.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
Have you ever wondered if your digital doors are actually locked? Penetration testing acts as a stress test for your entire digital world. It is a controlled way to see if a hacker could break into your systems. Instead of waiting for a real criminal to show up, you hire a friendly expert to try and get in first. We often call this "ethical hacking."
Here’s the thing: most companies think they are safe because they have a firewall. But is that enough? In my experience, even the strongest locks don't matter if someone left a window open on the second floor. To be honest, most security gaps come from small mistakes, not giant system failures.
Does your team know how to spot these gaps? Penetration testing helps you find those "open windows" before the bad guys do. It is a deep dive into your network, apps, and even your staff's habits. By the end of this guide, you’ll see why this process is a must-have for any modern business.
Get Your Free Security Consultation
We’ve all been there—installing a new piece of software and assuming it's secure. But the digital world changes fast. New bugs appear every day. A penetration testing session provides a snapshot of your security at a specific moment. It’s like a medical check-up for your computer network.
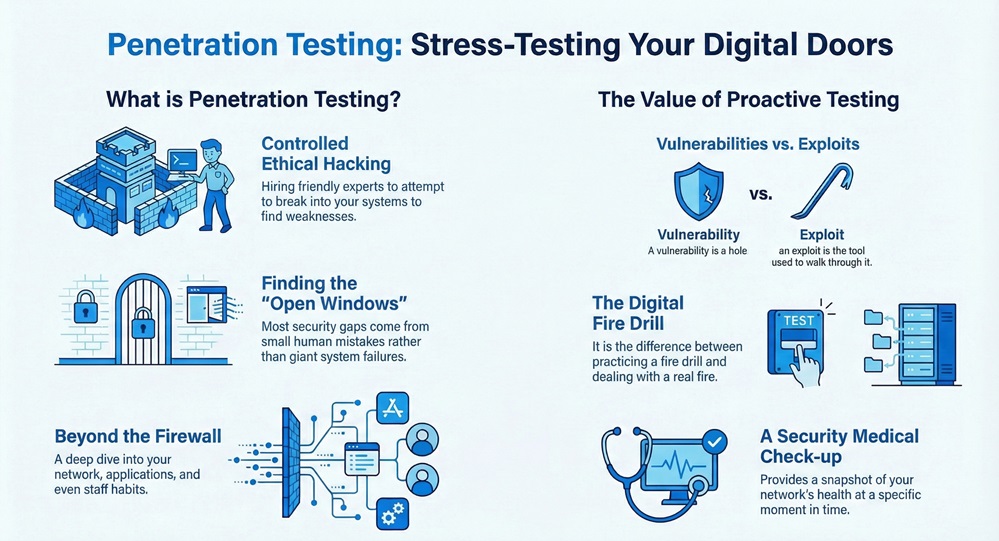
The main goal of a PT (Penetration Test) is to find "exploitable" weaknesses. A vulnerability is just a hole, but an exploit is the tool used to walk through it. Why wait for a disaster to happen? By running these tests, you stay ahead of the curve. It’s roughly the difference between practicing fire drills and actually dealing with a fire.
Also Read: What is Ransomware? Definition, Types, and Protection
Not all tests are the same. Depending on what you want to protect, you might choose a specific "flavor" of testing.
1. Network Services
This is the most common type of penetration testing. Experts look at your servers, routers, and switches. They search for open ports or old software that hasn't been updated. If your network is the foundation of your house, this test checks for cracks in the cement.
2. Web Application Testing
Do you have a customer portal or an online store? Web apps are huge targets. A penetration testing expert will look for things like SQL injection or cross-site scripting. These are just fancy ways of saying they check if a hacker can trick your website into giving up secret data.
3. Social Engineering
Sometimes, the weakest link isn't a computer; it's a person. In this phase, the tester might send "phishing" emails to your staff. They want to see if anyone clicks a suspicious link. It’s a bit eye-opening to see how easily a simple email can bypass a million-dollar firewall.
4. Wireless Testing
How secure is your office Wi-Fi? Testers will sit in your parking lot (with permission!) and try to crack your password. They also look for "rogue" access points that shouldn't be there.
A good penetration testing process follows a strict path. It isn't just "smash and grab." It is a careful, scientific method.
Phase 1: Planning and Recon
First, we define the scope. What are we testing? Is it the whole office or just one app? Then, the tester gathers "intel." This might include IP addresses or employee names found online. It’s like a scout looking at a map before a big game.
Phase 2: Scanning
Next, the tester uses tools to see how the target responds to intruders. They look for "live" hosts and open doors. This is where we see what software you are running and if it's out of date.
Phase 3: Gaining Access
This is the "hacking" part. The tester uses the data from the scanning phase to launch an attack. They might try to steal a password or hijack a session. This proves that a hole is not just a theory—it’s a real risk.
Phase 4: Maintaining Access
Once inside, can the tester stay there? Real hackers try to hide in your system for months. During penetration testing, the expert tries to see if they can move from a low-level computer to the main "admin" server.
Phase 5: Analysis and Reporting
This is the most important part for you. You get a detailed report. It lists what was found, how they got in, and—most importantly—how to fix it. We focus on "remediation," which is just a fancy word for "patching the holes."
Also Read: What is an Access Control System (ACS) for your security?
When you start a penetration testing project, you have to decide how much info to give the tester.
| Test Type | Information Given | What it Simulates |
|---|---|---|
| Black Box | None (only a URL or IP) | An outside hacker with no inside knowledge. |
| White Box | Full Access (code, IP, maps) | A rogue employee or "insider threat." |
| Grey Box | Partial (user login) | A customer or partner with limited access. |
In my view, Grey Box testing is often the best value. It saves time on the "guessing" phase but still feels like a real-world attack.
Is your company required to follow PCI DSS or HIPAA? If you handle credit cards or health data, penetration testing isn't just a good idea—it's the law. For example, PCI DSS 11.3 requires yearly testing.
If you fail to do this, you could face huge fines. Worse, you could lose the trust of your customers. Think of PT as your proof of due diligence. It shows the world (and your lawyers) that you take security seriously.
While the human brain is the best tool, experts use software to speed things up. You might hear names like:
Don't worry, you don't need to know how to use these. That’s what the pros are for!
"We did a test last year, we're fine, right?" Not exactly. I recommend penetration testing at least once a year. However, you should also run a test whenever you:
Security is a journey, not a destination. Fast-forward to six months from now—a new virus could exist that didn't exist today. Stay vigilant.
This is a common mix-up. Here is the simple version:
You need both. Scans are great for weekly checks, but PT gives you the deep "why" and "how."
At the end of the day, penetration testing is about being honest with yourself. It’s easy to assume we are safe, but a PT proves it. Our company values transparency and safety above all else. We don't just find problems; we partner with you to solve them. We’ve helped hundreds of clients turn their weaknesses into strengths. Your data is your most valuable asset—let's make sure it stays yours.

Professional testers are very careful. We've all been there where a tool runs too fast and slows things down, but a pro will schedule attacks during "off-hours" to keep your business running.
Usually, it takes between 1 to 3 weeks. It depends on how big your network is and what you want to test.
It costs more than a simple scan because you are paying for a human expert's time. However, it's much cheaper than the cost of a data breach.
You'll get a report. Your IT team will use this to fix the problems. Usually, the tester will do a "re-test" later to make sure the holes are truly closed.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts