today and 1,000 tomorrow, the cloud handles it. Plus, they stay updated against the latest threats without you lifting a finger.
Also Read: What is the Shared Responsibility Model and Why Does it Matter?
For big businesses, connecting an IdP to SAP is a game changer. SAP Identity Management works with your IdP to make sure permissions are right. When the Identity Provider confirms a user, SAP then checks exactly what that user is allowed to do inside the finance or HR modules.
This creates a "Single Point of Truth." You don't have different lists of users in different places. Everything stays in sync.
Is it all sunshine and rainbows? Not quite. Here is the thing: if your Identity Provider goes down, no one can work. It is a "single point of failure."
This is why choosing a provider with high availability is a must. You also need to ensure your IdP supports Multi-Factor Authentication (MFA). A password alone is no longer enough. Are you using an authenticator app or a physical key? You should be.
Don't just pick the first name you see. Think about your specific needs.
We are moving toward a "passwordless" future. Your Identity Provider will soon rely entirely on biometrics (like FaceID) and hardware signals. This will make things even faster and safer.
Picture this: You walk up to your laptop, it sees your face, checks your phone's location, and opens all your apps. No typing. No stress. That is the goal of a modern IdP.
At our core, we believe that security should never get in the way of great work. A strong Identity Provider balances safety with a smooth experience. It protects your data while letting your team move fast. We focus on building trust through technology. If you want to secure your future, start with how you identify your people.
The IdP holds the user info and proves identity. The Service Provider is the app (like Gmail or Salesforce) that provides the service once the IdP gives the green light.
Yes, some companies use "identity federation." This links multiple IdPs so users from different organizations can work together safely.
Not exactly. SSO is the benefit you get. The Identity Provider is the engine that makes SSO happen.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts