.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

The digital world faces constant security threats. You constantly search for robust ways to protect your systems. Application Whitelisting (AWL) provides a highly effective, foundational approach to this protection. It is a critical security control that ensures only trusted programs can execute on a system.
Application Whitelisting can be understood as a security method that creates a definitive list of approved, or "whitelisted," applications and code allowed to run on a computer or network. This action fundamentally shifts the security posture from a denial-based model to an allowance-based model. Only authorized applications will run, and the system automatically blocks everything else.
This practice is essential, especially when you consider that traditional antivirus methods often struggle to keep up with the constant emergence of new, unknown threats. Application whitelisting offers a simple, powerful solution. It permits only known-good files to execute, dramatically reducing the chances of malware, viruses, and unauthorized software affecting your business.
We will now explore this powerful security measure in detail. We will examine how this strategy works, why you need it, and how you can implement it effectively using the right application whitelisting software.
Application whitelisting refers to the technique of specifying an explicit list of software programs that a system permits to run. This method of security control provides a contrast to the widely used "blacklisting" approach, which tries to identify and block known malicious programs.
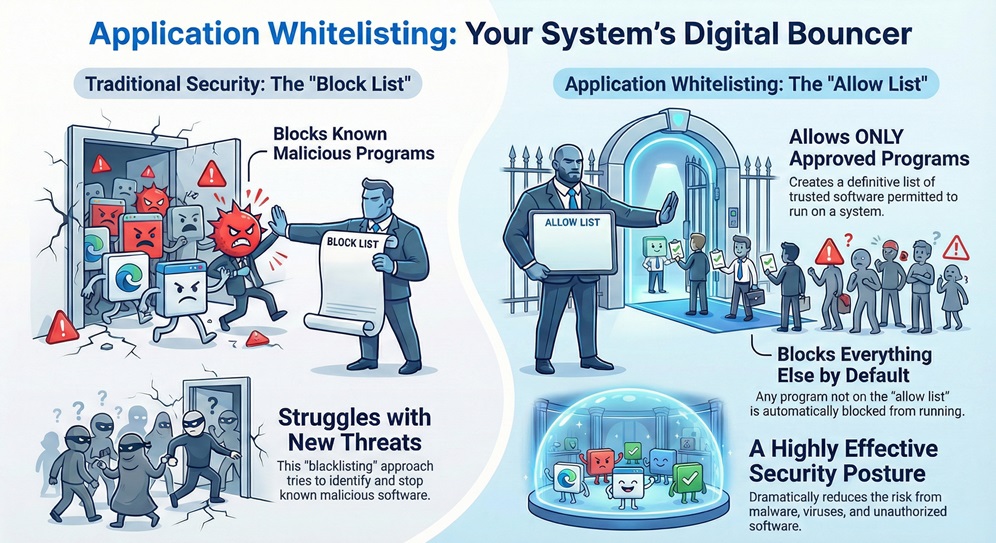
In a system protected by AWL, any program that is not on the approved list receives an automatic block. This block occurs regardless of whether the system knows the program to be good or bad. This acts as a digital bouncer, allowing only those with an invitation to enter.
To understand this better, we must explore the process that application whitelisting follows to ensure system integrity. The principle works on a simple but powerful premise: trust nothing unless explicitly permitted.
The process of implementing an effective application whitelisting tool generally involves three key phases:
This verification process ensures that even if a new piece of malware enters the system, the system cannot execute it because it is not an authorized application. This drastically reduces the attack surface.
Also Read: What Is Application Security? Tools, Testing & Best Practices
A robust application whitelisting policy consists of several crucial elements. Application whitelisting implementation depends on how strictly you define these attributes.
To fully appreciate the power of AWL, you should understand how it differs from traditional antivirus approaches, which primarily use blacklisting.
| Basis for Comparison | Application Whitelisting (AWL) | Application Blacklisting |
|---|---|---|
| Core Principle | Allows only known, approved applications to run. | Prevents only known, unapproved (malicious) applications from running. |
| Security Posture | Default Deny: Everything is blocked unless explicitly allowed. | Default Allow: Everything is permitted unless explicitly blocked. |
| New/Unknown Threats | Effectively prevents unknown threats (Zero-Day attacks) since they are not on the approved list. | Ineffective against unknown threats until a security vendor creates a signature and updates the list. |
| Maintenance | Requires effort to maintain and update the list of approved applications when changes occur. | Requires continuous, daily updates to the blacklist of known threats. |
| Impact on System | Higher security, more predictable environment, but requires careful initial setup. | Lower security assurance, but simpler initial setup. |
| Long-Tail Keyword | top 10 application whitelisting software | Traditional Antivirus Solutions |
Application whitelisting is fundamentally a much stronger security approach. While blacklisting struggles to keep up with the pace of new malware, AWL simply denies all non-approved executables right from the start.
Also Read: Quantum Cryptography - QKD, Security & Future Guide
Implementing application whitelisting provides several significant benefits that strengthen your security posture. This security measure plays a vital role in modern threat defense.
1. Robust Protection Against Malware and Zero-Day Threats
Application whitelisting offers immediate, high-level protection against all forms of unauthorized code. This includes:
2. Regulatory Compliance and Control
Many industry regulations and security frameworks specifically recommend or mandate the use of whitelisting. Application whitelisting solutions facilitate compliance with standards such as the National Institute of Standards and Technology (NIST) Special Publication 800-167 and guidelines from the Cybersecurity and Infrastructure Security Agency (CISA). This helps you meet required security baselines.
3. Effective License and Resource Management
Implementing a strict whitelist also helps in maintaining control over the software installed and running on your network. This leads to several operational advantages:
4. Strong Defense for Industrial Control Systems (ICS)
Application whitelisting is a critical security measure for Industrial Control Systems (ICS) and Operational Technology (OT) environments, as outlined in CISA guidelines. These systems often run legacy operating systems and cannot tolerate unexpected reboots or patches. AWL provides a stable security layer, permitting only the pre-approved industrial software and drivers to execute, thereby maintaining the operational continuity of essential services.
Also Read: What is Sandboxing in CyberSecurity? How It Works?
Successfully deploying an application whitelisting solution requires careful planning and a systematic, sequential process. Let us now discuss the steps you must follow.
Step 1: Initial Discovery and Inventory
First, you must establish a comprehensive baseline. This involves:
Step 2: Develop and Test the Policy
Next, you define the rules for enforcement. Application whitelisting policy development requires precision.
Step 3: Implement Enforcement and Management
After thorough testing, you can activate the protection.
Also Read: What is Vulnerability Assessment? Process & Tools
Selecting the right application whitelisting software is crucial for successful implementation. Various application whitelisting tools exist, each offering a specific set of features.
When evaluating application whitelisting solutions, you should look for the following characteristics:
Security is an ongoing commitment, not a one-time fix. Implementing a powerful application whitelisting solution dramatically reduces the attack surface of your critical systems, ensuring stability and compliance. We specialize in deploying foundational security controls that bring clarity and certainty to your operations.
Contact us today to explore how our expertise in application whitelisting can protect your most valuable digital assets.
Application whitelisting serves as an indispensable security control in today's threat environment. It provides a significant and necessary shift from trying to identify bad programs to only permitting known-good programs.
AWL complements, but does not completely replace, your antivirus solution. While AWL prevents the execution of unauthorized code, your antivirus still serves a role by detecting and removing known malware from storage and scanning email attachments or downloaded files. Together, they provide a layered defense.
This is the most common challenge. When an approved application updates, its file hash changes. The application whitelisting tool must offer a mechanism—often by trusting the vendor's digital certificate—to automatically approve the update. Alternatively, the administrator must manually update the whitelist with the new file hashes through the change management process.
Yes, you can use application whitelisting on a wide range of devices, including servers, desktop computers, Industrial Control Systems (ICS), and even embedded devices. Its effectiveness is particularly high on systems with a stable and predictable software footprint, such as servers or specialized workstations.
Application blacklisting is nothing but a security approach that lists known malicious files or applications. The system permits everything except the items on the blacklist. Blacklisting is reactive, as it requires prior knowledge of the threat.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts