.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
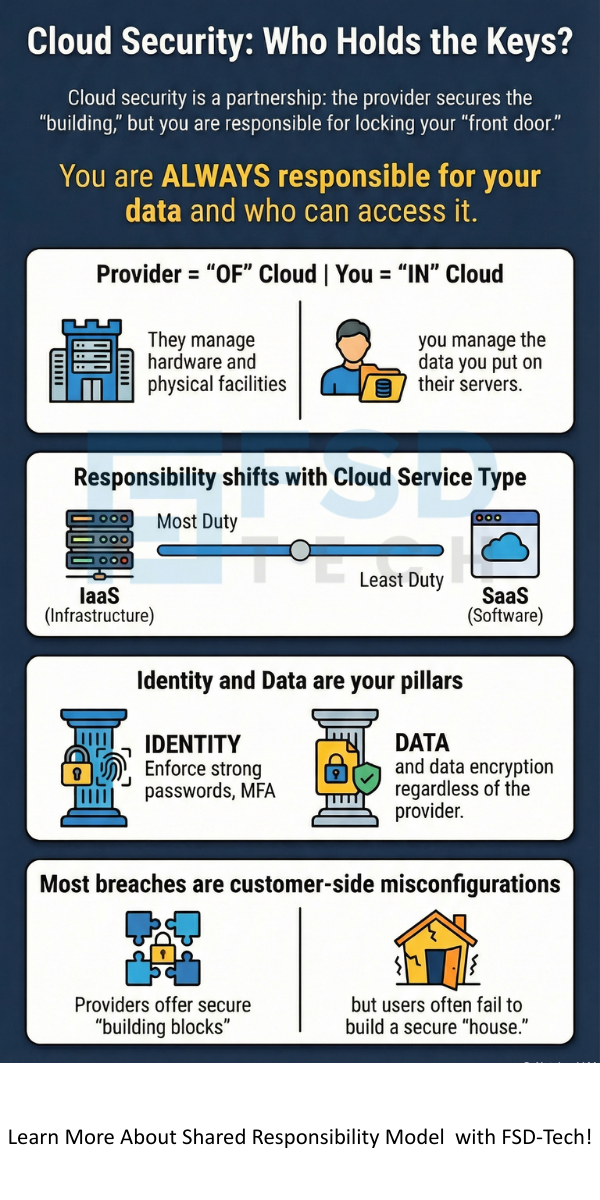
The shared responsibility model is the fundamental framework that dictates who is responsible for security in the cloud. Have you ever wondered if your data is truly safe just because it’s sitting on a world-class server?
Many people assume that once they move to the cloud, the provider handles everything from A to Z. In my experience, this is the biggest mistake a business can make. It’s like renting an apartment; the landlord fixes the roof, but you still have to lock your front door. If you leave it wide open, you can't really blame the building owner for a missing TV, right?
The shared responsibility model works in a very similar way. It draws a line in the sand between what the cloud service provider (CSP) manages and what you, the customer, must handle. This isn't just a technical detail; it’s a legal and operational necessity. If you don't know where the provider's job ends and yours begins, you're leaving your "front door" wide open for hackers.
To be honest, the concept is simpler than most tech blogs make it sound. Every major player, from AWS to Google Cloud, uses a shared responsibility model to keep things organized. They provide the "security OF the cloud," while you handle the "security IN the cloud." That sounds like a catchy slogan, but what does it actually mean for your daily operations?

The CSP takes care of the physical hardware, the power, the cooling, and the actual cables that run the internet. We've all seen those high-tech data centers in photos. They guard those with biometric locks and cameras. However, they don't look at the data you put on their servers. They don't know if your password is "123456" or if you've given access to a former employee. That part is on you.
The shared responsibility model exists because cloud providers cannot control how you use their tools. Think of it like a car manufacturer. They build the car with airbags and anti-lock brakes (security OF the car). But if you choose to drive at night without headlights, that’s a user error (security IN the car).
In the digital world, this means the provider ensures the database software isn't broken, but you ensure the data inside that database is encrypted. We've seen massive data breaches where a company blamed the cloud, only to find out they left a storage bucket public. Don't be that company.
The line of responsibility moves depending on what kind of cloud service you use. We usually talk about three main types: IaaS, PaaS, and SaaS. It's helpful to picture these as a sliding scale. The more the provider does for you, the less you have to manage—but you never reach 0% responsibility.
Infrastructure as a Service (IaaS) gives you the most control. Here, the shared responsibility model puts the heavy lifting on your shoulders. The provider manages the physical stuff, like the servers and the hypervisor. You manage everything else.
If you don't patch your virtual machine's OS, it's your fault if it gets hacked. Does that make sense? It's the most flexible option, but it requires the most "security sweat equity."
Platform as a Service (PaaS) is the middle ground. Developers love it because they don't have to worry about the underlying server. In this version of the shared responsibility model, the provider takes over the operating system and the middleware.
You still have to make sure your code doesn't have bugs that allow SQL injections. The platform is secure, but your specific app might not be.
Software as a Service (SaaS) is like Microsoft 365 or Salesforce. Here, the provider does almost everything. Many people think the shared responsibility model disappears here, but that is a dangerous myth.
Even in SaaS, if your employee's account is compromised because they didn't have Multi-Factor Authentication (MFA) turned on, that's your responsibility. The provider can't stop a user from logging in with a valid (stolen) password.
Also Read: What is Managed SD-WAN? All You Need to Know
Now, let's look at the specific buckets of tasks. No matter which cloud flavor you pick, these categories always come up.
Data Governance and Rights
In every single shared responsibility model, you own the data. This means you are responsible for labeling it, classifying it, and making sure it meets privacy laws like HIPAA or GDPR. The cloud provider is just a vault. They don't decide who gets the key; you do.
Identity and Access Management (IAM)
Who can log in? This is the core of cloud security. We've all seen how easy it is to lose a password. Under the shared responsibility model, setting up strong IAM policies is your job. You must enforce the "principle of least privilege." This means only giving people the access they absolutely need to do their jobs.
Endpoint Security
Are your employees accessing the cloud from a coffee shop on an unencrypted laptop? The CSP can't see that. Protecting the devices that connect to the cloud is a major part of your side of the shared responsibility model. This includes using VPNs and keeping antivirus software up to date.
I've talked to many business owners who feel overwhelmed by this. Let’s clear up some common misconceptions that lead to "cloud anxiety."
Also Read: What is a Secure Web Gateway and How Does It Protect You?
How do you actually implement this without going crazy? Here is a simple plan we often recommend to our partners.
1. Read Your Contract
It sounds boring, but your Service Level Agreement (SLA) is where the shared responsibility model is legally defined. Look for the "Security" or "Compliance" sections.
2. Audit Your Permissions
Check your IAM settings. Are there "ghost" accounts from people who left the company months ago? Cleaning these up is a quick win for your security posture.
3. Use Automated Tools
Many cloud providers offer tools (like AWS Trusted Advisor or Azure Security Center) that tell you if you're failing your side of the shared responsibility model. These tools act like a "security health check."
4. Train Your Team
Human error causes most cloud breaches. Make sure your team knows that security isn't "the IT guy's job." It’s everyone’s job to handle data carefully.
Understanding the shared responsibility model is the first step toward a secure digital future. It isn't about the provider passing the buck; it's about a partnership where both sides do what they do best. By taking ownership of your data and access points, you can enjoy the speed and scale of the cloud without the constant fear of a breach.
At FSD-Tech, we believe that security should be accessible to everyone. We're committed to helping you navigate these complex lines so you can focus on growing your business. Your peace of mind is our biggest priority, and we're always here to help you lock that front door.
If the breach happens in the physical infrastructure or the underlying software they manage, it's on them. They usually have insurance and protocols to handle this. However, if the breach happened because you used a weak password, you are liable.
Yes, but the line shifts even more toward you. In a private cloud, you might even be responsible for the hardware and the cooling systems, depending on the setup.
Use the security frameworks provided by your CSP. They often offer checklists and automated scanners to help you stay on track with the shared responsibility model.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts