.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

Serverless networking refers to the hidden web of connections that allows code to talk to databases, APIs, and users without you managing a single router. Have you ever wondered how a function that only lives for a millisecond knows exactly where to find your data? It’s a bit like ordering pizza; you don't care about the traffic lights or the delivery driver’s route, you just want the hot slice at your door. In the world of cloud computing, we call this abstraction.
Here is the thing: most people think "serverless" means the infrastructure vanishes. In reality, the networking side becomes more complex because your code is constantly moving. We’ve all been there, staring at a timeout error and wondering why our Lambda function can’t see the database. To be honest, mastering this connectivity is the secret to building apps that don't just work, but actually scale.
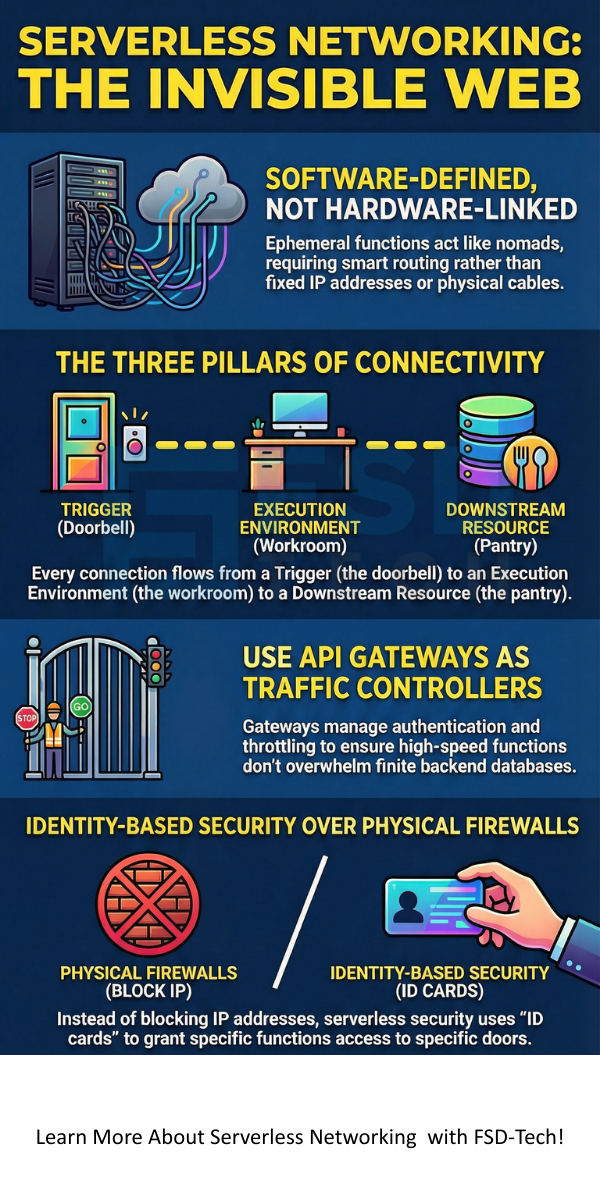
When we discuss serverless networking, we are looking at how cloud providers handle traffic for ephemeral tasks. Unlike a traditional server with a fixed IP address, a serverless function is like a nomad. It wakes up, does a job, and disappears. Because it doesn't have a permanent "home" in a data center, the network must be smart enough to find it every time.
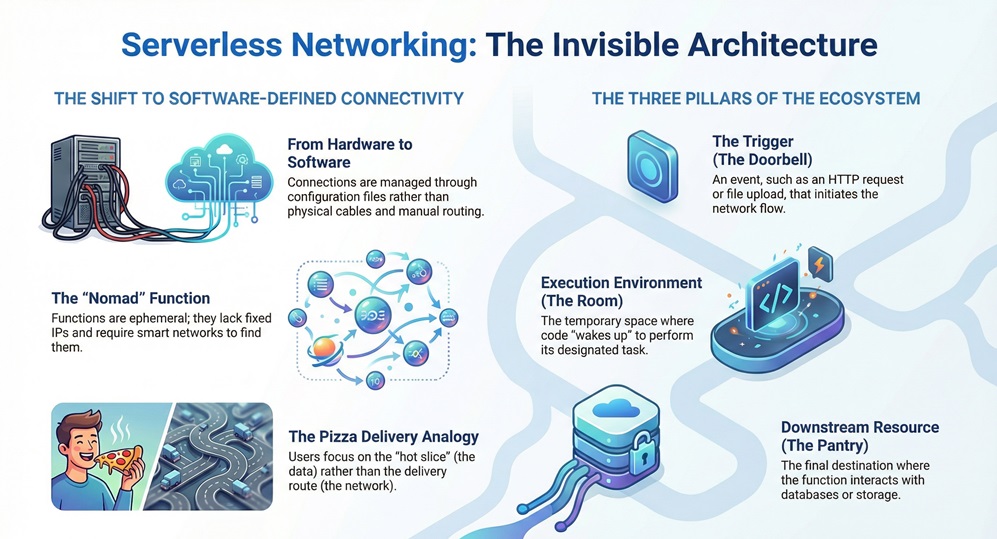
In my view, the biggest shift here is moving from "Hardware-Defined" to "Software-Defined" everything. You aren't plugging in cables. Instead, you're writing configuration files. This shift allows for incredible speed, but it also means you have to understand how Virtual Private Clouds (VPC) and API Gateways interact.
To understand the flow, we need to look at the three main pillars:
A major part of serverless networking involves managing how many "guests" can come into the party at once. In a classic setup, if too many people show up, the server crashes. In a serverless world, the cloud provider just opens more doors. This is called horizontal scaling.
However, there’s a catch. If you open 1,000 doors (functions) but they all try to go through one narrow hallway to your database, the database will break. This is why connection pooling and rate limiting are so vital. We must balance the infinite scale of the function with the very finite scale of the backend.
Also Read: How Remote Browser Isolation Protects Your Team from Web Threats?
Have you noticed a slight delay the first time you trigger a function? That is a "cold start." From a networking perspective, this happens because the cloud provider is busy setting up a tiny network interface for your code. Roughly speaking, this can add anywhere from 100ms to 1 second of lag.
To fix this, providers now use "Pre-warmed" interfaces. Instead of building a bridge every time you want to cross the river, they keep a few bridges ready to go. It makes the user experience much smoother, don't you think?
Most businesses don't want their data sitting on the public internet. This is where the Virtual Private Cloud (VPC) comes in. When we talk about serverless networking, VPC integration is often the most technical part.
Normally, a serverless function sits in a "public" pool. If it needs to talk to a private database, it has to jump into your private network. In the past, this jump was slow. It felt like waiting for a slow elevator every time you needed a file. Luckily, newer technologies like AWS Hyperplane have made this almost instant.
In a world without physical firewalls, how do we keep the bad guys out? We use "Identity-Based" security. Instead of saying "Allow this IP address," we say "Allow this specific user or function."
This is much safer. If a hacker gets into one part of your system, they can't just hop to another part because they don't have the "ID card" for it. It's like having a key that only opens one specific door in a massive hotel. We've all seen news about data leaks; usually, those happen because someone left a door wide open. In serverless networking, the goal is to keep every door locked by default.
Also Read: Network Firewalls vs. Next-Generation Firewalls: Which One Wins?
It isn't all sunshine and rainbows. There are real hurdles we have to jump over. For instance, IP address exhaustion is a real thing. If you launch 5,000 functions in a small network, you might run out of "addresses" for them to use.
Another issue is outbound traffic costs. Cloud providers often charge you when data leaves their network. If your serverless function is talking to an external API millions of times, your bill might give you a heart attack! That’s why we always suggest keeping as much traffic as possible inside the same cloud region.
Pro Tip: Always check your "Subnet" size before launching a massive serverless project. It's better to have too much room than not enough.
Think of the API Gateway as the traffic cop of serverless networking. It sits at the front of your application and directs every incoming request. It handles:
Without a gateway, managing thousands of micro-connections would be a nightmare. It provides a single point of entry, which makes monitoring and debugging much easier for us.
One of the coolest things about this tech is that it reacts to events. Picture this: a user uploads a photo. That event triggers a network signal. The network wakes up a function, which shrinks the photo and saves it.
This "Event-Driven" style means the network is mostly quiet until something happens. It is incredibly efficient. You aren't paying for "idle" time. You only pay for the seconds the electricity is flowing through the digital wires.
| Feature | Traditional Networking | Serverless Networking |
|---|---|---|
| IP Addresses | Static / Fixed | Dynamic / Ephemeral |
| Scaling | Manual / Slow | Automatic / Instant |
| Security | Firewall-based | Identity-based |
| Cost | Fixed Monthly Fee | Pay-per-use |
As you can see, the shift is toward flexibility. While traditional setups give you more "control," serverless gives you more "freedom" to focus on your actual product.
To be honest, the cloud is moving faster than most of us can keep up with. But serverless networking isn't just a fad; it’s the new standard for building fast, lean, and global applications. We've seen how it simplifies scaling and shifts the burden of maintenance away from your team. At our core, we believe in empowering developers to create without limits. We focus on your infrastructure so you can focus on your customers. Are you ready to stop managing cables and start building the future?
No, there are definitely servers! You just don't have to manage them. The cloud provider handles the hardware, while you focus on the logic.
It can be. Because functions are short-lived, a hacker has a very small window to do damage. However, you still need to configure your permissions correctly.
Generally, no. But you can use a "NAT Gateway" if you need to talk to a third-party service that requires a specific IP for whitelisting.
It could be a cold start, or it could be that your function is struggling to connect to a database inside a VPC. Check your networking logs!

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts