.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
The Cyber Kill Chain framework refers to the process an intruder uses to attack your network. By understanding the attacker’s approach, you can create effective defenses and stop an intrusion before it causes serious damage.
The Cyber Kill Chain is nothing but a structured methodology. It helps security teams analyze attacks, improve system defenses, and prioritize their security investments. This approach significantly enhances the ability to predict and prevent cyber-attacks, moving your team from a reactive to a proactive security stance.
The name “kill chain” originally describes the structure of an attack. In simple words, it refers to the chain of steps an adversary takes to achieve their objective. Now, the question arises: What is the Cyber Kill Chain in cybersecurity?
In cybersecurity, the Cyber Kill Chain is a model that breaks down the attack process into distinct, observable stages. This framework, developed by Lockheed Martin, gives defenders specific points where they can stop an attack. You, the reader, need to understand each phase to effectively protect your organization.
It is important to note that Lockheed Martin developed the Cyber Kill Chain framework. They formalized this model to improve the identification and prevention of cyber intrusions.
The original model acts as a defense-oriented view of the steps an external attacker takes. This understanding allows security teams to identify key indicators of compromise (IOCs) and prevent the attack from progressing.
The Cyber Kill Chain model provides a clear, sequential path. An adversary must successfully complete this path to execute an attack on a target network. By breaking the attack into stages, you can focus on disrupting the chain at any point. Successfully disrupting the chain means you stop the attack.
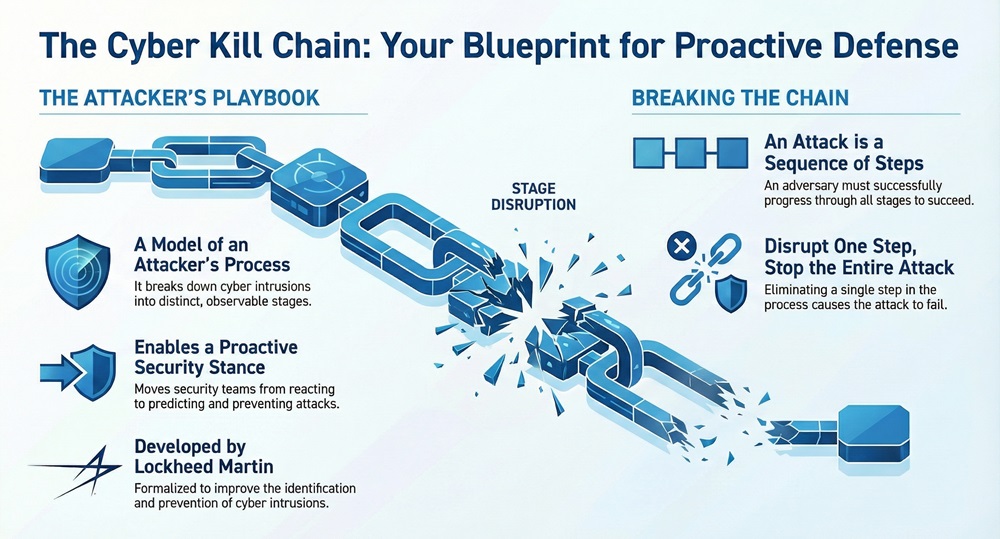
The entire Cyber Kill Chain methodology relies on the principle that the attacker must progress through all stages. Therefore, if you, the defender, eliminate a single step, the entire attack fails. This is a very powerful concept for building resilient security strategies.
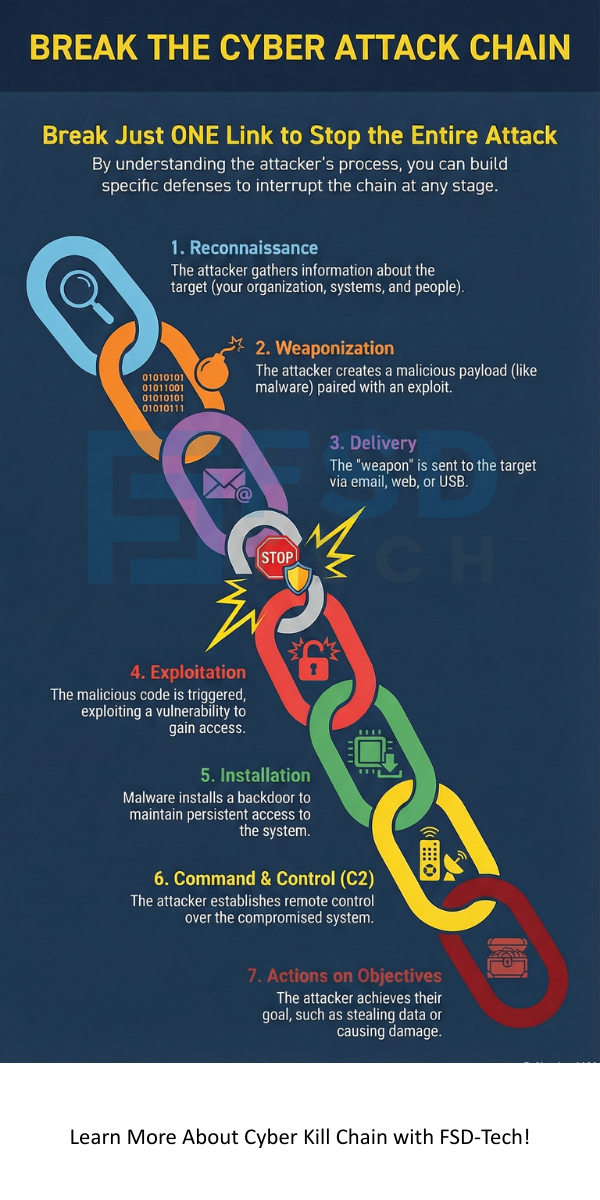
Let us now discuss the seven essential Cyber Kill Chain stages.
The original Cyber Kill Chain process consists of seven distinct steps. Each step plays a vital role in the attacker's journey to infiltrate and compromise a target system. Cyber Kill Chain steps are sequential and provide a roadmap for detection and mitigation.
The following are the seven Cyber Kill Chain phases that you need to know:
Reconnaissance is the first step in the Cyber Kill Chain process. The attacker gathers information about the target before the attack. This stage aims to collect data on the target's organization, systems, and personnel.
Information gathering activities include:
The attacker uses this information to formulate their attack strategy.
Once the attacker gathers sufficient information, they move to the Weaponization stage. Weaponization refers to the coupling of a malicious payload with an exploitable vulnerability.
The attacker creates a weapon suitable for the target environment. This weapon typically comprises two main parts:
The combination of exploit and payload creates the ultimate cyber weapon.
The Delivery phase focuses on transmitting the cyber weapon to the target. This step means using various communication channels to send the malicious package to the victim’s environment.
Common Delivery methods include:
Successful Delivery places the weapon within the target’s network perimeter.
Exploitation is the phase where the attacker triggers the vulnerability within the system. After the weapon is delivered, the Exploitation step executes the exploit code.
This action allows the attacker to gain unauthorized access to the target system. The exploit code uses a weakness in the target's software or operating system. For example, the exploit may leverage a buffer overflow to execute arbitrary code.
Successful Exploitation creates a breach, allowing the attacker to continue the Cyber Kill Chain steps.
After successful Exploitation, the attacker performs the Installation phase. Installation refers to placing persistent access mechanisms on the compromised system.
This step ensures the attacker can maintain control over the system even after a restart or patched vulnerability. The attacker typically installs one or more of the following:
This guarantees the attacker a firm foothold in the network.
The Command and Control (C2) phase is where the installed malware opens a two-way communication channel. The attacker uses this channel to control the compromised system remotely.
The C2 communication allows the attacker to:
The compromised system is now under the attacker's direct control.
The final stage of the Cyber Kill Chain is the Actions on Objectives. In this phase, the attacker achieves their ultimate goal. The goal varies depending on the attacker's intent.
The attacker utilizes the established Command and Control channel to:
Successfully completing this stage signifies a successful attack.
Also Read: What is Phishing Simulation? Benefits & Best Practices
Understanding the Cyber Kill Chain framework becomes easier with practical examples. The model provides a checklist for security teams to analyze any intrusion attempt.
Let us consider a common Cyber Kill Chain example involving spear-phishing.
| Kill Chain Stage | Attacker’s Action | Defender’s Goal (Mitigation) |
|---|---|---|
| Reconnaissance | Attacker finds an employee's email and their system type. | Blocking external scanning; Monitoring external information sources. |
| Weaponization | Attacker creates a document with an embedded exploit for the target’s PDF reader. | Using secure operating systems; Employing patch management to eliminate vulnerabilities. |
| Delivery | Attacker sends the malicious document via a targeted email. | Using email filters to block suspicious attachments; Implementing Cyber Kill Chain security training for employees. |
| Exploitation | The employee opens the attachment, triggering the exploit code. | Deploying an Intrusion Prevention System (IPS) to detect exploit attempts; Using application whitelisting. |
| Installation | Malware installs a backdoor to guarantee future access. | Using Endpoint Detection and Response (EDR) to prevent unauthorized installations; Monitoring registry and file system changes. |
| Command & Control | The backdoor connects to the attacker’s external server. | Blocking suspicious outbound network traffic; Analyzing DNS and network logs for C2 beacons. |
| Actions on Objectives | Attacker searches for and steals intellectual property files. | Implementing network segmentation; Monitoring data loss prevention (DLP) alerts; Applying the Cyber Kill Chain methodology to stop lateral movement. |
By analyzing the attempt through this structured lens, security teams can pinpoint exactly where they failed and implement stronger controls at those specific Cyber Kill Chain steps.
Also Read: What is Robotic Process Automation (RPA)?
The Cyber Kill Chain framework is often compared to the MITRE ATT&CK framework. While both help defend against attacks, they serve different primary purposes.
| Basis for Comparison | Cyber Kill Chain | MITRE ATT&CK |
|---|---|---|
| Focus | High-level attack progression (The What and When of an attack). | Specific TTPs (Tactics, Techniques, and Procedures) (The How of an attack). |
| Structure | Sequential, linear phases (must follow in order). | Non-linear, matrix of tactics and techniques. |
| Level of Detail | General, focused on external intrusion stages. | Highly granular, mapping specific adversary actions. |
| Purpose | To interrupt the attack at any phase. | To emulate and detect specific adversary behavior. |
| Use Case | Incident response and high-level defense planning. | Threat intelligence, hunting, and security control validation. |
While autonomous investment is unrelated to national income, induced investment is positively related to national income, the Cyber Kill Chain provides a foundational view of an attack's progression. On the other hand, MITRE ATT&CK offers a deeper catalog of the specific methods (TTPs) used within those phases. Both are essential tools in a complete cybersecurity strategy.
Understanding the Cyber Kill Chain allows your team to stop thinking reactively and start acting proactively. By focusing your resources on defense across all Cyber Kill Chain phases, you create a resilient environment that reduces the chances of a successful intrusion.
If you are serious about protecting your digital assets, learning to map your security controls against the Cyber Kill Chain stages is essential. This crucial methodology ensures you meet and exceed the current demands of a dynamic threat environment.
We at FSD-tech focus on implementing robust, multi-layered security solutions that directly target each step of the Cyber Kill Chain process, guaranteeing a strong line of defense for your critical infrastructure. Contact us today to learn how our tailored security services can help you secure your future.
So, with the above discussion, we can say that the Cyber Kill Chain is a critical, foundational framework in modern cybersecurity. It offers you a clear, step-by-step understanding of how external attacks unfold.
The Cyber Kill Chain is a model that describes the external attack process in seven distinct, sequential stages. This model helps defenders identify and stop an intrusion at any point before the attacker achieves their goal. It essentially provides a roadmap of the adversary's actions.
Cyber Kill Chain in cyber security refers to a framework that helps security professionals understand, analyze, and mitigate cyber-attacks. The framework identifies the necessary phases an attacker must complete, giving the defender specific points of intervention or "choke points" to break the attack chain.
The primary purpose of the Cyber Kill Chain methodology is to improve defensive measures. By clearly defining the attack stages, it enables security teams to create defenses specifically targeted at each stage. This proactive defense aims to detect and disrupt the attack early, minimizing the damage.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts