.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
Protecting your business data today feels a bit like guarding a castle in a world of teleporting spies. You might have the thickest stone walls, but if an intruder can simply "hop" over them using a clever disguise, your defense is just for show. This is exactly why the debate between Network Firewalls vs. Next-Generation Firewalls is so critical for modern IT teams.
We’ve all been there: staring at a complex dashboard, wondering if our current setup actually stops modern threats or just checks a compliance box. To be honest, the "classic" firewall we relied on for decades is struggling to keep up. But how do you know when it’s time to move to an NGFW? And what makes a next-gen solution so different?.
In this guide, we'll break down the technical bits without the headache. We'll explore why simple packet filtering isn't enough anymore and how advanced tools like Cato Networks are changing the game.
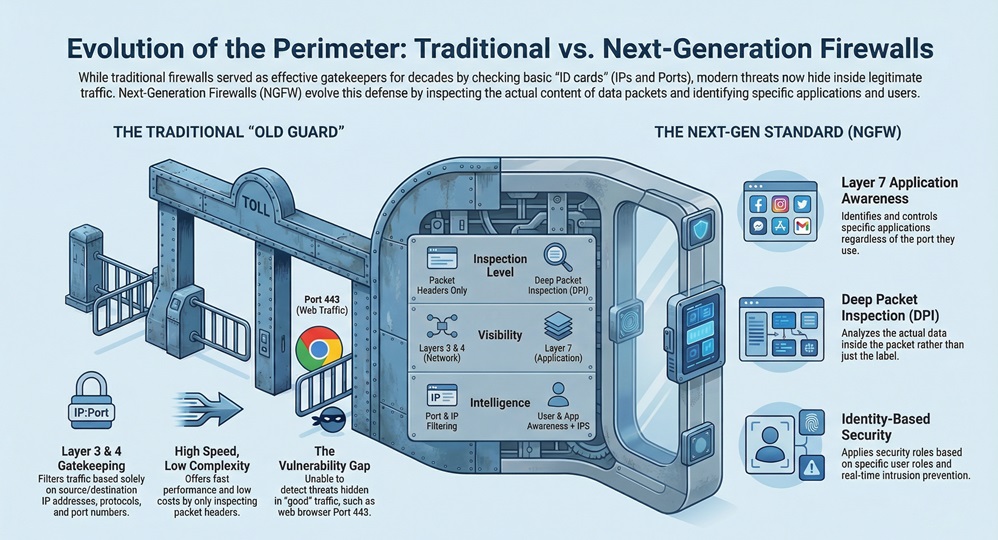
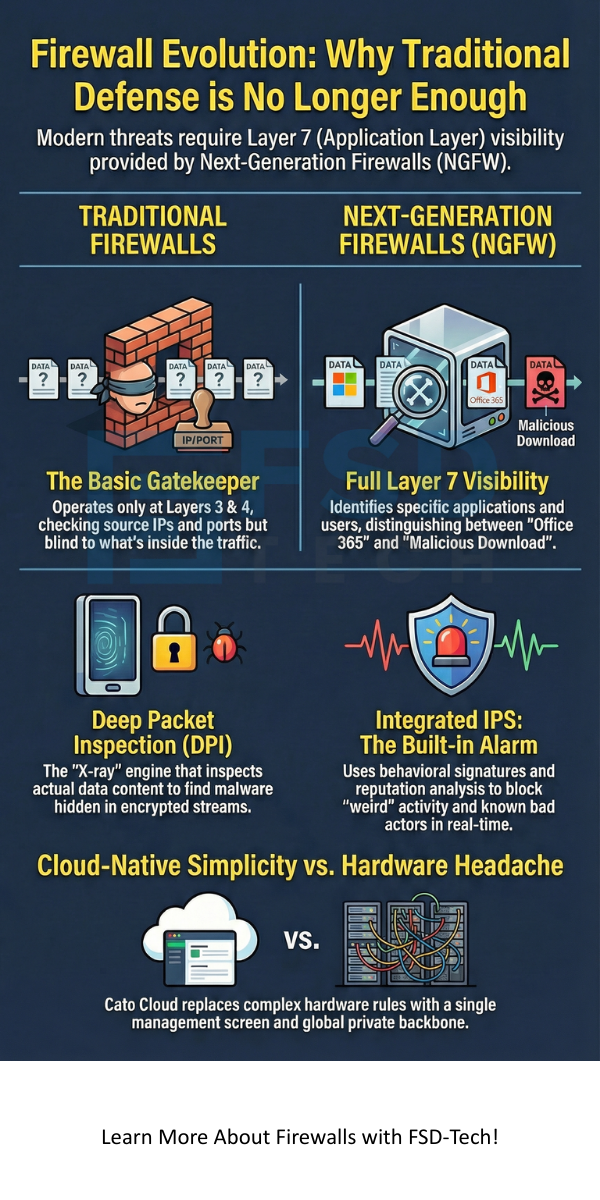
The traditional network firewall is the "old guard" of security. Think of it as a security guard at a gate who only looks at the ID card. If the ID says the person is allowed and they’re coming through the right door (port), the guard lets them in.
Technically, these devices operate at Layers 3 and 4 of the OSI model. They check the source and destination IP addresses, the protocol being used, and the port number.
Also Read: What is Managed Detection and Response (MDR)?
However, here’s the thing: hackers don't use "bad" ports anymore. They hide their attacks inside "good" traffic, like your web browser (Port 443). To a traditional firewall, that looks perfectly fine. Does that sound safe to you?
A Next-Generation Firewall (NGFW) is like that same security guard, but now they have an X-ray machine, a background check database, and the ability to recognize faces. It doesn't just look at the ID card; it looks at what’s inside the person's briefcase.
An NGFW does everything a traditional firewall does, but it adds Layer 7 (Application Layer) visibility. This means it can tell the difference between "Facebook for marketing" and "Facebook for playing games," or "Office 365" and a "malicious file download."
If you’re choosing between these two, you need to see the side-by-side comparison. In my experience, most enterprises find that while a standard firewall works for simple segmentation, it fails at the edge where the internet meets your data.
| Feature | Network Firewall | Next-Generation Firewall (NGFW) |
|---|---|---|
| OSI Layer | Layers 3 & 4 (Network/Transport) | Layers 3 through 7 (Up to Application) |
| Visibility | IP, Port, and Protocol only | Specific Apps and User Identities |
| Inspection | Basic Packet Filtering | Deep Packet Inspection (DPI) |
| Threat Protection | Very limited | Integrated IPS, Anti-Bot, and Sandboxing |
| Encryption | Cannot see inside SSL/TLS | Can decrypt and inspect secure traffic |
We know that managing firewall rules can be a nightmare. Usually, you need a dozen rules just to allow one simple business app. At Cato Networks, we’ve changed that.
The Cato firewall is built into the cloud, making it simple and powerful. We’ve removed the "grunt work" of rule management. Instead of configuring 50 different appliances, you manage everything from one screen.
Also Read: What is Penetration Testing? Guide to Ethical Hacking
Cato uses two specific types of firewalls to keep you safe:
A firewall without an Intrusion Prevention System (IPS) is like a lock without an alarm. Our IPS is built directly into the Cato Cloud, so every bit of traffic gets inspected without slowing you down.
We use several layers of security:
Sometimes people ask, "Can I just use a segmentation firewall?" This is an internal firewall that lives between your subnets. While these are great for stopping a virus from spreading inside your office, they aren't designed to fight off sophisticated external hackers.
In modern networking, we usually suggest a "defense in depth" strategy. Use segmentation for your internal "zones" but rely on an NGFW for your main perimeter.
Choosing between Network Firewalls vs. Next-Generation Firewalls shouldn't be a struggle. While the older tech had its time, the modern "threat landscape" (to use a fancy term) requires more intelligence. You need to see the apps your team uses and the data they send.
At Cato Networks, we believe security should be simple, not a second job. We focus on protecting your people and your data so you can focus on growing your business. We're committed to giving every client enterprise-grade protection without the enterprise-grade headache.
Yes. Most modern attacks target applications (like your browser or email). A traditional firewall simply can't see these. An NGFW is now the baseline for professional security.
On old hardware appliances, yes. However, cloud-native solutions like Cato use a global private backbone to process traffic, meaning you get high security without the lag.
It means the firewall knows who is behind the IP address. Instead of making a rule for "IP 192.168.1.5," you make a rule for "John in Marketing." It’s much easier to manage.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts