.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

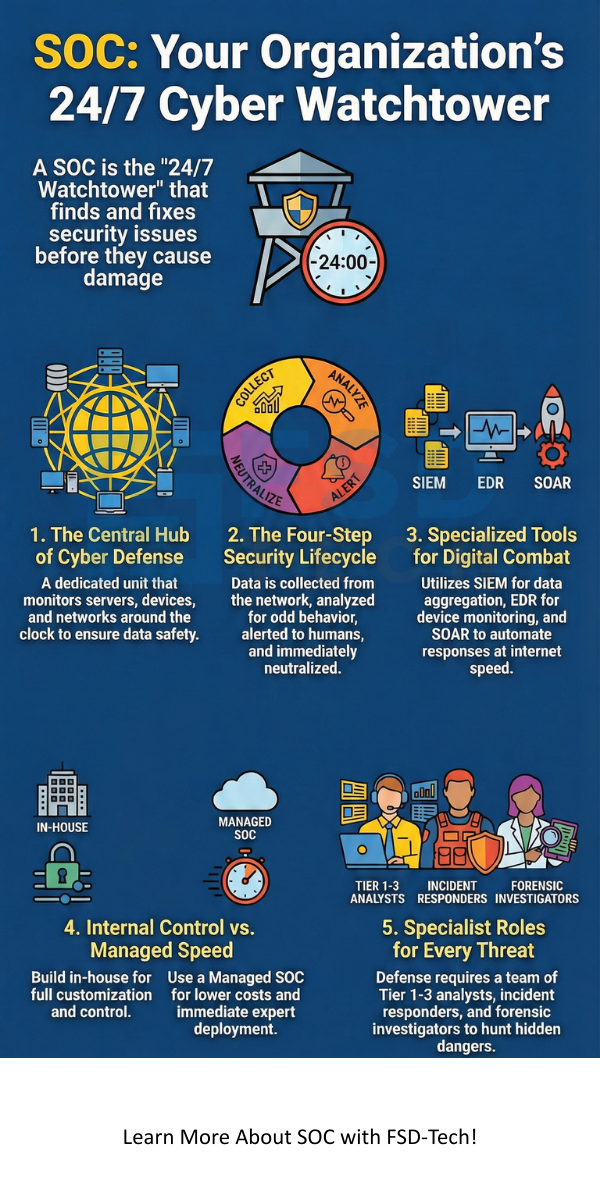
The digital world faces more threats than ever before. You might wonder how large companies keep their data safe around the clock. The answer lies in a specialized hub known as a Security Operations Center (SOC). This unit acts as the central command post for an organization's defense. It is not just a room full of screens; it is a blend of people, refined processes, and high-end technology.
Security operations center soc teams work to find and fix security issues before they cause damage. They monitor everything from servers to mobile devices. But what really goes on inside these centers? How do they stay ahead of hackers?
Let us explore how these centers function and why they are vital for modern business safety.
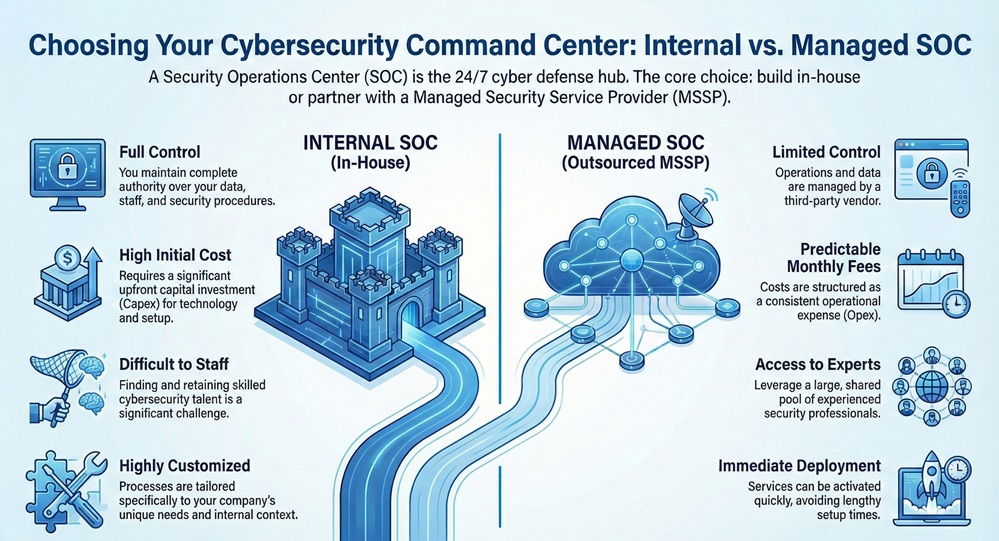
When you decide to implement a cyber security operations center, you must choose between building one in-house or hiring a service. The following table highlights the key differences:
| Basis for Comparison | Internal SOC | Managed SOC (MSSP) |
|---|---|---|
| Control | Full control over data and staff. | Limited control; third-party managed. |
| Cost | High initial investment (Capex). | Predictable monthly fees (Opex). |
| Staffing | Hard to find and keep skilled talent. | Access to a large pool of experts. |
| Customization | Tailored to specific company needs. | Standardized processes for many clients. |
| Setup Time | Can take months or years to build. | Immediate deployment. |
| Knowledge | Deep understanding of internal context. | Broad knowledge of global threats. |
A security operations center soc is a central facility where an information security team monitors and analyzes the security posture of an organization. The primary goal is to detect, analyze, and respond to cybersecurity incidents. You can think of it as a 24/7 watchtower for the company's network.
Security operations center soc units do not focus on building security policies. Instead, they focus on live operational tasks. They collect data from across the network, including firewalls, Windows event logs, and antivirus software. By looking at all this data in one place, the team can see patterns that indicate a cyber attack.
Get started with our SOC services
Security operations center soc functions rely on constant data collection. The team uses a tool called a Security Information and Event Management (SIEM) system. This tool aggregates logs from every corner of the IT environment.
Does your current setup catch every small anomaly? Most basic setups fail here. A dedicated cyber security operations center ensures that no alert goes unnoticed.
Also Read: What is Cloud Access Security Broker (CASB)?
How to build security operations center capabilities starts with a clear strategy. You cannot simply buy software and expect it to work. You must align your security goals with your business needs.
Building security operations center teams requires finding the right balance of Tier 1, 2, and 3 analysts. Tier 1 analysts handle the initial alerts. Tier 2 analysts deal with deep investigations. Tier 3 analysts are threat hunters who look for hidden dangers.
Building security operations center environments also involves physical considerations. You need a secure space with backup power and redundant internet lines. This ensures the center stays online even during a local disaster.
Security operations center processes are the lifeblood of the unit. Without clear steps, the team would be overwhelmed by "alert fatigue." Effective processes ensure every incident follows a standard path from discovery to resolution.
Security operations center processes typically include:
Are your teams following a repeatable manual? If not, you risk missing critical steps during a high-pressure breach.
Also Read: What is Dynamic Application Security Testing (DAST)?
Security operations center tools provide the technical muscle needed to fight cybercrime. The SIEM is the most important piece, but it is not the only one. Modern centers use a variety of specialized software.
SOC tools often include:
Using a cyber security operations center without automation is like fighting a fire with a tea cup. You need tools that can act at the speed of the internet.
A GSOC is a larger version of a standard SOC. It manages security for companies that operate in multiple countries. It handles both digital threats and physical security risks.
What is global security operations center management like? It involves coordinating across different time zones and languages. A global security operations center might monitor cameras at a warehouse in Germany while defending a server in Singapore.
Global security operations center setups offer a "follow-the-sun" model. This means as one team finishes their day in India, the team in the United States takes over. There is never a gap in coverage.
Global security operations center teams also have a wider view of the threat landscape. If an office in London sees a new type of virus, the GSOC can protect the Tokyo office before the virus even reaches them.
Does your business have offices in multiple regions? If so, a localized security approach might leave gaps that a global security operations center would fill.
Also Read: What is Security Information and Event Management (SIEM)?
A cybersecurity operations center is no longer a luxury for big banks. Small and medium businesses are now frequent targets. Hackers know that smaller firms often have weaker defenses.
Cybersecurity operations center teams provide the expertise that most IT departments lack. While your IT staff focuses on keeping the internet running and the printers working, the SOC focuses only on defence. This specialisation is the only way to stop sophisticated "Advanced Persistent Threats."
A successful security operations center soc relies on specific roles. Everyone must know their job when a crisis hits.
Building security operations center facilities is a complex task. One of the biggest hurdles is the cost of the software. SIEM licenses can cost thousands of dollars per year based on the amount of data you process.
Another challenge in building security operations center teams is the talent gap. There is a global shortage of cybersecurity experts. You might find it hard to hire enough people to cover night shifts and weekends. This is why many companies turn to hybrid models, using their own staff during the day and a managed service at night.
The cyber security operations center is changing. Artificial Intelligence is now helping analysts find threats faster. Instead of looking at thousands of alerts, the AI groups them into a single story. This lets humans focus on the most dangerous problems.
As more companies move to the cloud, the security operations center soc must adapt. It must now monitor AWS, Azure, and Google Cloud alongside physical offices. The "perimeter" of the office has vanished, so the SOC must watch everything, everywhere.
Protecting your company's future requires more than just a firewall. It requires the constant vigilance that only a security operations center can provide. Whether you choose to invest in building security operations center teams internally or partner with experts, the goal remains the same: staying one step ahead of the threat.
At our core, we believe that security is a right, not a privilege. We focus on building long-term partnerships with our clients to ensure their digital assets remain untouchable. Your peace of mind is our primary metric for success. We are here to simplify the complex world of cyber defense so you can focus on growing your business.
Contact us now to start building your dedicated cyber security operations center.
A Network Operations Center (NOC) focuses on uptime and performance. They make sure the network is fast. A security operations center focuses on security. They make sure the network is safe from intruders.
Yes, through a Managed Security Service Provider (MSSP). You pay a subscription fee instead of building security operations center infrastructure yourself.
The core tools are SIEM, EDR, firewalls, and threat intelligence feeds. Many teams also use SOAR to automate their security operations center processes.
To cover three shifts every day, you typically need at least 8 to 12 analysts. This accounts for vacations, sick days, and training time.
A false positive is an alert that looks like an attack but is actually normal activity. For example, a new software update might look like a virus to a basic scanner.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts