.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

A Next Generation Firewall (NGFW) refers to an integrated network security platform that combines the features of a traditional firewall with advanced capabilities like application awareness and deep packet inspection.
This technology is essential for modern businesses and organizations in places like the UAE and the wider GCC region, as it provides a robust defense against today’s complex and evolving cyber threats. The primary function of a Next Generation Firewall is to enforce security policies at the application level and block modern threats, not just simple port or protocol violations.
A Next Generation Firewall consists of several key elements that work together to provide comprehensive network security. The two essential components are the traditional firewall functions (like stateful inspection) and advanced inspection techniques. It also includes features such as Intrusion Prevention Systems (IPS) and Deep Packet Inspection (DPI).
This combination connects directly to the practical need of companies to manage risk, ensure compliance, and protect sensitive data in a world of cloud computing and remote access.
In this section, we will discuss the Next Generation Firewall in detail along with its components, working process, and advantages. Understanding this advanced security tool is crucial for anyone managing cybersecurity today. Let us now understand how this technology helps secure businesses.
Next Generation Firewall technology can be defined as a security solution that goes beyond basic port and protocol filtering to include deep packet inspection (DPI), application control, and intrusion prevention. This kind of advanced security is vital because simple, older firewalls cannot keep up with sophisticated cyberattacks. Modern cyber threats hide in legitimate applications, which makes simple network security rules useless.
NGFW technology matters greatly for all companies, whether they are in Dubai or any other major Gulf city. These firewalls provide visibility into the data moving across the network. Moreover, the NGFW looks at the content of the data, not just where it is going. This ability to see and understand traffic at a deeper level is what truly defines the NGFW.
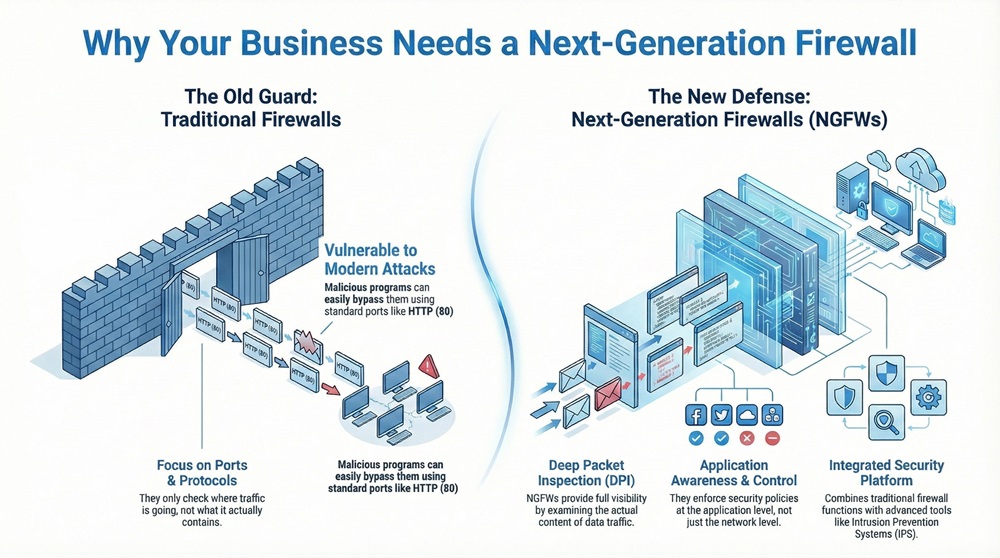
Why do older firewalls fail against today's attacks? The problem is that many malicious programs now use standard ports like HTTP (Port 80) or HTTPS (Port 443). A traditional firewall will allow this traffic because the port is correct, even if the content is harmful. Next Generation Firewall solves this issue by examining the traffic’s actual application and content, not just the port number.
Get Started with Next-Gen Firewall Protection!
The construction of NGFW involves bringing together different security functions into one device or platform. This single-platform approach provides better security and easier management for network administrators. It is composed of both hardware and software elements working together to inspect all data that passes through the network perimeter.
The major components are:
The working of NGFW is a multi-step process that applies different security controls at various layers of the network stack. It starts with the basic firewall function and then moves to the more advanced security checks. This layered inspection is what provides superior protection.
The process occurs as follows:
Simply put, a Next Generation Firewall acts as a very strict security guard. It does not just check the person's ID, but also what they are carrying and what they plan to do inside the building. This comprehensive check makes the NGFW an essential internet security tool.
Also Read: Domain Spoofing Explained: How It Works & How to Stop It
The distinguishing characteristics of NGFW make it a powerful upgrade over traditional solutions. These features provide a holistic security approach necessary for modern, complex networks. These points make the Next Generation Firewall a fundamental part of any robust information security strategy.
Following are the key characteristics:
You should know that there are different types of NGFW deployment to fit various network security needs. The choice of deployment depends on the company size, the type of network infrastructure, and whether the company uses cloud services.
Hardware NGFW is a physical appliance installed at the edge of the network. This appliance handles high data throughput and is common for large enterprises in the Gulf Cooperation Council (GCC) area.
The hardware deployment is often used by companies that need maximum performance and control over their physical network. These devices are purpose-built to execute all the advanced functions like DPI and IPS with very little slowdown.
Virtual NGFW is a software application that runs on a virtual machine (VM) within a server. This type is very popular for companies using cloud computing or having many smaller branch offices.
This deployment option offers great flexibility and scalability. You can easily spin up a new virtual firewall instance to protect a new application or server in the cloud, which is key for modern, agile business operations.
Cloud-Based NGFW is a Firewall-as-a-Service (FWaaS) model where the firewall functions are provided by a cloud provider. You do not manage the hardware or software updates.
This method is excellent for businesses that want security that follows their users wherever they go. It simplifies security management for remote workers and multi-cloud environments, a growing trend in the IT security landscape.
Also Read: What is a Firewall as a Service (FWaaS)?
The advantages of Next Generation Firewall are clear when you look at the challenges of securing a modern network. The integrated and intelligent nature of the NGFW offers protection that older technology cannot match.
While powerful, the Next Generation Firewall also has some disadvantages of NGFW that companies should consider before deployment.
Also Read: What is an Intrusion Detection System (IDS)? Components and Types
The applications of Next Generation Firewalls are broad, making them suitable for almost any organization that needs robust internet security. Their ability to manage traffic at the application layer makes them useful in many scenarios.
Let us consider an example. Suppose a bank in Abu Dhabi needs to ensure that only its approved trading application can access certain external financial markets, even if an employee tries to use a forbidden application on the standard web port. The Next Generation Firewall can enforce this rule perfectly, blocking the unauthorized application while allowing the approved one.
A Next Generation Firewall is a vital tool for any organization serious about cybersecurity. It goes far beyond the capabilities of older firewalls by bringing together key functions like Application Control, Deep Packet Inspection, and Intrusion Prevention into one integrated solution. This advanced capability is no longer a luxury but a requirement for defending against today's sophisticated and often hidden cyber threats.
Therefore, understanding the Next Generation Firewall is the first step toward building a truly resilient network security system. Its features offer the necessary visibility and control to protect valuable assets in a complex IT environment.
Furthermore, the move toward cloud-based security makes the NGFW adaptable to any modern business structure, ensuring your protection remains effective regardless of where your data or users are located.
We are committed to helping you implement the most effective and advanced security solutions, such as the Next Generation Firewall, tailored to your unique business needs, whether you are securing a local office or a large regional operation across the UAE and the GCC.
We provide expert guidance to make sure your network security is not just compliant, but truly capable of defending your future. Reach out to us today to explore how we can strengthen your network defenses.
Here are the five essential points to understand about Next Generation Firewalls (NGFW):
An NGFW is a deep-inspection firewall that combines the functions of a traditional firewall (stateful inspection) with advanced security features like Application Control, an integrated Intrusion Prevention System (IPS), and Threat Intelligence feeds. Its purpose is to detect and block modern threats that evade basic firewalls.
A traditional firewall only inspects traffic headers (source, destination, port). An NGFW adds Deep Packet Inspection (DPI) to inspect the entire packet payload, identifying the actual application and content, regardless of the port used. This allows it to enforce policies based on the application and user, not just the network address.
DPI is the process where the NGFW examines the data portion of a packet as it passes through the firewall. It is important because it allows the firewall to identify malware, viruses, and the true application in use, even if that application is using a common port like 80 or 443 to sneak past basic filters.
Yes, a built-in, integrated Intrusion Prevention System (IPS) is a mandatory feature of an NGFW. The IPS actively scans network traffic against a database of known threat signatures and immediately blocks malicious attempts like network exploits or buffer overflows.
Absolutely. Application Control is a key feature. An NGFW can identify and manage specific applications, such as allowing Facebook but blocking its chat function, or permitting a business-approved file-sharing app while blocking consumer-grade ones.
Identity Awareness allows the NGFW to link network traffic and security policies to a specific user or user group rather than just a physical IP address. This is critical in large corporate networks for auditing, logging, and enforcing role-based access.
The advanced features like DPI and IPS require significant processing power, so an NGFW can introduce latency if it is not properly sized for the network traffic volume. Vendors use specialized hardware or optimized software to minimize this performance impact.
Yes. Virtual NGFWs are deployed as software instances within public cloud providers (like AWS, Azure, GCP) to secure cloud workloads and provide the same level of advanced inspection and policy enforcement as hardware appliances. There are also Cloud-Based NGFW (FWaaS) models.
Threat Intelligence ensures the NGFW remains effective against new attacks. The firewall connects to global security databases for continuous, real-time updates on malicious IP addresses, infected domains, and new malware patterns, allowing it to block emerging threats immediately.
Businesses in the UAE and the wider GCC region must protect high-value data and meet strict regulatory standards. An NGFW provides the holistic security needed to combat sophisticated, targeted attacks, ensure compliance, and manage security across distributed networks, which is vital in fast-growing global markets.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts