.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
Communication in a computer network happens in various ways. You might send an email to a single friend, or a company might stream a live video to thousands of employees. Each of these scenarios requires a different method of data delivery. Among these, unicast is the most common form of message delivery in networks today. It is the foundation of how we browse the web, send private messages, and access cloud services.
To understand modern networking, one must understand how a single sender talks to a single receiver. In this detailed guide, we will explore the definition, working mechanism, types, and importance of this communication method, with a specific focus on its application in wide area networks.
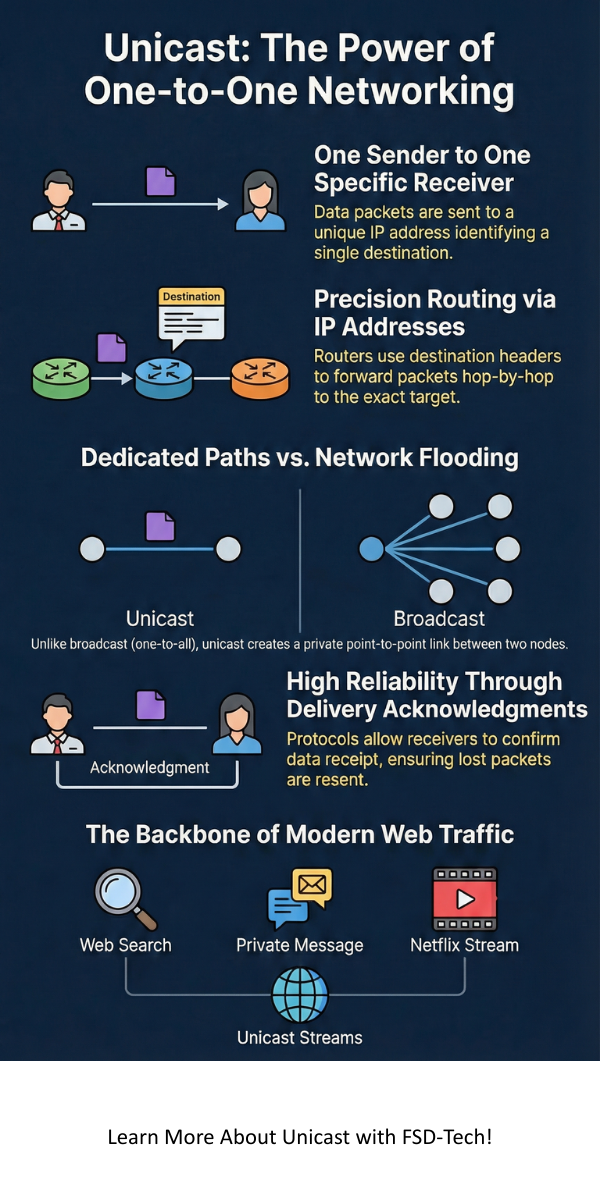
Unicast is a type of network communication where data packets are sent from a single source to a single specific destination. It is a one-to-one transmission method where each destination address uniquely identifies a single receiver in the network.
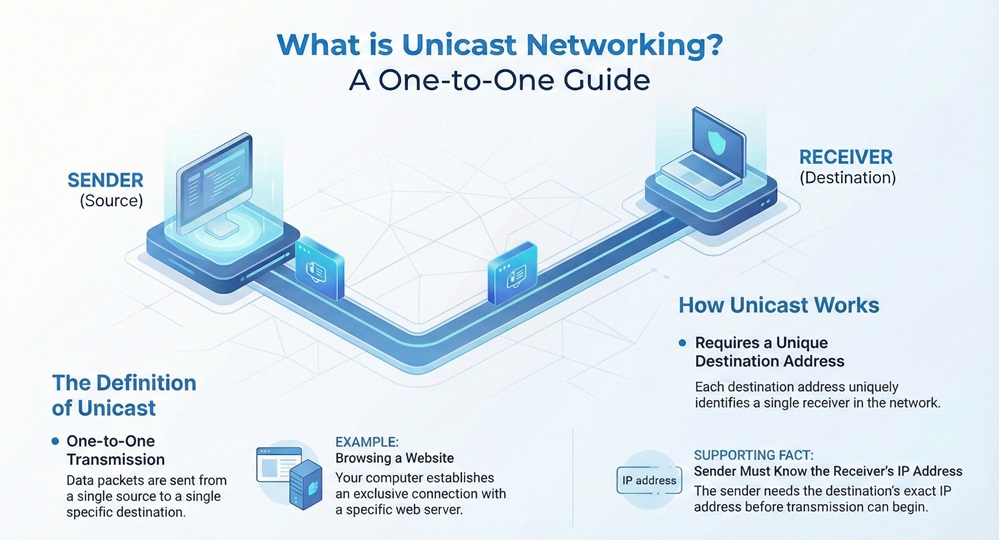
When you enter a URL into your browser, your computer establishes a connection with a specific web server. This is a classic example of a unicast transmission. The network ensures that the data you request goes only to your IP address and not to your neighbor's computer. It involves a point-to-point link, even if the data passes through multiple intermediate routers.
It is noteworthy that in this method, the sender must know the exact IP address of the receiver before the transmission begins. If you want to send a letter to a friend, you need their specific home address; similarly, for a unicast packet to reach its goal, the destination field in the IP header must contain the unique address of the target host.
The working of a unicast system can be understood through the process of addressing and routing. When a device wants to send data, it encapsulates that data into packets. Each packet contains a header that specifies the source IP address and the destination IP address.
Let us discuss the step-by-step process of a unicast transmission:
To be honest, this process happens millions of times a second when you are simply scrolling through a social media feed. Every image or text block you receive is likely delivered via this one-to-one method.
Also Read: What is Throughput? Definition, OS & Networking
To truly grasp the significance of unicast, we must compare it with other transmission methods like broadcast and multicast. While they all move data, the "scope" of the delivery changes significantly.
| Basis for Comparison | Unicast | Multicast | Broadcast |
|---|---|---|---|
| Meaning | One-to-one communication between a single sender and one receiver. | One-to-many communication where data is sent to a specific group of receivers. | One-to-all communication where data is sent to every device on a network. |
| Recipient Count | Exactly one. | Multiple (a specific group). | Everyone on the local segment. |
| Address Type | Individual IP address. | Group/Multicast IP address (Class D). | Broadcast address (e.g., 255.255.255.255). |
| Bandwidth Usage | High if sending same data to many people. | Optimized for group delivery. | Can cause network congestion (broadcast storms). |
| Traffic Direction | Point-to-point. | Point-to-multipoint. | Point-to-everyone. |
Also Read: What is a Wide Area Network (WAN)? Architecture & Types Explained
Now the question arises: what happens when we move beyond our local office network and send data across the globe? This is where wan unicast comes into play.
Wan unicast meaning refers to the delivery of point-to-point traffic across a Wide Area Network (WAN). Unlike a local network where devices might be connected to the same switch, a WAN involves traversing multiple autonomous systems, leased lines, and satellite links.
When we ask what is wan unicast, we are looking at the backbone of internet communication. In a WAN environment, routers use complex protocols like BGP (Border Gateway Protocol) to maintain paths for unicast traffic. Wan unicast ensures that a packet sent from a server in New York reaches a specific laptop in London without being broadcasted to the entire Atlantic cable.
In my experience, managing wan unicast traffic is the biggest challenge for ISPs. Because every single user session (Netflix stream, Zoom call, Web browsing) requires a unique unicast stream, the volume of traffic is immense. If a million people watch a video via unicast, the server must push out a million individual streams. This is quite different from traditional TV, which broadcasts a single signal to everyone.
In modern networking, unicast routing is the process of forwarding a unicast packet from its source to its destination. This is facilitated by routing protocols that "learn" the topology of the network.
Let us discuss the two primary ways unicast routing is implemented:
1. Static Unicast Routing
In this method, a network administrator manually enters the routes into the routing table. This is efficient for very small networks with only one or two paths. However, it doesn't scale well. If a link goes down, the administrator must manually change the route.
2. Dynamic Unicast Routing
Most wan unicast traffic relies on dynamic routing. Protocols like OSPF (Open Shortest Path First) or EIGRP allow routers to communicate with each other. They share information about which networks they can reach. If a path is blocked, the routers automatically calculate a new path to ensure the unicast packet reaches its destination.
Note: Unicast Reverse Path Forwarding (uRPF) is a security feature used in routers to prevent IP spoofing. It checks if the source address of a unicast packet is reachable via the interface the packet arrived on.
Also Read: What is Bandwidth? | Types, Working, and Network Capacity Explained
The reason unicast remains the standard for most applications is its inherent reliability and simplicity in a complex environment.
Despite its dominance, unicast is not always the most efficient choice, especially when dealing with mass media.
Understanding unicast is essential for anyone looking to master the world of networking. It provides the precision and reliability required for the millions of private transactions that happen every second. While newer methods like multicast offer efficiency for group communication, the one-to-one nature of unicast remains the backbone of our digital lives.
Here at our company, we believe in building network infrastructures that prioritize both speed and security. Whether you are setting up a small office or managing a global WAN, choosing the right transmission strategy is the first step toward success. Don't let your data get lost in the noise—ensure your network is optimized for the paths that matter most.
Build a faster network, Contact our experts today!
Yes. When you browse a website using HTTP or HTTPS, you are establishing a unicast connection between your client device and the web server.
Absolutely. Platforms like YouTube and Netflix primarily use unicast. Each user gets a personalized stream, allowing them to pause, rewind, or fast-forward without affecting others.
In unicast, data goes to one specific receiver. In anycast, data is sent to the nearest receiver among a group of potential candidates sharing the same address. Anycast is often used in DNS routing.
For a business, wan unicast is how branch offices communicate with the headquarters. It ensures that sensitive financial data or internal communications are delivered to the correct office and not leaked across the wider network.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts