.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
Rootkit software represents one of the most dangerous threats in the cybersecurity world because you usually don't know it's there. Imagine a burglar who doesn't just steal your jewelry but also replaces your security cameras with fake loops. You look at the monitor, and everything looks fine, but the house is actually empty. That is exactly how these programs work. They hide themselves and other malicious tools from your operating system (OS).
Have you ever felt like your computer was acting strange, but your antivirus said everything was perfect? It’s a frustrating spot to be in. In my experience, catching a stealthy infection requires looking where the OS doesn't want you to look. To be honest, most people think a simple scan fixes everything. However, these digital ghosts play by different rules.
In this guide, we will look at how these tools operate. We'll explore why they are so hard to find and what you can do to protect your data. Ready to see what's hiding under the hood?
The term rootkit comes from two words: "root" and "kit." In Linux and Unix systems, "root" is the name of the account with the highest level of control. A "kit" is a set of tools. So, put them together, and you have a kit that gives an intruder root-level access.
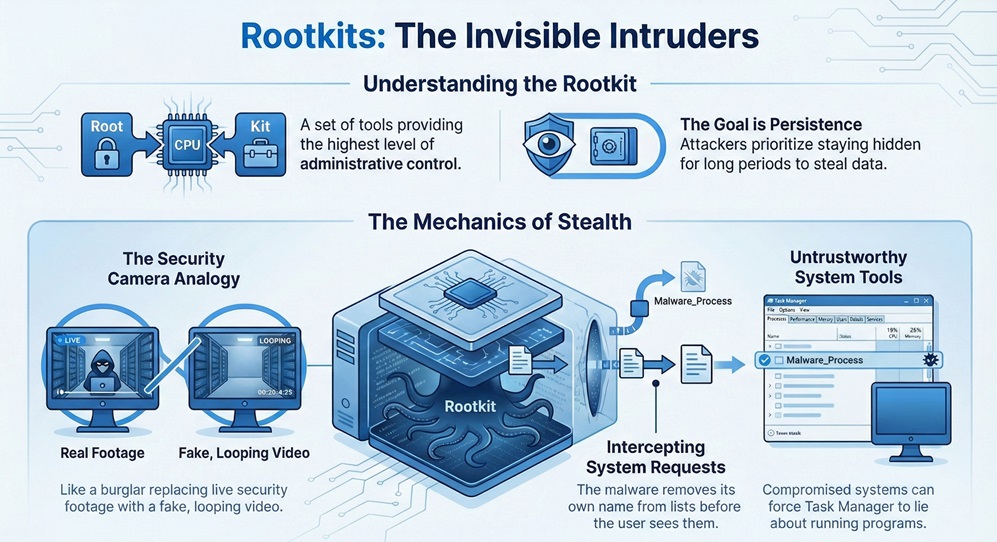
When a hacker installs one of these, they aren't just looking to crash your PC. They want to stay there for a long time. This is called "persistence." By hiding their presence, they can steal passwords or watch your screen without you ever knowing.
Here is the thing: these programs modify the very tools your computer uses to report what's happening. If you ask your computer to "list all running programs," the malware intercepts that request. It removes its own name from the list before you see it. It’s like a witness at a crime scene who is also the person writing the police report.
Do you think your Task Manager is always telling the truth? Not if a kernel-level threat is involved.
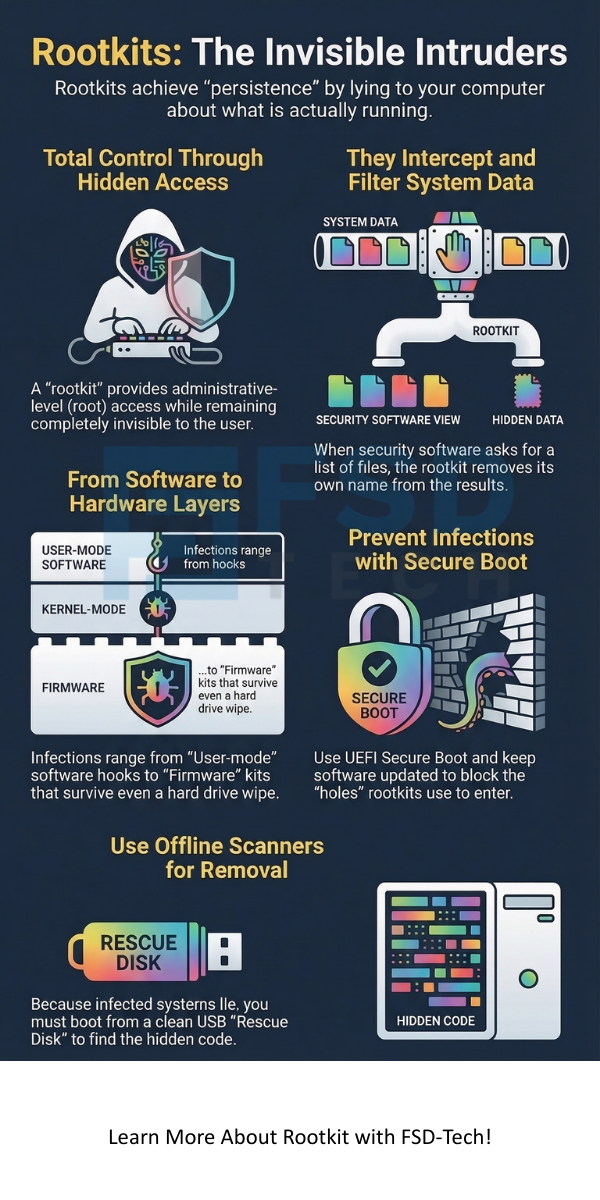
Not all infections are the same. Some live in your software, while others hide in the physical parts of your computer. Understanding these types helps us know how to fight them.
1. User-Mode Rootkits
These are the most common. They operate at the same level as your web browser or Word processor. They work by "hooking" into APIs (Application Programming Interfaces). When a program asks for information, the malware changes the answer.
2. Kernel-Mode Rootkits
This is where things get serious. The kernel is the heart of your OS. It manages the memory and the hardware. A Kernel-Mode Rootkit lives here. Because it has the same power as the OS itself, it can be almost impossible to find using standard tools.
If the kernel is compromised, you can't trust anything the computer tells you. In my view, this is the "final boss" of malware infections.
3. Bootkit (Bootloader Rootkits)
Have you ever wondered what happens the second you press the power button? Your computer runs a bootloader. A Bootkit replaces your legitimate bootloader with a fake one. This means the malware loads before your OS even starts.
4. Firmware and Hardware Rootkits
These hide in your BIOS, router, or even your hard drive's firmware. Even if you wipe your hard drive and reinstall Windows, the infection stays. Why? Because it isn't on the hard drive; it's in the chips of the hardware itself.
Also Read: What is Antibot? Stopping Automated Threats
You might be wondering, "How did this happen to me?" Usually, it starts with a simple mistake. Hackers use several tricks to get their "kit" onto your system.
We've all been there—clicking a link a bit too fast. But with this type of malware, that one click gives the attacker a permanent seat in your system.
The biggest challenge is that most security tools rely on the OS to give them data. If the OS is lying, the security tool is useless.
The Problem of Trust
To be honest, security is built on layers of trust. Your antivirus trusts the OS kernel. The kernel trusts the drivers. If a Rootkit replaces a driver, the chain of trust breaks. This is why we often have to use "Offline Scanning." This means booting from a USB drive to scan the hard drive while the infected OS isn't running.
How can you find something that has the power to make itself invisible? It's like trying to find a ghost using a camera the ghost has already hacked.
Prevention is much easier than a cure when it comes to these threats. Since they are so hard to remove, we must focus on keeping them out.
Keep Software Updated
Most hackers use old vulnerabilities. When Microsoft or Apple sends you an update, it's often a patch for a hole that a Rootkit could use. Don't wait. Install them immediately.
Use Secure Boot
Modern computers use UEFI (Unified Extensible Firmware Interface) with a feature called Secure Boot. This ensures that only trusted software can load when the computer starts. It's a great defense against boot-level threats.
Be Careful with Admin Rights
Do you use your "Administrator" account for everyday browsing? That's a big risk. If you are logged in as a standard user, malware has a harder time reaching the kernel. It's roughly the difference between a burglar having a key to your front door versus just looking through the window.
Also Read: Network Firewalls vs. Next-Generation Firewalls: Which One Wins?
If you suspect an infection, don't panic, but act fast. Here is a basic process we often recommend:
Note: Always back up your important files (photos, documents) to a cloud service or external drive regularly. If you have to wipe your PC, you won't lose your life's work.
In the past, these tools were used by hobbyist hackers. Today, they are used by state-sponsored groups and professional criminals. They use them to hide "Ransomware" or "Keyloggers."
As our defenses get better, the malware gets smarter. We are seeing more "fileless" attacks where the code only lives in the RAM (memory) and never touches the hard drive. This makes it even harder for traditional scanners to see.
The digital world is full of hidden dangers, and Rootkit attacks are among the most sophisticated. These tools remind us that what we see on our screens isn't always the full truth. By staying informed and following basic security habits, you can keep your "digital house" safe from these invisible intruders.
At our core, we believe that security should be simple and accessible. We are committed to helping you understand your technology so you can use it with confidence. Your safety is our priority, and we're always here to help you navigate the complex world of cybersecurity.
Sometimes, but not always. Many can find "User-Mode" versions. However, "Kernel-Mode" versions often hide from standard antivirus programs. You need specialized tools or offline scans.
No. These tools are designed for "persistence." They stay in your system through restarts and even some system updates.
Look for signs like your antivirus turning itself off, sudden slow performance, or strange network traffic. However, the best ones show no signs at all.
Technically, no. A virus spreads and damages files. This is a "stealth" tool used to hide other malware like viruses or spyware.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts