.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

Data security keeps your private information safe. When you send a message or save a file, you want it to stay private. This is where the process of hiding and revealing data comes into play. You might wonder, what is decryption and how does it protect you?
In simple terms, it is the process of changing unreadable data back into its original form. Without this process, your scrambled data would be useless. Have you ever thought about how your bank keeps your password safe? They use a secret code. But how do you get that information back when you need it?
Let us explore the world of secret codes and how they work. You will learn about the tools used to lock and unlock digital files. By the end of this guide, you will understand what is decryption in computer systems and why it matters to your daily life.
To understand one, you must understand the other. These two processes work together like a lock and a key.
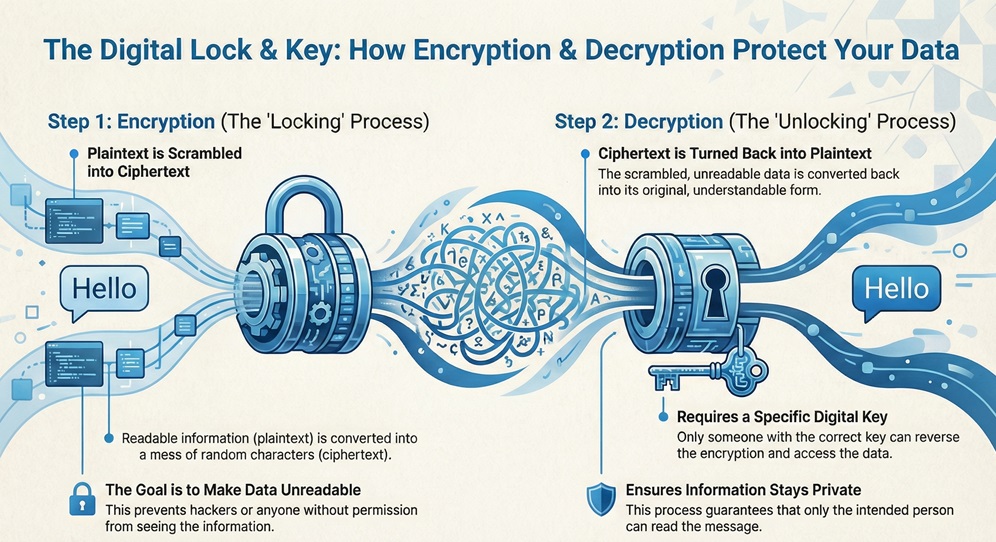
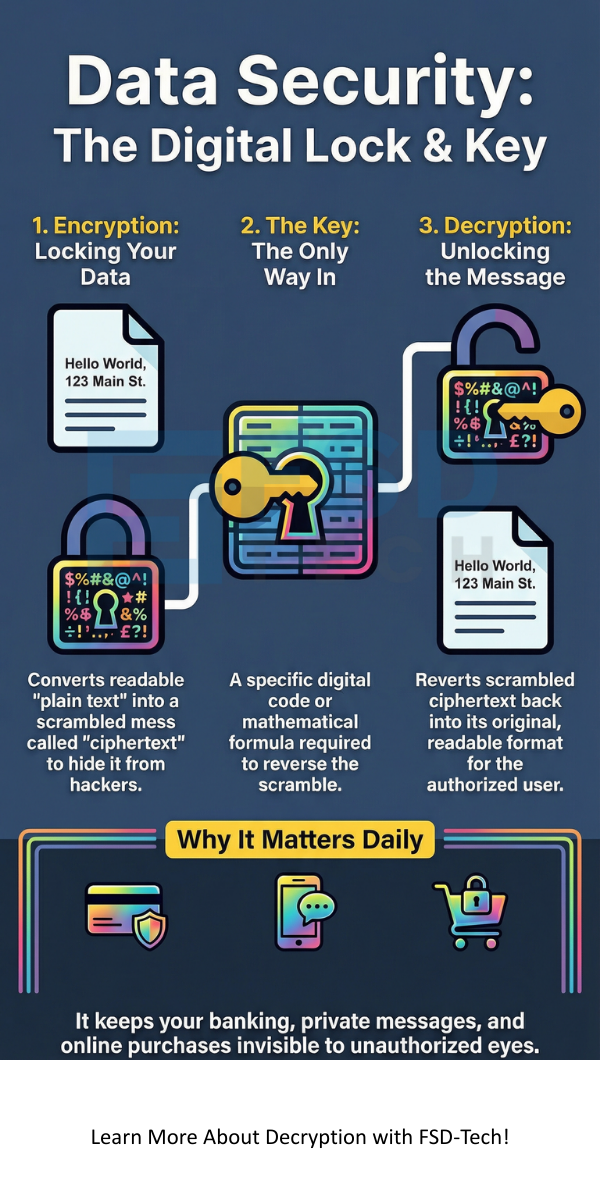
Encryption is the first step. It takes your plain text, like a "Hello" message, and turns it into a mess of random characters. This scrambled text is called ciphertext. The goal is to make the data unreadable to hackers or anyone who does not have permission to see it.
Decryption is the second step. It is the reverse of encryption. It takes that scrambled ciphertext and turns it back into the original message. To do this, you need a specific digital key.
Data decryption is necessary because it allows authorized users to access their information. If we only had encryption, our data would be locked forever. We need a way to read the files we protect.
This process ensures that:
Also Read: What is Asymmetric Encryption? Keys and How It Works
While they are parts of the same system, they serve opposite goals. One hides information, while the other reveals it.
| Basis for Comparison | Encryption | Decryption |
|---|---|---|
| Primary Goal | To hide data from unauthorized users. | To recover original data for authorized users. |
| Input Data | Plain text (readable). | Ciphertext (scrambled). |
| Output Data | Ciphertext (unreadable). | Plain text (readable). |
| Process Timing | Occurs at the sender's end. | Occurs at the receiver's end. |
| Key Usage | Uses a key to lock information. | Uses a key to unlock information. |
| Complexity | Focuses on creating a hard-to-crack code. | Focuses on reversing the specific algorithm. |
When you ask what does decryption mean, you are looking at the final stage of a secure conversation. Think about your smartphone. When you use your fingerprint to open an app, the phone might be unlocking encrypted files.
Decryption signifies the restoration of data. In a computer system, this happens in the background. You usually do not see it working. For example, when you visit a website with a padlock icon in the browser, your computer is constantly revealing the data sent by that site.
Let us look at a basic example of decryption. Imagine you use a simple shift code where every letter moves one spot forward in the alphabet.
In modern computers, these "shifts" are based on complex math and very long numbers called keys.
Also Read: What is API Security and Why it matters for your Business?
Many people ask how decrypt encrypted files is possible if they lose their password. The truth is, it is very difficult by design.
To reveal a file, the computer follows these steps:
If you have the right key, the process is instant. If you do not have the key, you would need to try billions of combinations. This is why strong passwords are so important.
You might not realize it, but you use these tools every hour. Where encryption is used defines how safe the internet feels.
Passwords themselves are rarely stored as plain text. Instead, they are often "hashed" or encrypted. When you ask how decrypt password systems function, you are looking at how a website checks if you are who you say you are.
When you type your password, the site turns it into a code. It then compares that code to the one in its database. If they match, you get in. This protects you because even if a hacker steals the database, they only see the codes, not your actual password.
Also Read: What is Zero Trust Security Model? All You Need to Know
Not all uses of this technology are good. Cybercriminals use these same tools to hurt people. You might wonder which encryption type ransomwares uses to lock your computer.
Most ransomware uses a mix of AES (Advanced Encryption Standard) and RSA.
Ransomware is dangerous because the hackers hold the decryption key. They demand money in exchange for that key. Without it, your files may stay locked forever. This is why backing up your data is the best defense.
There are two main ways that keys work in the digital world. These are Symmetric and Asymmetric methods.
1. Symmetric Key Decryption
In this method, the sender and the receiver use the exact same key. It is fast and simple. However, the big problem is sharing the key. If someone steals the key while you are sending it to a friend, they can read all your secret messages.
2. Asymmetric Key Decryption
This is also known as Public Key Cryptography. It uses a pair of keys.
This is much safer for the internet because you never have to share your private key.
Understanding what is decryption helps you see how the digital world stays safe. It is the vital bridge between hidden data and usable information. From your private chats to your bank account, this process works every second to protect your privacy.
While the math behind it is complex, the goal is simple. It ensures that your data belongs only to you. As hackers get smarter, these methods must become even stronger.
At FSD-Tech, we value the trust of our clients above all else. We stay at the edge of security technology to keep your business safe. Your data deserves the best protection possible. We are here to ensure your digital future remains secure and private. Let us help you navigate the complex world of data security with ease.
Defend with Encryption Talk to a specialist
It is the process of converting hidden or coded information back into a format that a human or computer can read.
Generally, no. Modern security is built to be impossible to break without the specific key. Some experts use "Brute Force" to guess keys, but this can take millions of years for strong codes.
No, it is a standard part of computer science. However, using it to bypass security on files you do not own can be a crime.
Revealing large files requires a lot of math. Your computer's processor has to work hard to run the algorithms, which can sometimes slow down other tasks.
A code replaces whole words with other words. A cipher uses a mathematical algorithm to change individual letters or bits of data.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts