.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

Cybersecurity is the practice of protecting systems, networks, and programs from digital attacks. These attacks usually aim to access, change, or destroy sensitive information. Think about how much of your life lives online today. From bank details to private photos, everything is a target. But why does this matter to you? Well, imagine waking up and finding your digital identity wiped or your savings gone. It sounds like a movie plot, but it happens to real people every day.
We've all been there—clicking a link that looks a bit "off" or using the same password for five different sites. In my experience, most people think they aren't "important" enough to be hacked. That is a dangerous mistake. Hackers don't always want you specifically; they want your data or your computer’s power. This guide will walk you through the basics of staying safe without making your head spin with tech jargon.
The term cybersecurity refers to a set of layers spread across computers and networks. To stay safe, these layers must work together. When we talk about defense, we usually look at the "CIA Triad." No, not the secret agents! It stands for Confidentiality, Integrity, and Availability.
The world is more connected than ever. We use smart fridges, wearable watches, and cloud storage for everything. Each of these devices is a "door" into your life. Roughly 2,200 cyberattacks happen every day. That’s one every 39 seconds! If we don't take CS (cybersecurity) seriously, we leave our virtual front doors wide open.
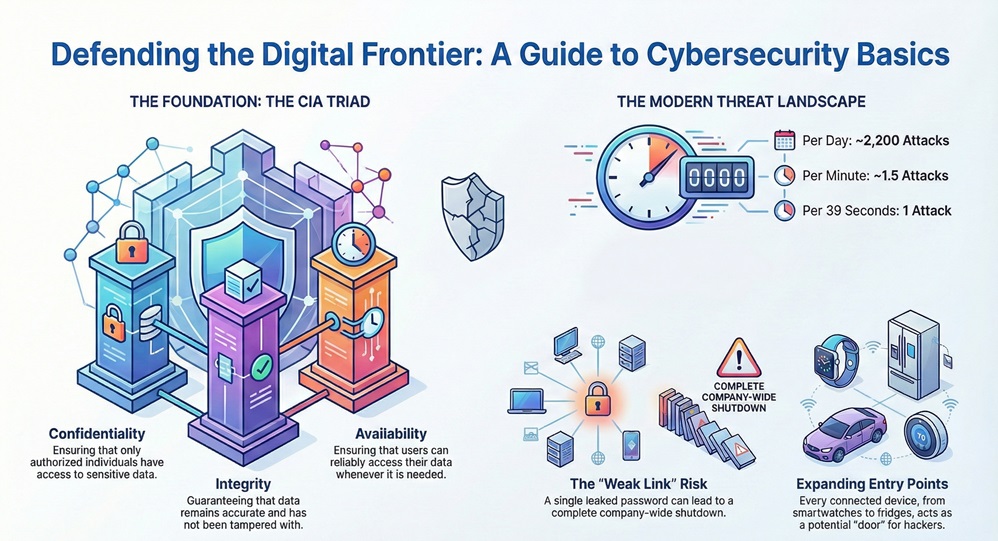
Have you ever wondered how a single leaked password can lead to a company-wide shutdown? It’s because everything is linked. One weak link can break the whole chain.
Also Read: What is a Secure Web Gateway and How Does It Protect You?
Knowing your enemy is the first step in any fight. In the world of cybersecurity, threats come in many flavors. Most aren't high-tech "Matrix" style code-breaking. They're often simple tricks.
Phishing and Social Engineering
Phishing is when someone sends a fake email to trick you. They might pretend to be your bank or a boss. They want you to click a link or give up a password. To be honest, this is the most common way hackers get in. They don't hack the machine; they hack the human.
Malware and Ransomware
Malware is "malicious software." This includes viruses, worms, and spyware. A very scary version is ransomware. It locks your files and demands money to give them back. Imagine losing all your family photos unless you pay $500 in Bitcoin. It’s a nightmare scenario we see too often in small businesses.
Man-in-the-Middle (MitM) Attacks
Picture this: you're at a coffee shop using their free Wi-Fi. A hacker sits nearby and "listens" to the data traveling between your laptop and the router. They can see your login info as you type it. This is why using public Wi-Fi without a VPN is like whispering your secrets in a crowded room.
Building a defense isn't just about installing an antivirus. It is about a mindset. Effective cybersecurity requires a mix of tools, processes, and people.
Network and Infrastructure Security
Your network is the highway your data travels on. Network security involves firewalls and encryption to make sure no "hitchhikers" grab your data. For businesses, this often means using a Secure Access Service Edge (SASE). SASE combines networking and security into one cloud service. It makes it much harder for attackers to find a way in.
Application and Cloud Security
We use apps for everything. If an app has a bug, a hacker can use it to get into your phone. Developers must write secure code to prevent this. Similarly, cloud security protects data stored on servers like Google Drive or iCloud. While these companies have huge security teams, you still need to lock your "individual" door with a strong password.
The Human Element
I've said it before, and I'll say it again: you are the most important part of the shield. No software can stop you from giving away your password if you're tricked. Training and "cyber hygiene" are vital. What does that mean? It means updating your software, using a password manager, and being skeptical of "too good to be true" offers.
Also Read: Secure Coding Practices: How to Build Apps That Don't Break
Now that we know the "what," let's look at the "how." How does a company or a person actually stay safe? It usually involves a cycle of identifying, protecting, detecting, responding, and recovering.
Identification and Risk Assessment
You can't protect what you don't know you have. The first step in cybersecurity is making a list of your digital assets. This includes hardware, software, and sensitive data. We then ask: "What is the worst thing that could happen to this?"
Implementing Protective Measures
Once we know the risks, we put up guards.
Detection and Response
What happens when an attacker gets through? You need a way to see them. Systems use "logs" to track activity. If a user logs in from Russia and then two minutes later from New York, the system flags it. A fast response can mean the difference between a small glitch and a total disaster.
Is cybersecurity just a personal problem? Not at all. Governments have passed laws like the GDPR and Various Data Protection Acts. These laws force companies to protect your data. If they lose it because they were lazy, they have to pay massive fines.
In many countries, there are specific agencies focused on national digital defense. They protect power grids, water systems, and hospitals from foreign attacks. This is often called "Cyber Warfare," and it is a very real part of modern global politics.
Also Read: Security Automation: How to Protect Your Data Without the Burnout
Let's clear the air on a few things.
The world of cybersecurity is always changing. As we move toward 2026, Artificial Intelligence (AI) is playing a bigger role. Hackers use AI to write better phishing emails. On the flip side, we use AI to spot attacks faster than any human could.
We're also seeing the rise of "Zero Trust." This is a strategy where the system assumes everyone is a threat until proven otherwise. You have to verify your identity every step of the way. It sounds annoying, but it's the safest way to operate in a digital world.
Staying safe online doesn't mean you have to be a tech genius. It starts with small, consistent habits. By understanding what cybersecurity is and how it works, you've already taken the biggest step toward safety. We're all in this together. Our company believes in a digital world where everyone can browse, shop, and work without fear. We're committed to helping you build that secure future, one click at a time.
Ready to lock down your digital life?

It is the practice of protecting your digital devices, services, and data from unauthorized access or damage.
Yes. Hackers often use automated bots to find any weak password or unpatched device, regardless of who owns it.
First, disconnect the device from the internet. Change your passwords from a "clean" device. Then, notify your bank and any relevant services.
It's better than nothing, but paid versions often offer better protection against new threats and "zero-day" exploits.
Instead of changing them often (which leads to weak passwords), use long, unique "passphrases" and a password manager. Change them immediately if a service you use has a breach.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts