.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

A Secure Web Gateway is your first line of defense against the messy world of internet threats. Have you ever wondered how big companies keep their staff from accidentally clicking a link that crashes the whole system? It's not just luck. It's usually an SWG working hard behind the scenes.
To be honest, the internet is no longer a safe neighborhood. In my experience, even the most tech-savvy employees can fall for a clever phishing site. That is where this technology comes in. It sits between your device and the web, checking every site you visit and every file you download. But how exactly does it know what is safe and what is a trap?
The term Secure Web Gateway refers to a security solution that filters unauthorized traffic and malware from user-initiated web access. Think of it as a bouncer at a club. It checks IDs, looks for hidden weapons, and makes sure everyone follows the house rules. If a website looks shady, the gateway blocks it before it can touch your computer.
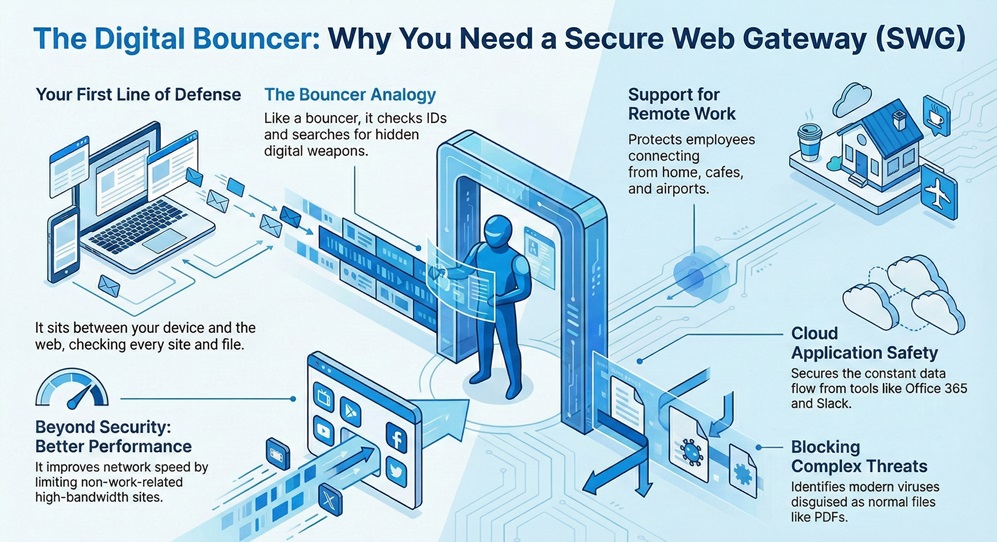
We've all been there—trying to get work done while annoying pop-ups or slow speeds get in the way. An SWG doesn't just block the "bad guys." it also helps your network run smoother by limiting high-bandwidth sites that aren't work-related. This tool has evolved from a simple office box to a powerful cloud service.
The Secure Web Gateway works by inspecting web traffic in real-time. When you type a website address into your browser, the request goes to the gateway first. The gateway then runs a series of checks. Does this site have a bad reputation? Does the file you're downloading contain a virus?
In contrast to old firewalls, which mostly looked at "where" traffic was going, an SWG looks at "what" is inside the traffic. It uses several layers of protection to keep you safe.
1. URL Filtering
This is the most basic job. The SWG keeps a massive list of websites. It categorizes them into groups like "Social Media," "Gambling," or "Malicious." Your company can decide which groups are allowed. If you try to visit a known phishing site, the gateway stops you.
2. Malware Inspection
What happens if a safe site gets hacked? This is a common trick. The gateway uses signatures—like digital fingerprints—to identify known viruses. It also uses "sandboxing." This means it opens a suspicious file in a safe, isolated bubble to see if it starts acting crazy before letting it reach your laptop.
3. Data Loss Prevention (DLP)
Have you ever worried about a teammate accidentally uploading a customer list to a public cloud? DLP is a feature within the Secure Web Gateway that scans outgoing traffic. If it sees credit card numbers or secret project files leaving the building, it can block the transfer.
The Shift to Cloud-Based SWG
In the past, companies bought a physical machine and plugged it into their office. However, that doesn't work well when half the team is working from a beach in Bali. Now, most organizations use cloud-based gateways.
Cloud-native solutions are part of what we call SASE (Secure Access Service Edge). This implies that security follows the user, not the office. Whether you are at your desk or at a coffee shop, the Secure Web Gateway protects your connection through the cloud. This makes it much easier for IT teams to manage because they don't have to fix physical hardware in twenty different locations.
Also Read: Simplifying IT Operations with Cato SASE: Reducing Complexity and Enhancing Performance
When we look at high-end solutions, they offer more than just blocking sites. They provide deep visibility into what is happening on your network.
SSL/TLS Inspection
Most websites today use "https," which encrypts your data. This is great for privacy, but hackers use it to hide their viruses too. A good Secure Web Gateway can "unzip" this encrypted traffic, check it for bugs, and then zip it back up. It’s a bit like a customs officer opening a sealed box to check for contraband.
Application Control
It isn't just about websites anymore. We use thousands of web apps. An SWG can allow you to use LinkedIn for networking but block you from using the chat feature. This level of control is very helpful for staying productive.
Threat Intelligence
The best gateways are connected to a global brain. If a new virus is discovered in Tokyo, your gateway in London knows about it seconds later. This constant updating is why cloud-based systems are so effective.
It is easy to get these two confused. While they both protect you, they do different jobs.
| Feature | Traditional Firewall | Secure Web Gateway |
|---|---|---|
| Primary Focus | Network Ports & IP Addresses | Web Traffic (HTTP/HTTPS) |
| Inspection Level | Packet Level | Application & Content Level |
| User Awareness | Often limited | Deeply integrated with user ID |
| Best For | Blocking unauthorized access | Stopping web-based malware |
As we can see, the firewall acts as the perimeter fence, while the Secure Web Gateway is the security guard checking the contents of every bag coming through the gate.
Also Read: What is SASE? | Secure Access Service Edge Explained
Choosing a gateway depends on your team's size and how you work. If everyone is in one building, an appliance might work. But if you have a global team, a cloud-native SWG is usually the better choice.
Here, the goal is to find a balance between security and speed. You don't want a system so strict that your employees can't do their jobs. In my view, the best systems are "silent." They protect you without you even noticing they are there.
The internet is a vital tool, but it doesn't have to be a dangerous one. By using a Secure Web Gateway, you give your team the freedom to explore the web without the constant fear of a cyberattack. It is about being proactive rather than reactive.
At FSD-Tech, we believe that security should empower your business, not slow it down. We focus on providing simple, powerful tools that protect your most valuable assets—your people and your data. Are you ready to make your web experience safer?
Schedule a Call with Network Expert

A VPN creates a private tunnel for your data to travel through. An SWG is the filter inside that tunnel that checks for viruses. They often work together, but they serve different purposes.
Yes, most corporate gateways log which sites are visited. This is done for security audits and to ensure employees follow company policies.
Absolutely. IT admins can use the gateway to block or limit any web-based application to save bandwidth or improve security.
A proxy is a part of the gateway. The proxy handles the "middleman" connection, while the gateway adds the security features like antivirus and filtering.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts