.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
Managed detection and response is a service that handles your security feeds to find potential threats or active breaches. It helps you fix these issues before they turn into a nightmare for your business. Most big security names have an MDR offer. For example, Cato does this, and so do many specialized partners.
But why do you actually need it? To be honest, we have all been there—staring at a screen full of alerts and wondering which one is a real fire. Most teams are tired. They have too many tools and not enough hands. That is where MDR steps in. It combines smart software with real human experts who watch your back 24/7.
In this guide, we will look at how this service works. We will also see how it fits into a SASE platform and why having a human in the loop makes all the difference.
At its heart, managed detection and response (MDR) is about speed. Think of it as a high-tech security guard for your digital office. It does not just watch the cameras; it runs toward the noise to stop the intruder.
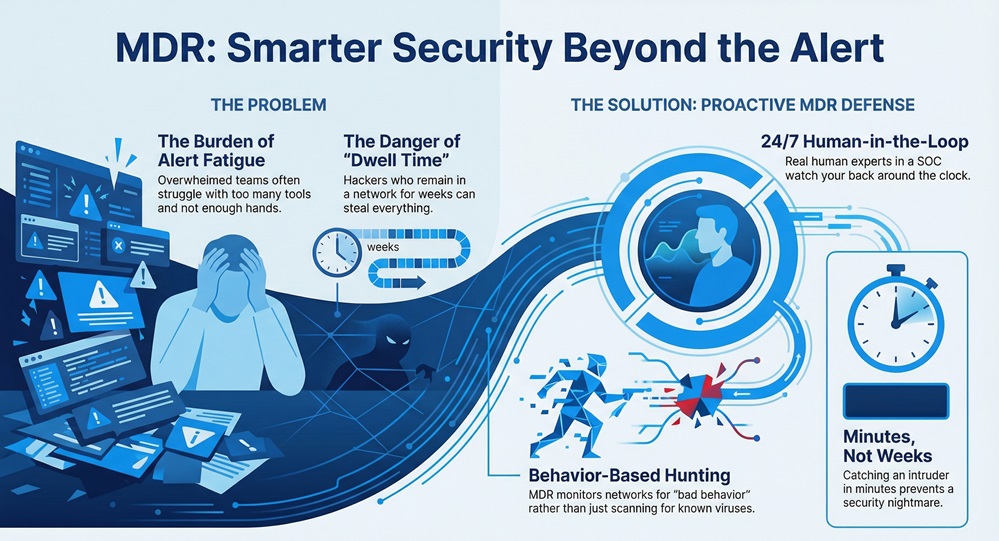
Many people confuse it with standard antivirus. However, it is much more than that. While basic software looks for known "bad files," MDR looks for "bad behavior." It monitors your network, your cloud, and your remote workers.
The main goal is to reduce "dwell time." This is the time a hacker spends inside your network before you catch them. If a hacker stays in for weeks, they steal everything. If you catch them in minutes, you win. Thus, we can say that MDR is your best bet for keeping dwell time low.
Does your current team have the time to hunt for hidden threats every single day? Most don't. That is why offloading this work to a dedicated Security Operations Center (SOC) is a smart move.
When you use managed detection and response, you are buying expertise. You get a team that knows exactly what a real attack looks like. They use Artificial Intelligence (AI) and Machine Learning (ML) to sort through millions of data points.
24x7 Monitoring
Threats do not take the weekend off. Hackers often strike on holidays or at 3 AM. A good MDR service monitors your environment every single minute. This constant eye on the ball ensures that a small glitch does not turn into a total shutdown.
Human Threat Verification
Here is the thing: AI is great, but it can be wrong. It might flag a legitimate software update as a virus. In a Cato MDR setup, the SOC team inspects these "suspicious" flows. They close cases that are just noise. This means you only get a call when the threat is real. Don't you prefer a quiet inbox over one filled with false alarms?
Also Read: What is Managed SD-WAN? All You Need to Know
Most managed detection and response services require you to install a lot of new hardware. You have to put "sensors" everywhere. It takes months to set up. But Cato MDR is built-in to the Cato SASE platform.
Zero-Footprint Data Collection
Since Cato already runs your network, it already sees your data. You do not need to install anything new. Once you get the license, the SOC team starts working. It's like flipping a light switch. You get instant visibility into your sites, VPNs, and cloud environments.
Automated Threat Hunting
We use ML to mine your network for weird patterns. We look at:
By checking these boxes, the system finds infected endpoints that traditional tools might miss.
If you are looking to improve your security posture, MDR offers several big wins. We've seen companies transform their safety levels just by adding this layer.
Monthly Reporting and Tracking
Transparency is key. Each month, you get a custom report. It shows your risk levels, which endpoints were at risk, and how we saved the day. It is a great way to show your boss that the investment is working.
Also Read: Infrastructure Monitoring: Your Guide to a Healthy Tech Stack
You might wonder what happens behind the scenes. To be honest, it is a very structured dance between computers and people.
As we have already discussed, this cycle happens every single day. It removes the burden from your IT staff so they can focus on growing your business.
In this section, we will discuss why old methods are failing. In contrast to MDR, older tools like Managed Security Service Providers (MSSP) often just pass the alerts to you. They are like a "forwarding service."
MDR is more like a "resolution service." While an MSSP tells you that your house is on fire, an MDR team brings the fire truck and helps you put it out. This shift from "watching" to "doing" is what modern businesses need.
| Feature | Traditional MSSP | Cato MDR |
|---|---|---|
| Response | Only Alerts | Alerts + Containment |
| Setup | Complex / Extra HW | Instant / No HW |
| Focus | Logs and Events | Network Behavior |
| Human Element | Limited | 24/7 SOC Experts |
You might think your company is too small for this. However, hackers actually love small businesses because their security is often weaker. Whether you have 50 employees or 5,000, managed detection and response scales with you.
If you struggle with "alert fatigue" or don't have a 24/7 security team, then the answer is yes. It's a way to get "enterprise-grade" safety without hiring ten expensive security engineers.
To sum up, managed detection and response is no longer a luxury. It is a necessity in a world where cyberattacks are constant. By combining smart AI with a dedicated SOC team, you can finally sleep at night. You'll know that if something goes wrong, someone is already fixing it.
At Cato, we value your peace of mind above all else. We are committed to keeping your network clean and your data safe. Our focus is always on the client, ensuring you have the best tools to succeed without the fear of a breach.

Ready to see how we can protect your network? Let's chat about your security needs today.
EDR (Endpoint Detection and Response) is a tool for your computers. MDR is a service that might use EDR tools but covers your whole network and includes human experts.
No, it helps them! It takes the boring, scary work of watching logs off their plate. This lets them focus on high-value projects.
With Cato, monitoring is 24x7. Verification happens daily, and critical threats are alerted and contained almost instantly.
Yes! You get a full dashboard and monthly reports that show every investigation.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts