.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
Identity governance is the strategic framework that ensures the right people have the right access to the right resources for the right reasons. To be honest, we've all been there: a new hire starts, but they can't log into their email for three days. Or worse, an employee leaves the company, yet their account stays active for months. These aren't just IT headaches; they're massive security gaps.
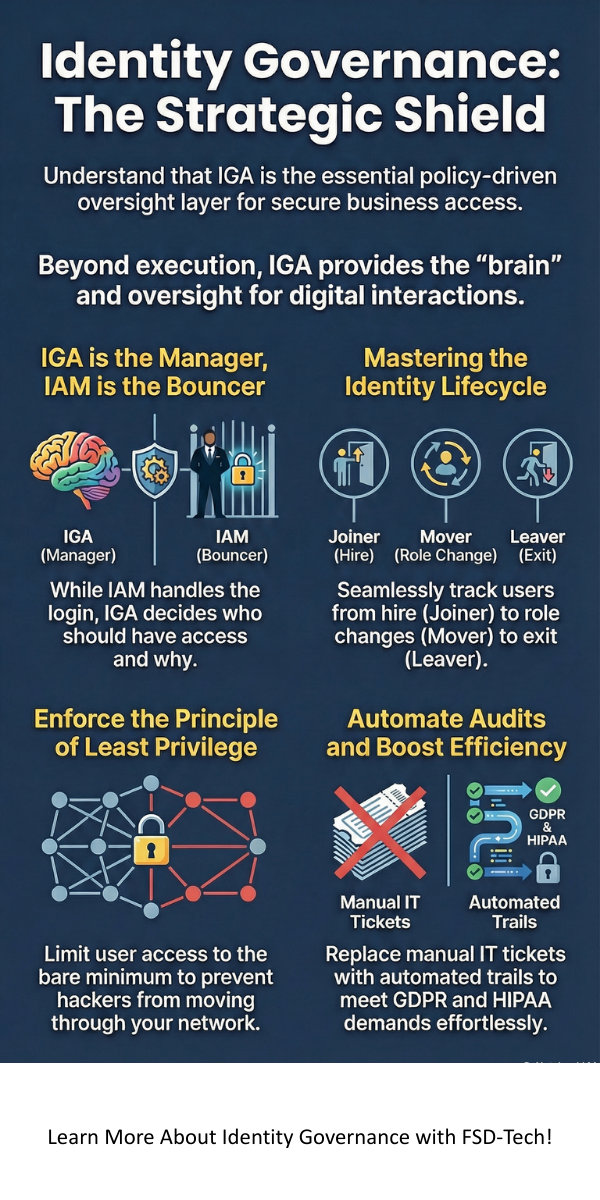
In my experience, many leaders confuse simple logins with true oversight. Think of it this way: if Identity Management is the key that opens the door, then identity governance is the auditor who checks if you should even have a key in the first place. It provides the "who, what, where, and why" of every digital interaction in your network.
As we move through 2026, the digital world is getting crowded. With more apps, remote workers, and even AI bots joining our teams, how do we keep track of it all? Let's explore how this framework keeps your data safe while making life easier for your team.
When we talk about this topic, you'll often hear the acronym IGA. This stands for Identity Governance and Administration. It's a fancy way of saying we're combining technical tools with smart business policies.
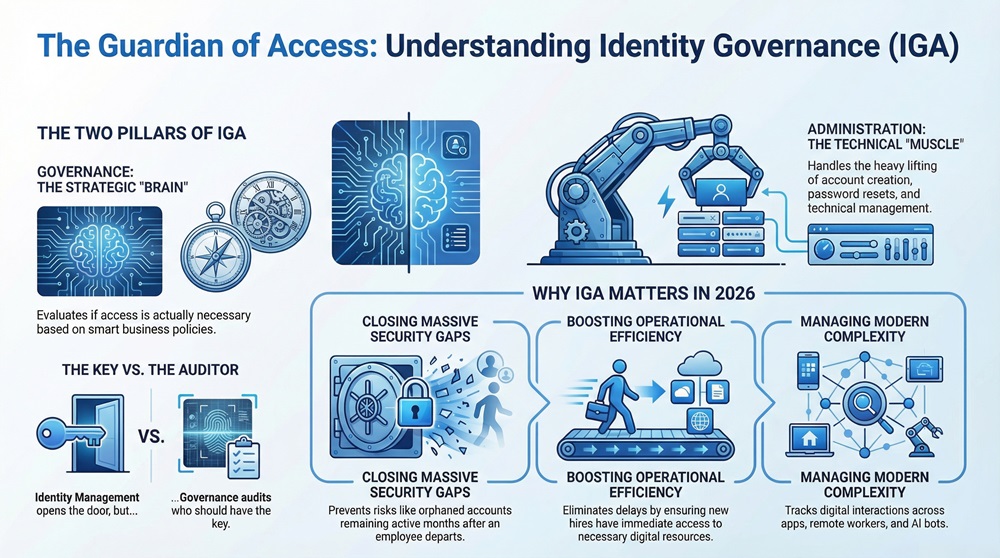
The "Administration" part handles the heavy lifting, like creating accounts or resetting passwords. The "Governance" part is the brain. It asks: "Does this person actually need access to the payroll folder?"
Have you ever wondered why some companies seem to pass audits effortlessly while others scramble? It's usually because they have a solid identity governance strategy in place.
In the past, we relied on a strong "perimeter." We thought if the office walls were secure, the data was safe. Fast-forward to today, and that perimeter is gone. We're working from coffee shops, using personal phones, and connecting to a dozen different cloud services.
Reducing the Risk of Breaches
Most cyberattacks today don't "hack" in; they log in. Hackers use stolen credentials to walk right through the front door. Identity governance limits this risk by enforcing the "Principle of Least Privilege." This means users only get the bare minimum access they need to do their jobs. If a hacker steals a junior designer's password, they shouldn't be able to access the company's financial servers.
Meeting Compliance Demands
Whether it's GDPR, HIPAA, or SOX, regulators are getting tougher. They don't just want to know that your data is safe; they want proof. IGA solutions provide a clear audit trail. You can show exactly who approved a specific permission and when it was last reviewed.
Boosting IT Efficiency
Let’s be real: IT teams are tired of manual tickets. By automating the identity governance process, you remove the "middleman." New hires get their tools on day one automatically. This doesn't just save time—it stops human error from creating "orphan accounts" that attackers love to exploit.
Also Read: What is the Principle of Least Privilege (PoLP)? Guide & Benefits
It's common to hear people use Identity Governance and IAM (Identity and Access Management) interchangeably. To be honest, they're related, but they aren't the same.
| Feature | Identity Management (IAM) | Identity Governance (IGA) |
|---|---|---|
| Primary Focus | Execution and Speed | Policy and Oversight |
| Core Task | Logging people in (SSO/MFA) | Deciding who should be logged in |
| Goal | User Productivity | Risk Mitigation & Compliance |
| Process | Transactional (Add/Remove) | Strategic (Review/Certify) |
Starting an IGA program can feel like climbing a mountain. Roughly 40% of companies struggle because they try to do everything at once. In my view, the best approach is a slow and steady one.
1. Clean Your Data First
You can't govern what you don't understand. Before you buy expensive software, look at your current user list. Are there "ghost" accounts for people who left years ago? Clean up your active directory so your identity governance tools have a fresh start.
2. Focus on High-Risk Areas
Don't worry about every single app on day one. Start with the ones that hold your "crown jewels"—things like customer data or financial records.
3. Involve Business Leaders
This isn't just an IT project. Who knows better than a Sales Manager if a salesperson needs access to a specific CRM folder? Identity governance works best when the people who manage the workers also manage the permissions.
4. Use Automation Wisely
We've all seen automation go wrong. Start by automating simple things, like removing access the moment an HR system marks an employee as "terminated." This is a quick win for security.
Also Read: Security Automation: How to Protect Your Data Without the Burnout
We're seeing a massive shift toward "Identity-First Security." This means identity is now the new perimeter. We're also seeing the rise of "Non-Human Identities"—think of the AI agents and bots that now perform tasks for us. How do we govern them?
Modern identity governance platforms are starting to use AI to spot weird behavior. If a user suddenly requests access to fifty folders they've never used before, the system can flag it instantly. It's about being proactive rather than waiting for an audit to find a problem.
“Identity is the foundation of Zero Trust. Without knowing exactly who is on your network and why, you're just hoping for the best.”
At its heart, identity governance is about trust. It's about knowing that your digital house is in order and that your team has exactly what they need to succeed—nothing more, nothing less. By focusing on smart policies and clear oversight, you aren't just ticking a compliance box. You're building a foundation that allows your business to grow safely in a messy digital world.
Our company believes that security should empower people, not slow them down. We're dedicated to helping you find that perfect balance between airtight protection and seamless productivity. Your security is our focus, and we're here to guide you every step of the way.
An orphan account is a login that no longer has an owner, usually because an employee left the company. These are dangerous because they are often unmonitored and provide an easy entry point for hackers.
Yes! While you might not need a complex software suite, the principles of identity governance—like reviewing access every six months—are vital for any business that handles customer data.
No, but it enforces it. SoD (Segregation of Duties) is a policy that prevents conflicts of interest. Identity governance is the system that makes sure those policies are actually followed.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts