.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

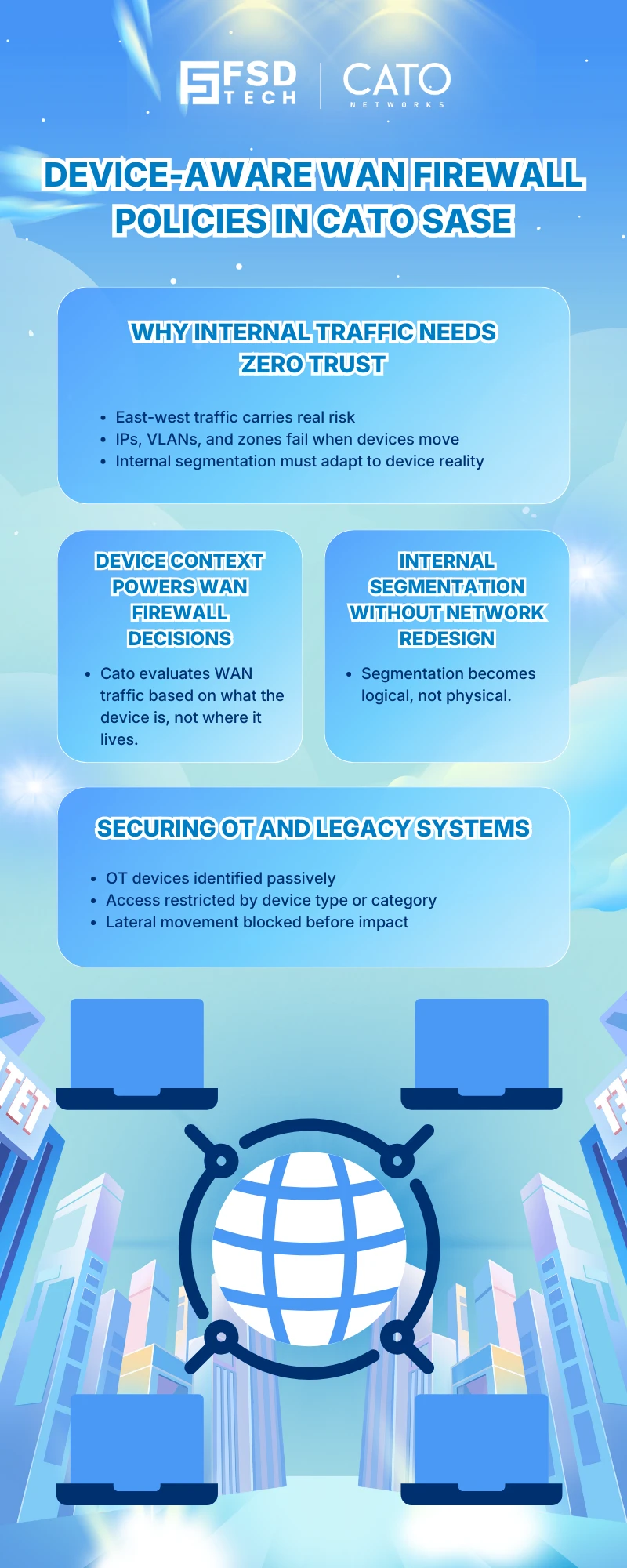
Modern enterprise risk no longer comes only from the internet edge. Lateral movement, unmanaged internal devices, and uncontrolled site-to-site access now represent some of the most serious security gaps inside corporate networks. Traditional WAN firewalls, built around IPs and static zones, struggle to enforce meaningful segmentation once traffic moves inside the network.
This is where device-aware WAN firewall policies in Cato Networks SASE fundamentally change how internal security is enforced. By incorporating device context directly into WAN firewall rules, Cato allows enterprises to apply Zero Trust principles inside the network—without introducing complexity or multiple control planes.
This blog explains how Cato’s WAN firewall uses device awareness to secure east-west traffic, protect OT and IT assets, and deliver scalable internal segmentation across sites.
In most enterprises, internal WAN traffic includes a mix of:
Traditional WAN firewalls evaluate this traffic using network-centric identifiers such as IP ranges, VLANs, or site objects. These controls break down when:
Cato’s WAN firewall addresses this by enforcing policies based on what the device is, not just where it sits on the network.
Cato applies device context to WAN firewall policies through its Device settings in the WAN firewall rule base.
The WAN firewall evaluates traffic using:
These conditions are evaluated before WAN traffic is allowed between sites, users, or resources.
This enables segmentation decisions such as:
All enforcement happens centrally in the Cato Cloud.
Device Attributes allow WAN firewall rules to match traffic based on classified device characteristics, including:
These attributes are populated by Cato’s Device Inventory engine, which passively analyzes WANbound and outbound traffic without requiring agents.
An enterprise can create WAN firewall rules such as:
Because enforcement is device-aware, segmentation remains intact even if:
OT environments are particularly difficult to secure because:
Cato’s WAN firewall enables OT protection using agentless device identification.
Using Device Attributes in WAN firewall rules, administrators can:
For example:
This aligns directly with Zero Trust segmentation principles for OT security.
Cato WAN firewall rules can combine device context with additional criteria to create precise internal policies.
This allows policies such as:
For devices that support the Cato Client, WAN firewall rules can also include Device Posture Profiles.
This enables internal access control based on:
A common enforcement model is:
This ensures that internal WAN access is granted only to devices that are both recognized and secure.
Device-aware WAN firewall policies deliver clear operational benefits:
Security teams can validate and investigate enforcement using:
This tight integration simplifies internal threat detection and response.
By embedding device context directly into the WAN firewall, Cato enables enterprises to:
Most importantly, this is achieved without deploying additional tools or maintaining parallel policy engines.
Protect IT and OT environments with agentless, device-aware controls → Schedule a free 30-minute Cato WAN Firewall strategy session.
The Cato WAN Firewall uses Device Attributes and Device Posture Profiles as rule conditions, allowing segmentation decisions based on device identity rather than IP addresses.
Yes. Cato SASE uses agentless Device Inventory detection to classify OT devices and enforce WAN firewall policies without requiring endpoint agents.
Cato WAN Firewall rules can use Category, Type, Model, Manufacturer, Operating System, and OS Version attributes sourced from Device Inventory.
Yes. For devices running the Cato Client, Device Posture Profiles can be applied in WAN firewall rules to enforce internal access based on endpoint compliance.
By enforcing device-aware rules, Cato SASE limits which devices can communicate across sites, reducing lateral movement even inside trusted networks.
Yes. All WAN firewall enforcement is centralized in the Cato Cloud, providing consistent policy application across all locations.
Cato WAN Firewall applies identity, device, posture, and context checks before allowing internal traffic, aligning internal access with Zero Trust principles.

Anas is an Expert in Network and Security Infrastructure, With over seven years of industry experience, holding certifications Including CCIE- Enterprise, PCNSE, Cato SASE Expert, and Atera Certified Master. Anas provides his valuable insights and expertise to readers.
Share it with friends!
share your thoughts