.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

You hear about data breaches and constant threats. Therefore, organizations need tools to watch their entire IT network constantly. Security Information and Event Management (SIEM) is nothing but a solution that provides this continuous watch.
To understand this better, a security information and event management platform collects, analyzes, and presents security data from all the different parts of your IT setup. This includes firewalls, servers, applications, and network devices. Simply put, SIEM helps you detect security threats and respond to them quickly.
We will discuss how a security information and event management system works and why it plays a vital role in protecting your data.
The security information and event management solution is based on two primary functions: Security Information Management (SIM) and Security Event Management (SEM).
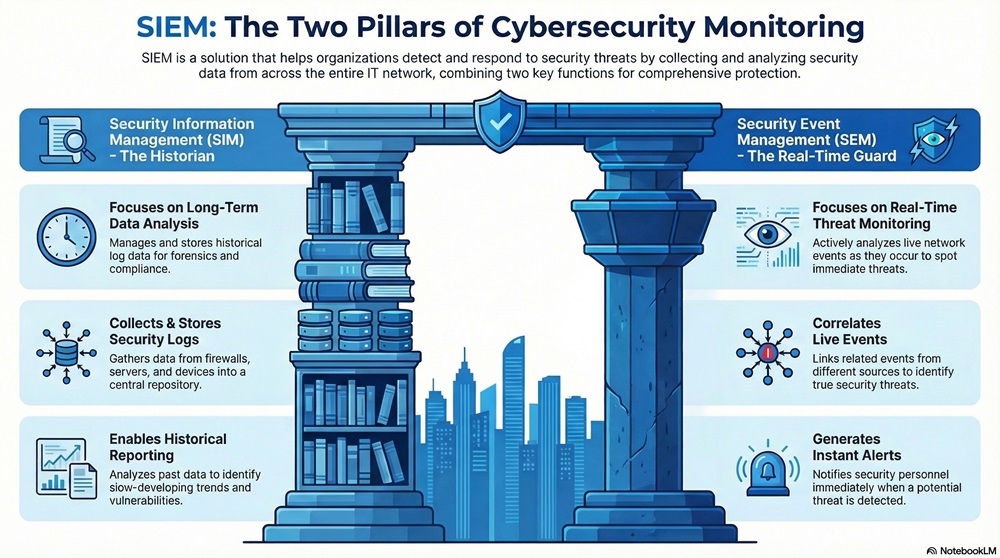
SIM mainly deals with log data management. It refers to the process of collecting log data from various sources and then storing this information for a long period. This is essential for forensics and compliance.
SIM provides these services:
SEM, on the other hand, deals with real-time event monitoring and analysis. It focuses on identifying and responding to active threats.
SEM performs the following:
The security information and event management solution brings these two functions together. It provides both a real-time watch and a long-term record.
SIEM Today Contact our experts now
The functioning of a security information and event management system is a systematic, step-by-step process. This process ensures that no critical security event goes unnoticed.
1. Data Aggregation and Collection
The SIEM process begins with data aggregation. The platform collects security logs and event data from every source in your network.
2. Data Analysis and Correlation
Once the system collects and normalizes the data, it begins the vital process of analysis. This is where the core security information and event management (SIEM) technology comes into play.
3. Threat Monitoring and Alerting
The ultimate purpose of a security information and event management system is to alert the security team to real threats.
4. Security Incident Management and Reporting
Finally, the SIEM system facilitates the response and compliance aspects of cybersecurity.
Also Read: What is Threat Hunting? Proactive Cyber Security
Deploying a security information and event management platform provides several crucial advantages for any organization focused on protecting its valuable data.
People often confuse SIEM with simple log management. While the two concepts are related, they serve different primary purposes. Let us compare them clearly.
| Basis for Comparison | Security Information and Event Management (SIEM) | Log Management |
|---|---|---|
| Primary Goal | Threat Detection and Incident Response | Data Storage and Searching |
| Analysis | Real-time correlation, behavioral analysis, and threat prioritization | Historical search and retrieval of individual events |
| Data Scope | Focuses on security-relevant logs and events | Collects all logs from all IT sources |
| Alerting | Generates immediate, high-priority alerts based on patterns | Requires manual creation of reports or basic threshold alerts |
| Data Usage | Used primarily by Security Operations Center (SOC) teams | Used by IT Operations, developers, and auditors |
| Technology | Includes correlation engines and advanced analytics | Mainly involves collection, indexing, and storage |
SIEM is a step far beyond simple log storage. Log management simply collects and archives the raw data. The security information and event management system takes that raw data, makes sense of it, and alerts you when something bad is about to happen. This distinction is critical.
Also Read: Cyber Threat Intelligence (CTI) in Cybersecurity
To ensure that you get the maximum value from the best security information and event management systems, you must follow certain practices.
1. Define Clear Use Cases
Before deployment, security teams must define specific use cases that the SIEM will monitor.
2. Proper Rule Tuning
The correlation rules and alerts in the SIEM must be accurate.
3. Continuous Monitoring and Review
A SIEM solution is not a "set it and forget it" tool.
4. Effective Data Prioritization
Do not try to ingest every single log file. This can become too costly and difficult to manage.
The modern threat landscape is complex and constantly changing. Simply installing point security products, like a firewall or an antivirus program, is no longer enough to protect your organization. You need a way to connect all the security information and respond to the most critical threats in real time.
The security information and event management platform provides this capability. It empowers your security team by providing comprehensive visibility and smart analysis.
Thus, we can say the security information and event management (SIEM) technology is an essential investment. It ensures that your security professionals can quickly detect, analyze, and manage security incidents, thereby protecting your most vital assets.

A: The firewall acts as a gatekeeper. It blocks known bad traffic at the network border. The SIEM acts as a security investigator. It collects data from the firewall (and other devices) to detect complex, multi-stage attacks that the firewall alone cannot see.
A: An event refers to any change in the state of a system or network. Examples include a user logging in, a file being accessed, or a connection being made between two devices. The security information and event management solution collects millions of these events.
A: No, the security information and event management system does not replace your existing tools like antivirus software or intrusion detection systems. Instead, it integrates with them. The SIEM platform collects the output (logs and alerts) from these existing tools and makes them more powerful by correlating the data.
A: Even with good security controls, a determined attacker can still get past them. The purpose of a security information and event management system is to find the residual threats—the attacks that slipped past your initial defenses. It finds the tiny pieces of evidence left behind and links them together.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts