.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

Every organization relies on software. This software, including operating systems and applications, often contains flaws. These flaws, known as vulnerabilities, create security risks. To fix these issues, software vendors release updates or corrections—these are called patches. The systematic process of acquiring, testing, and applying these patches is what we call patch management.
Patch management is nothing but a controlled process. This process ensures that you install necessary software updates promptly across all your systems. By consistently performing this task, you significantly reduce the risk of cyberattacks and maintain the stability of your entire IT structure.
Do you really need a structured way to handle software updates? Absolutely. Simply applying every update immediately can sometimes break other systems. A methodical patch management system determines what to patch, when to patch, and how to verify the installation's success.
Patch management meaning refers to the systematic process of installing, testing, and verifying software updates—known as patches—across all your computing devices. Every software, from operating systems to applications, contains flaws or vulnerabilities. Software vendors release patches to fix these security issues or bugs.
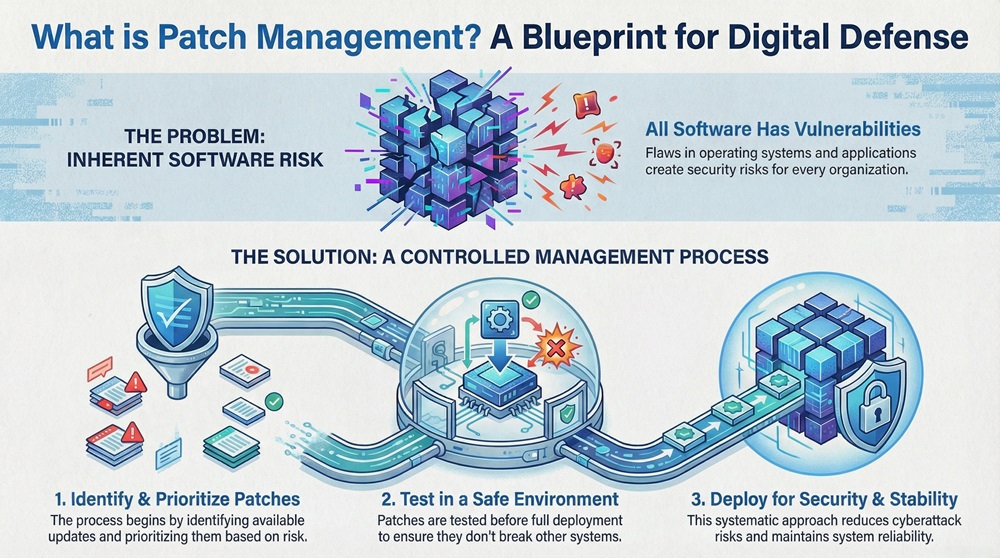
You do not simply install every patch immediately. A successful patch management system first identifies necessary updates, prioritizes them based on risk, and tests them in a safe environment. Only then does the system deploy the updates using automated patch management tools.
This structured approach significantly reduces the risk of cyberattacks and maintains system stability. Consistently performing security patch management is vital for protecting your digital assets and ensuring compliance.
Before we explore the full process, let us first clarify two key terms that often cause confusion: patch management and vulnerability management. While both are crucial for security patch management, they represent different steps in the overall defense strategy. We present the key differences in the table below.
| Basis for Comparison | Patch Management | Vulnerability Management |
|---|---|---|
| Definition | The process of applying software updates (patches) to fix existing flaws. | The comprehensive process of identifying, evaluating, treating, and reporting security flaws. |
| Primary Goal | To implement the fix provided by the vendor. | To identify and prioritize all security weaknesses, whether a patch is available or not. |
| Scope | Focuses on the implementation of vendor-provided software fixes. | Broader scope; includes risk assessment, remediation planning, and sometimes asset inventory. |
| Action | An implementation action—installing a patch. | An analytic and strategic action—finding and prioritizing risks. |
| When to Use | When a vendor releases a specific patch for a known issue. | Continuously, to assess the overall security posture of the network. |
Vulnerability patch management refers to the stage where you decide to implement a patch for a specific, identified vulnerability. Patch management, on the other hand, acts as a tool for vulnerability management.
Also Read: What is Vulnerability Assessment? Process & Tools
A reliable patch management system comprises several essential elements. You need these elements to ensure effective and comprehensive coverage across your organization's IT infrastructure.
The following are the core components that make up an effective patch deployment solution:
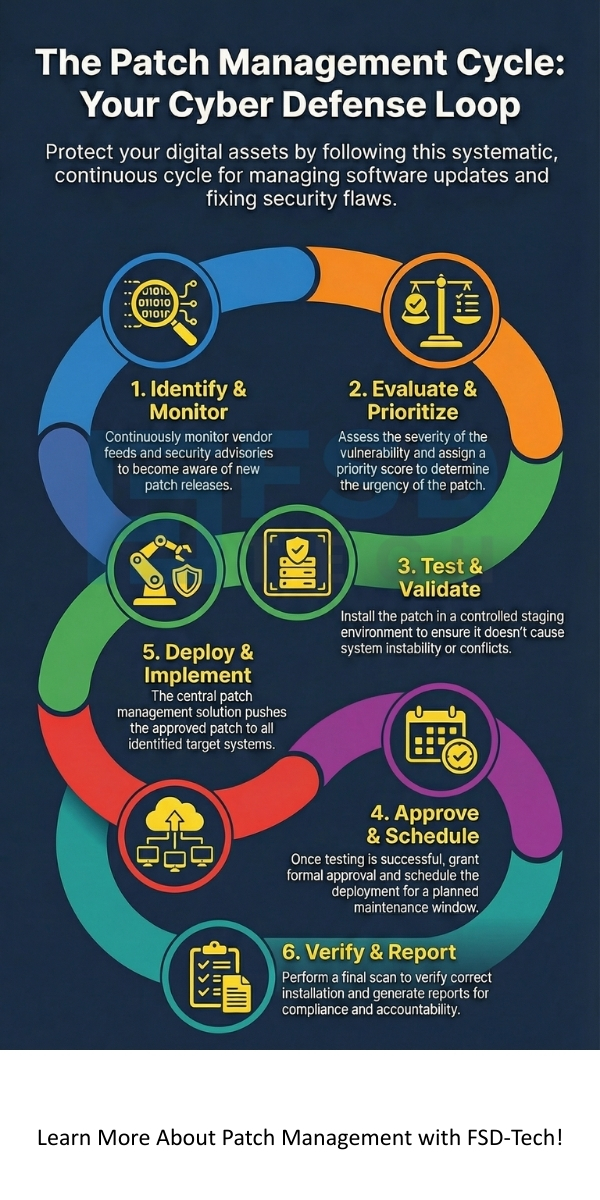
Effective patch management in cyber security follows a structured, continuous cycle. This patch management life cycle ensures that every step, from identifying a need to confirming the fix, is completed systematically.
1. Identify and Monitor New Patches
2. Evaluate and Prioritize
3. Test and Validate
4. Approve and Schedule Deployment
5. Deployment and Implementation
6. Verify and Report
Also Read: What Is Endpoint Detection & Response (EDR) in Cybersecurity?
Security patch management is not just an IT chore; it is a fundamental pillar of modern cybersecurity. Neglecting this function makes your organization a prime target for attacks.
Reduces Security Vulnerabilities
Prevents Financial and Reputational Loss
Ensures System Stability and Performance
Maintains Regulatory Compliance
As businesses shift their infrastructure, the tools for managing patches also evolve. You face a choice between traditional on-premise tools and newer patch management cloud solutions.
On-Premise Patch Management
This traditional approach involves running the patch management server within your own data center.
Patch Management Cloud Solutions
A patch management cloud solution operates as a service provided by a third party.
A good patch management solution offers the flexibility to handle both on-premise and remote assets effectively, regardless of its primary deployment model.
Also Read: Cyber Threat Intelligence (CTI) in Cybersecurity
Choosing the best patch management software and following key practices ensures an optimal and secure patching program.
Key Practices for Success
Many vendors offer comprehensive tools for patch management. These tools provide the necessary automation and reporting capabilities. For example, ManageEngine Patch Management and similar solutions provide features like automated patch testing, centralized control, and deep compliance reporting. Choosing the right tool depends on the size of your network and your specific compliance needs.
So, with the above discussion, we established that what is patch management is clear: it is a continuous, methodical process that acts as your primary defense against evolving cyber threats. You cannot treat it as an occasional task.
A strong patch management system requires defining a clear strategy, utilizing automated patch management tools, and maintaining a focus on all assets, including third party patch management. This systematic approach significantly reduces system vulnerabilities and ensures compliance.
We believe that a secure digital environment enables your business growth. Contact us today; we will help you implement an efficient patch management solution to fortify your systems immediately.
So, with the above discussion, we can say that what is patch management is clear: it is a continuous, methodical process that protects your organization from evolving cyber threats. You cannot treat it as an occasional task.
Here, we address common questions that arise when discussing the deployment of software updates.
The primary patch management meaning refers to the strategic process of installing, testing, and verifying software updates—known as patches—to fix bugs and security vulnerabilities across an entire network of computers and devices.
A patch is a general software update often released as part of a scheduled cycle. On the other hand, a hotfix refers to a small, urgent software update. Vendors release this kind of fix immediately to correct a specific, critical bug or security issue that requires immediate attention.
The answer depends on the severity of new vulnerabilities. For critical security patch management issues, you should patch systems immediately—within hours or days. For non-critical updates, most organizations schedule monthly or quarterly maintenance windows. Your priority must always be to address high-risk vulnerabilities quickly.
When a patch fails, the system must log this failure immediately. The deployment system then typically retries the installation. If it continuously fails, the system flags the machine for manual intervention. This is why having a robust reporting and auditing component is vital.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts