.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
Perimeter Security refers to the first line of defense used to protect a facility’s boundary from unauthorized access or threats. In my experience working with site managers, many people think a simple fence does the job. To be honest, a fence is just the beginning. True security involves a layered approach that combines physical barriers, smart technology, and clear procedures to keep people and assets safe.
Have you ever wondered why some buildings feel incredibly secure while others look like an easy target? It usually comes down to how well they've planned their outer defenses. When we talk about protecting a site, we aren't just talking about keeping "bad guys" out. We're also talking about safety, privacy, and peace of mind for everyone inside.
At its heart, Perimeter Security is about creating a "buffer zone" between the public world and your private property. Think of it like the walls of a castle. In the old days, you had a moat and a stone wall. Today, we use high-tech sensors, cameras, and reinforced bollards.
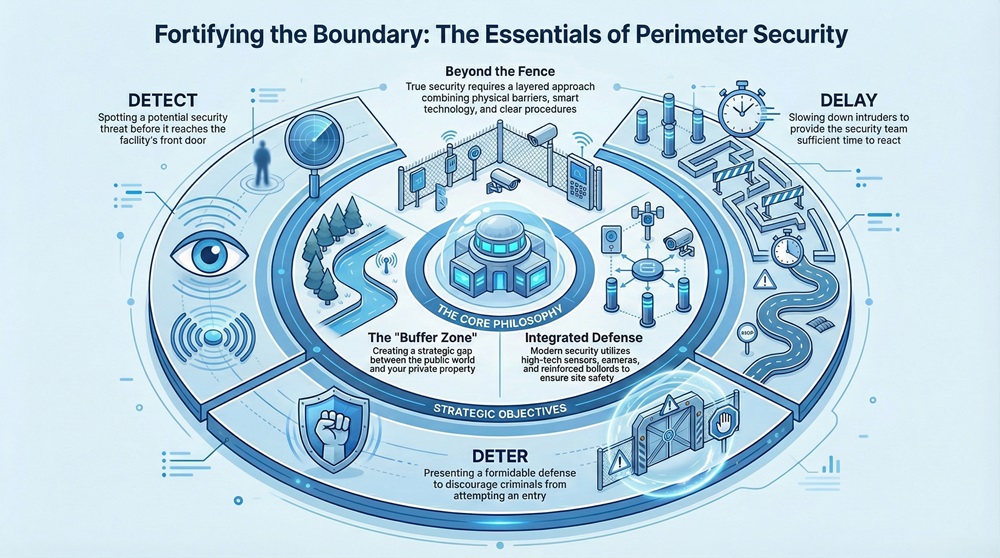
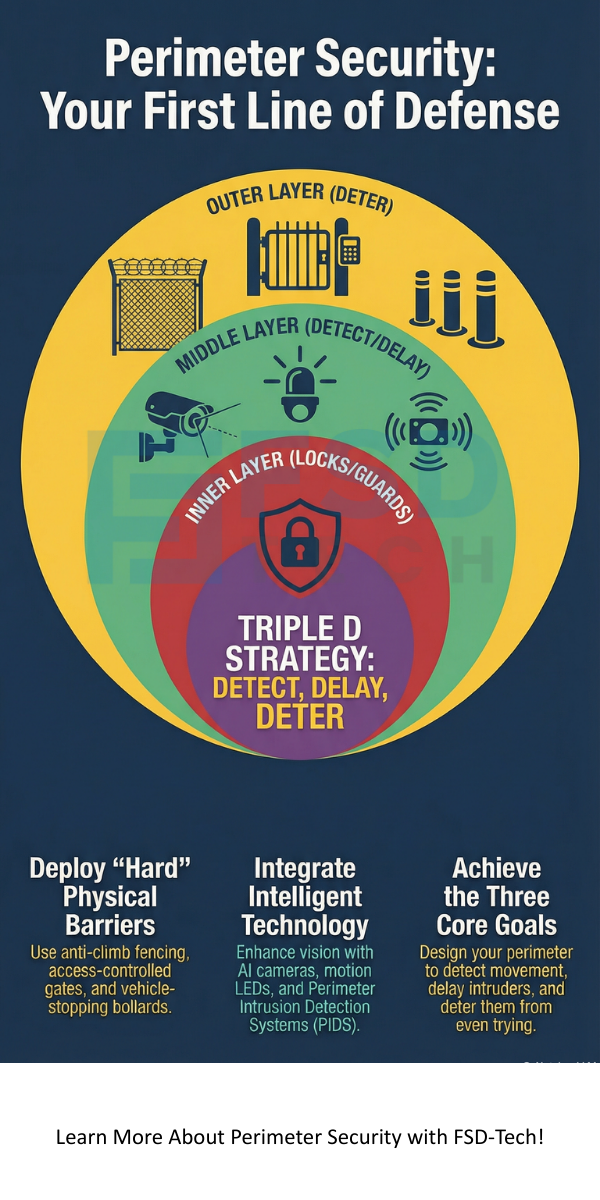
The main goal of PS is simple: detect, delay, and deter. You want to spot a problem before it reaches your front door. You want to slow down any intruders so your team can react. Most importantly, you want to make your site look so difficult to enter that a criminal doesn't even try.
Why do we spend so much money on gates and guards? It's because the perimeter is the most vulnerable part of any site. Once someone crosses that line, the risk to your staff and data goes up by 100%.
In many industries, having a solid security plan is actually a legal requirement. For example, chemical plants or power stations must follow strict rules to prevent sabotage. But even for a standard office building, a breach can lead to stolen equipment or leaked trade secrets. We've all been there—trying to explain to a boss why a laptop went missing over the weekend. A good perimeter plan stops that conversation from ever happening.
When we look at physical security, we usually start with the things you can touch. These are the "hard" assets that block physical movement.
Fencing and Walls
Fences are the most common tool. But not all fences are equal. A chain-link fence might stop a casual wanderer, but a determined intruder will cut right through it. Anti-climb fences with smaller mesh or curved tops are much better.
Gates and Access Points
Every hole in your fence is a potential weak spot. This is where you need "Access Control." We use gates that require a badge or a code. Some sites even use biometrics, like thumbprints, to let people in. It's a bit like a VIP club—if your name isn't on the list, you aren't getting past the velvet rope.
Bollards and Barriers
Have you seen those thick metal posts outside government buildings? Those are bollards. They are designed to stop a vehicle from driving into a building. If a truck tries to ram the entrance, the bollard takes the hit instead of the glass doors.
Also Read: Shadow IT & Unmanaged Devices: The Hidden Risks Draining Your SMB’s Security
Technology has changed the game for Perimeter Security. We no longer rely on a guy with a flashlight walking in circles. Today, we use "Intelligent Perimeter Defense" to watch the lines 24/7.
Surveillance Cameras (CCTV)
Cameras act as your eyes. But modern cameras do more than just record. They use AI to detect movement. They can tell the difference between a stray cat and a person crawling under a fence. This reduces false alarms, which saves everyone a lot of headaches.
Perimeter Intrusion Detection Systems (PIDS)
PIDS are sensors that live on or near your fence. Some detect vibrations—if someone tries to climb the fence, the sensor feels it. Others use fiber optics or buried cables to sense pressure on the ground.
Lighting
Never underestimate a good light bulb. Criminals love the dark. By using motion-activated LEDs, you take away their cover. It's one of the cheapest and most effective ways to boost your security.
In the security world, we often talk about "Defense in Depth." This means you don't put all your eggs in one basket. If one layer fails, the next one should catch the threat.
Does your current site have more than one layer? If someone jumps your fence, is there anything else stopping them from reaching your main office?
Here’s the thing: no system is perfect. One of the biggest issues we face is "False Alarms." If your alarm goes off every time the wind blows, your guards will eventually stop checking it. This is why choosing the right tech for your specific environment is so important.
Another challenge is the "Human Factor." You can have the best gates in the world, but if an employee props a door open to go have a smoke, your security is gone. Training your team is just as important as buying fancy gear.
Also Read: The Top 5 Cybersecurity Myths That Are Putting SMBs in Danger
Before you buy a single camera, you need to know what you are protecting. Ask yourself these questions:
In my view, you should always plan for the "worst-case scenario." Roughly 80% of security is preparation. The other 20% is reacting when things go wrong.
Securing your boundaries is about more than just buying gadgets. It’s about creating a smart, layered system that makes it too difficult for anyone to cause trouble. By combining strong physical barriers with modern surveillance technology, you create a safe environment for your business to grow.
At our company, we believe that every client deserves a tailored solution. We don't believe in "one size fits all" security. Our focus is always on your specific needs and the safety of your people. We've spent years helping sites like yours stay protected, and we're ready to help you too.
It depends on your budget, but anti-climb 358 mesh fencing is generally considered the gold standard for high security. It’s hard to cut and nearly impossible to grip for climbing.
Yes. Lighting increases the "risk of detection." Most criminals prefer targets where they can stay hidden. Sudden, bright motion lights are a huge psychological deterrent.
Not at all. Small businesses and even residential homes use these principles. A smart doorbell, a locked gate, and good porch lights are all forms of Perimeter Security.
PIDS stands for Perimeter Intrusion Detection Systems. These are sensors (vibration, infrared, or microwave) that alert security teams the moment someone touches or crosses a boundary.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts