.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

Mesh Architecture is the modern answer to the massive data bottlenecks we've all faced in the last decade. To be honest, we’ve spent years trying to cram every piece of company info into one giant, central lake, only to realize it’s nearly impossible to manage. If you've ever waited weeks for a data engineer to build a simple report, you know exactly what I mean.
Here is the thing: the old way of doing things just doesn't scale anymore. In my experience, treating data like a product rather than a byproduct of code changes everything for a growing business. But what does this shift actually look like in practice?
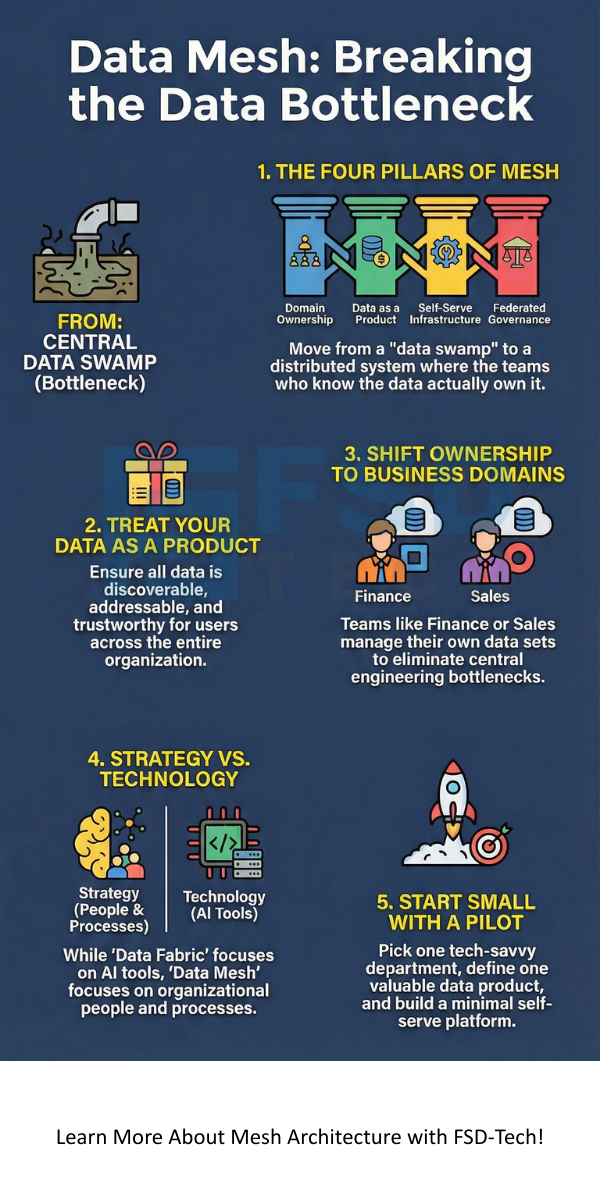
At its heart, Mesh Architecture refers to a decentralized approach where different business units own their own data. Instead of a single central team managing a massive "data swamp," the people who know the data best—like the marketing or finance teams—take responsibility for it.
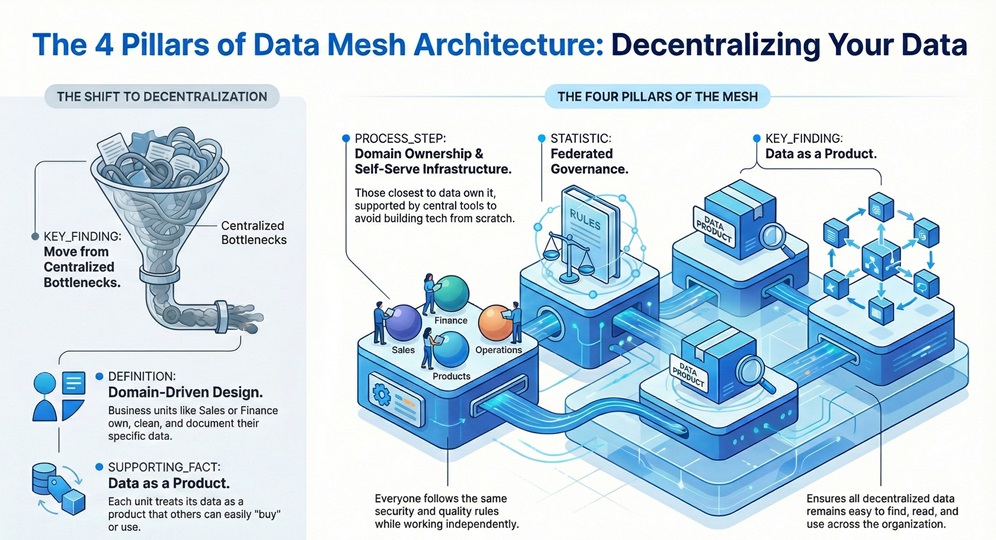
Picture this: your sales team creates sales data, so they should be the ones to clean it, document it, and share it. This shift moves us away from monolithic systems toward a distributed, "domain-driven" design. We call these units "domains." Each domain treats its data as a product that other people in the company can "buy" or use easily.
To truly understand this setup, we need to look at the four main rules that keep it running. Without these, you just have a mess of disconnected databases.
When we talk about Mesh Architecture, we have to talk about domains. In a traditional setup, if the accounting department changes how they label "revenue," the central data team has to scramble to fix every dashboard. It's a nightmare, right?
With domain ownership, the accounting team manages that change themselves. They provide a clean "data product" to the rest of the company. In my view, this is the only way to stay agile. You stop being a victim of "upstream" changes because the experts are in charge of their own output.
Also Read: Network Firewalls vs. Next-Generation Firewalls: Which One Wins?
Treating data as a product is a mental shift. We've all seen spreadsheets with titles like "Final_Report_v2_USE_THIS_ONE.csv." That is exactly what we are trying to avoid.
In a Mesh Architecture, a data product must be "discoverable." This means there's a catalog where you can search for it. It must also be "addressable," meaning it has a permanent spot where you can find it. Most importantly, it must be trustworthy. If the marketing team provides a "Customer Lead" product, they guarantee it’s accurate and updated daily.
"If the user of your data is unhappy, your product has failed."
This mindset forces teams to care about the "customer experience" of someone in another department using their numbers.
You might wonder, "If every team owns their data, doesn't that mean we need 50 sets of data engineers?" Well, not exactly. This is where the self-serve platform comes in.
The central IT team stops moving data and starts building "vending machines." They provide the storage, the compute power, and the security templates. A domain team then uses these tools to build their products. Roughly speaking, the platform team handles the "how," while the domain teams handle the "what."
Can we really trust every team to follow the rules? This is the scariest part of Mesh Architecture for many leaders. We solve this through "Federated Governance."
Think of it like a group of independent countries that all agree to use the same currency and follow the same trade laws. We create a council with members from each domain. They decide on global standards—like how to format a date or how to mask credit card numbers. Then, we bake these rules into the platform so they happen automatically.
Also Read: Database Fingerprinting: Secure Your Data Assets
Let's look at how this plays out in the insurance world. Insurance companies have tons of data: claims, policyholders, risk assessments, and marketing leads.
In a legacy system, these are all tangled together. When the "Claims" team wants to see "Policy" data, they have to ask IT for an export. In a Mesh Architecture, the Policy team publishes a "Policy Product." The Claims team simply connects to it.
I've seen this reduce the time to launch new insurance products from months to weeks. Since the risk models are already built as "products," the actuaries can just plug them into new applications without starting from zero.
To be honest, switching to this model is hard. It's 80% culture and 20% technology. Here are a few things that might trip you up:
Does it feel overwhelming? It can. But compare it to the cost of your business slowing down because no one can find the right numbers. Which is worse?
We often hear these two terms used together. While they sound similar, they are different. A Data Fabric is like a smart layer of software that connects all your data automatically using AI.
On the other hand, Mesh Architecture is about people and processes. You can use a Data Fabric to help build your mesh. One is the tool (Fabric); the other is the organizational strategy (Mesh).
| Feature | Data Mesh | Data Fabric |
|---|---|---|
| Focus | People & Domains | Tech & Metadata |
| Control | Decentralized | Usually Centralized |
| Ownership | Domain Teams | Central IT/AI |
If you're ready to dive in, don't try to change the whole company at once. That's a recipe for disaster.
The shift toward Mesh Architecture represents a major turning point in how we handle information. We are moving away from rigid, central control and toward a flexible, team-centered model. It's about empowering the people who know the data best to share it with the rest of the world.
At our core, we value innovation and client agility above all else. We believe that by giving your teams the right structure, you're not just managing data—you're fueling the next generation of your business. We are here to help you navigate this transition and ensure your data works for you, not the other way around.
Not necessarily. While it's designed for complex organizations, any company with more than three or four distinct departments can benefit from clearer data ownership.
It helps. Cloud tools make the "self-serve" part much easier. However, you can technically build a mesh on-premise, though it requires more manual effort.
Usually, it's a mix. You want a "Head of Data" to facilitate, but the actual rules should be decided by the people from the domains.
Look at "Time to Value." How long does it take for a new team to get the data they need? If that number goes down, your mesh is working.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts