.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
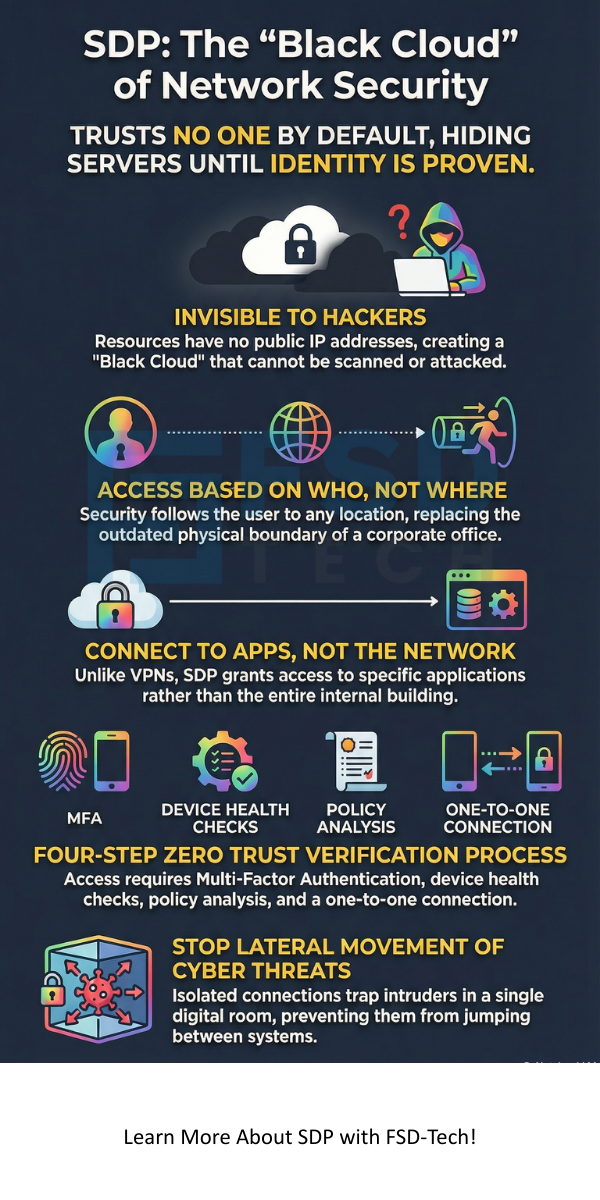
Have you ever wondered if your company's data is actually invisible to hackers? Traditional security acts like a castle moat. Once someone crosses the bridge, they're inside. But what if the castle itself was invisible until you proved who you were? That is the core idea behind a Software-Defined Perimeter.
A Software-Defined Perimeter, or SDP, is a security framework that controls access to resources based on identity. It doesn't care where you are or what network you're using. Instead of a physical boundary, it creates a virtual one. We often call this a "Black Cloud" because unauthorized users can't even see the servers they're trying to attack.

In my experience, moving to an SDP feels like a breath of fresh air for IT teams. To be honest, the old way of using Virtual Private Networks (VPNs) is dying. They're clunky, slow, and often leave doors wide open for lateral movement. Have you ever had a VPN drop right in the middle of an important meeting? It’s frustrating. SDP solves this by being smarter and faster.
The Software-Defined Perimeter works on a "need-to-know" basis. It follows the Zero Trust model. This means the system trusts no one by default. Even if you're inside the office, you still need to prove your identity.
The process usually follows these steps:
This is a huge shift. In the past, a VPN gave you the keys to the whole building. With an SDP, you only get the key to one specific desk. It makes it much harder for a virus to spread.
When we talk about a Software-Defined Perimeter, we usually look at three main parts. These parts work together to keep things hidden.
Here's the thing: the server doesn't even have a public IP address. It’s essentially a ghost on the internet. If a hacker scans your network, they see nothing. How can they attack what they can't find?
Also Read: Perimeter Security: How to Protect Your Property Effectively
Many people ask me, "Is a Software-Defined Perimeter just a fancy VPN?" The short answer is no. While both provide remote access, the way they do it is totally different.
Hidden vs. Visible Networks
A VPN usually sits on the edge of your network. It has a public entry point. Hackers can find that point and try to break in. On the other hand, an SDP keeps everything dark. You can't ping an SDP protected resource.
Granular Access Control
We've all been there—giving a contractor access to one file, but they end up seeing the whole server. VPNs struggle with "fine-grained" control. An Software-Defined Perimeter handles this naturally. It connects the user to the application, not the network.
Performance and Scalability
VPNs often "backhaul" traffic. This means all your data travels to a central data center before going to the cloud. It's like driving twenty miles out of your way just to turn around. SDP allows for direct connections. This makes your internet feel much faster.
Implementing a Software-Defined Perimeter isn't just about security. It's about making work easier for everyone.
1. Stopping Lateral Movement
If a hacker steals a password, they usually try to jump from one computer to another. Because SDP isolates every connection, that jump becomes impossible. They’re stuck in a tiny digital room with nowhere else to go.
2. Multi-Cloud Security
Does your company use AWS, Azure, and on-premise servers? Managing security across all of them is a nightmare. An SDP acts as a single layer that covers everything. It gives you one place to manage rules for all your clouds.
3. Better User Experience
Nobody likes logging into a VPN five times a day. Most SDP tools run quietly in the background. You just open your app and start working. It feels like magic, but it's just good engineering.
"In my view, the best security is the kind that users don't even notice. That's exactly what an SDP provides."
Also Read: What is a Secure Web Gateway and How Does It Protect You?
This is a common point of confusion. To be clear, Zero Trust is a strategy. A Software-Defined Perimeter is a tool used to reach that strategy. You can think of Zero Trust as the "goal" and SDP as the "engine" that gets you there.
The SDP framework was actually created by the Cloud Security Alliance (CSA). They wanted a way to make the "perimeter" follow the user. Since we no longer sit in cubicles all day, our security needs to move with us. Whether you're at a coffee shop or in a home office, the SDP keeps the boundary tight.
Where does a Software-Defined Perimeter really shine? We see it used most in three specific areas.
Secure Remote Access
Since the pandemic, everyone is working from home. Companies need a way to keep data safe on home Wi-Fi. An SDP makes this easy by verifying the person and the device before any data moves.
Third-Party Access
Do you have vendors or partners who need to see your data? Instead of giving them a full network login, give them an SDP link. They see only what they need, and your core network stays safe.
Mergers and Acquisitions
When two companies join, connecting their networks is a security risk. It can take months. With an Software-Defined Perimeter, you can connect them in days without merging the actual hardware.
The world of work has changed. We don't stay behind a physical wall anymore. Our data lives in the cloud, and our employees live everywhere. This is why a Software-Defined Perimeter is so important. It moves the protection to the person.
At the core of FSD-Tech, we believe in keeping things simple and safe. We've seen how much stress a data breach causes, and we want to help you avoid that. Our focus is always on your success and your peace of mind. Let’s build a future where your data is invisible to the bad guys but always ready for your team.
It stands for Software-Defined Perimeter. It's a way to hide internet-connected balance and give access based on identity.
Not exactly. It works with your firewall. While the firewall blocks bad traffic, the SDP hides the good stuff so it can't be targeted in the first place.
It can be simpler than a VPN. Because it's software-based, you don't need to ship expensive hardware to every office. Most companies use a cloud-based SDP provider.
Yes! In fact, it's great for small teams. It’s roughly the same cost as a professional VPN but offers much better protection for your files.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts