.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

Code signing is the digital equivalent of a wax seal on a royal letter. To be honest, we’ve all been there: you download a cool new app, try to install it, and a giant red warning pops up saying "Unknown Publisher." It’s frustrating for you and even worse for the person who wrote the code. That’s where a digital signature steps in to save the day.
When you sign your work, you’re telling the world, "Hey, I wrote this, and it’s safe to use." It isn't just about vanity or branding. It is about deep-rooted security. In my experience, developers often ignore this step until a browser blocks their launch. Don't let that be you.
How does it actually work under the hood? It uses a mix of math and trust. By the end of this, you’ll see why skipping this step is like leaving your front door wide open in a storm.
The term code signing refers to the process of using a certificate-based digital signature to sign executables and scripts. Think of it as a virtual ID card. When you apply this signature, you achieve two main things: you prove your identity and you lock the code.
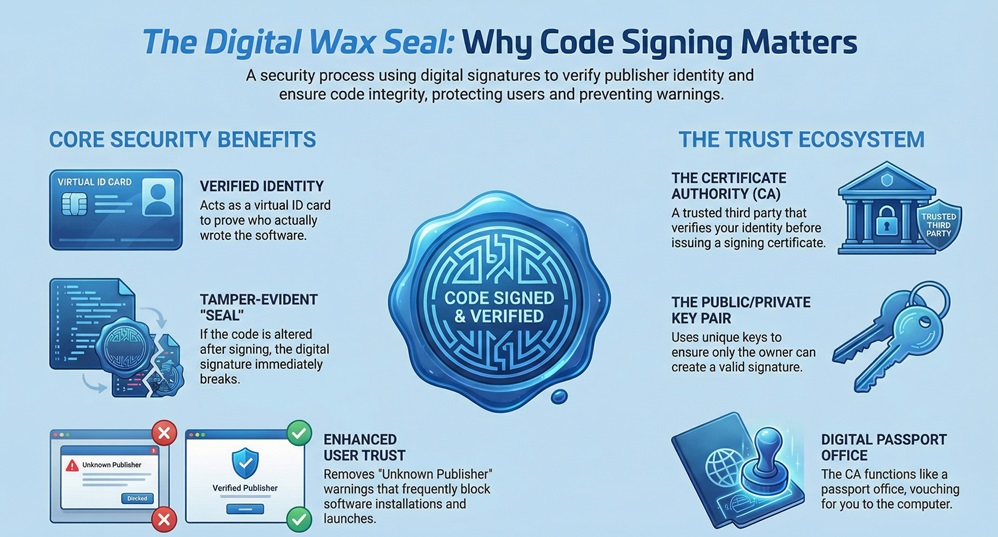
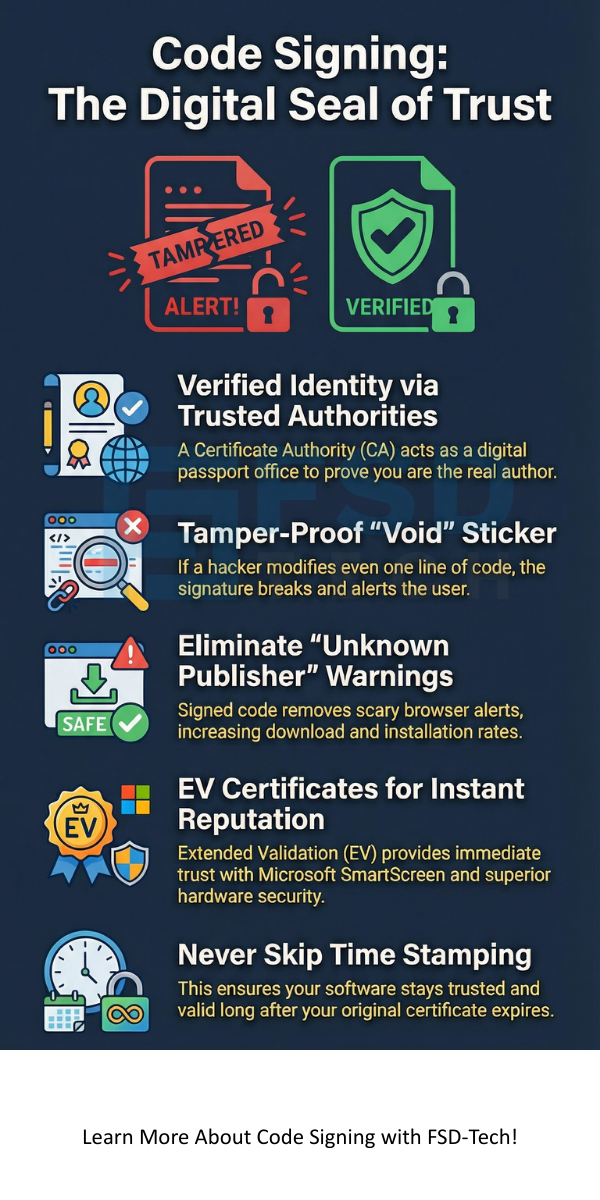
If a hacker tries to slip a bit of malware into your file after you’ve signed it, the signature breaks. It’s like a "void if tampered" sticker on a medicine bottle. This tells the user's computer that the file is no longer the original version you sent out.
Is it hard to set up? Not really, but you need the right tools. Most developers use a private key to sign the file and a public key to let others verify it. This pair ensures that only you could have created that specific signature.
We can't just vouch for ourselves in the digital world. We need a trusted third party. A Certificate Authority (CA) is an organization that checks who you are before giving you a code signing certificate. They act like a passport office.
When a computer sees a signed file, it checks who issued the certificate. If it’s a well-known CA, the computer relaxes. If you try to sign your own code without a CA, the computer will likely still throw a "Windows Protected Your PC" warning. This is because the system doesn't know who "You" are yet.
Using a CA ensures that the trust chain remains unbroken. We've seen software supply chain attacks skyrocket lately. By using a verified CA, you’re showing that you take your user's safety seriously. It's a small step that builds massive credibility.
Also Read: What is Managed Detection and Response (MDR)?
You might hear people talk about EV certificates. This stands for Extended Validation. While a standard certificate is great, EV code signing takes things to a whole new level. It requires a much stricter background check on your company.
The biggest perk? Immediate trust with Microsoft’s SmartScreen. If you use a regular certificate, you might still see warnings until you build up a "reputation." With an EV certificate, those warnings disappear instantly. It's like having a VIP pass at a crowded club.
However, EV certificates also require hardware security. You usually get a physical USB token or use a cloud-based Hardware Security Module (HSM). This means your private key isn't just sitting on your laptop where a thief could find it. It's locked away.
Let's break down the technical side. First, you create a "hash" of your code. A hash is a unique string of characters that represents your file. If even one comma changes in your code, the hash changes completely.
Next, your software uses your private key to encrypt that hash. This encrypted hash is your digital signature. You then bundle this signature and your certificate with the software.
When a user downloads your app, their computer does the same math. It creates its own hash of the file and decrypts your signature using your public key. If the two hashes match perfectly, the computer knows the file is safe. It’s a beautiful, automated way to keep everyone honest.
Also Read: What is Cybersecurity? Guide to Digital Safety
Picture this: you sign your software today, and your certificate expires in two years. Does your software stop working in two years? Not if you use time stamping.
Time stamping is a piece of data that says, "This signature was valid at the time the code was signed." It’s an extra layer of proof. Without it, your software would trigger warnings the moment your certificate reaches its end date. We always recommend adding a time stamp. It ensures your software stays trusted for years, even after your original certificate is gone.
Here is the thing: your signature is only as safe as your private key. If a hacker steals your key, they can sign malware as "You." This has happened to giant companies, and it’s a nightmare to fix.
Roughly 60% of security breaches involving signed code happen because keys were left in plain text or on unprotected servers. You must treat your key like the combination to a bank vault. Use passwords, use tokens, and never, ever share it.
If you’re working in a team, look into a Software Trust Manager. These tools let you sign code without actually giving every developer a copy of the key. It keeps the "gold" in the vault while letting the workers do their jobs.
Some people think that signing code makes it "virus-proof." That’s not true. Code signing only tells you who wrote the code and that it hasn't changed. A bad person could still sign a virus if they manage to get a certificate.
However, because the CA checks identities, bad actors are usually caught quickly. If a signed file is found to be malicious, the CA can revoke the certificate. This "kill switch" makes the software show a major warning on every computer in the world instantly.
Another myth is that it’s too expensive. While certificates cost money, the cost of losing a customer’s trust is much higher. Think of it as an insurance policy for your reputation.
We're moving toward a world where unsigned code won't run at all. Mobile phones already do this, and desktops are following. As we've already discussed, the software supply chain is under constant attack.
In my view, we will see more automation in this space. Tools are getting better at signing code as part of the build process. This means developers don't have to stop and do it manually. It just happens.
Will we see more cloud-based signing? Absolutely. It’s safer and easier to manage for remote teams. The goal is to make security so easy that there's no excuse to skip it.
At the end of the day, code signing is about showing your users that you care. We've all seen how quickly trust can vanish in the tech world. By taking the time to secure your software with a digital signature, you're building a foundation of safety. We pride ourselves on helping developers navigate these technical waters with ease. Our focus is always on your success and your clients' peace of mind. Let's make the internet a safer place together.
Talk to a security expert today
Your users will see scary warnings from their operating system. Browsers might even block the download entirely, which kills your conversion rates.
Usually, you can buy them for one to three years. After that, you need to renew them and verify your identity again.
Yes! You can sign .exe, .msi, .cab, .dll, and even Apple or Android apps. Each platform has its own specific tools for the job.
Not at all. The check happens during installation or when the app first opens. It doesn't affect how the software actually runs.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts