.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
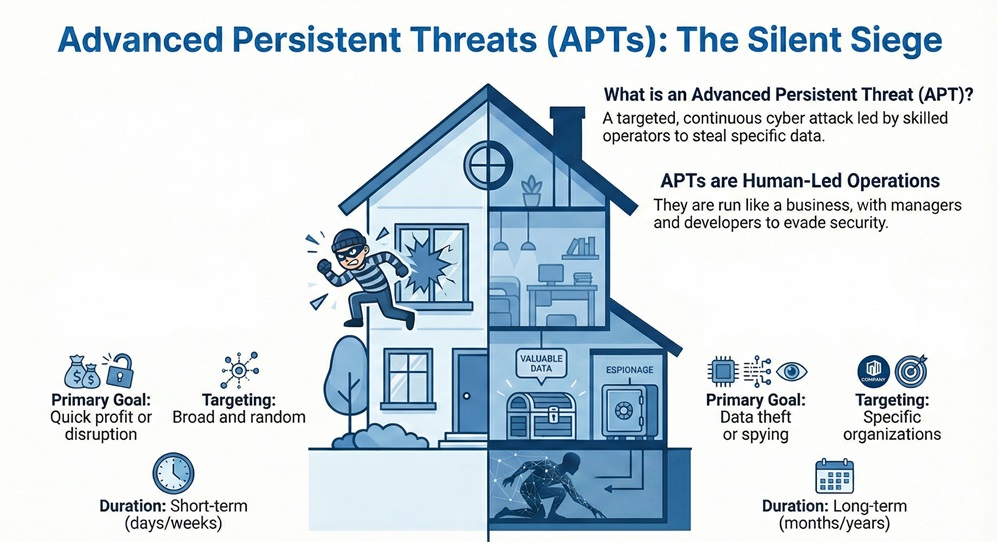
Have you ever thought about a thief who lives in your house for years without you knowing? This thief does not just grab your TV and run. Instead, they watch you every day. They learn where you keep your keys. They find out your bank codes. They wait for the perfect time to take your most valuable items. In the digital world, this is exactly how an Advanced Persistent Threat works.
You might think your current security is enough, but these attackers are different. They do not want a quick win. They want a long term stay. How do they get in? What are they really looking for? You will learn how these quiet attacks change everything you know about safety.
| Feature | Standard Malware | Advanced Persistent Threat |
|---|---|---|
| Primary Goal | Quick profit or disruption | Data theft or spying |
| Targeting | Broad and random | Specific organizations |
| Duration | Short (days or weeks) | Long (months or years) |
| Attack Method | Automated tools | Human-led and manual |
| Visibility | Often easy to find | Hard to detect |
| Complexity | Simple scripts | Custom coding and tools |
Advanced Persistent Threat describes a type of cyber attack that is targeted and continuous. These are not random hacks. Criminals or state actors lead these attacks with a specific goal in mind. They often want to steal trade secrets or government data.
It refers to the high level of skill the attackers have. They use many different methods to reach their goal. They do not give up if one door is closed. They look for another way in.
Advanced Persistent Threat means the attack stays in your system for a very long time. The "persistent" part is what makes it scary. The attackers do not want to be caught. They hide their tracks so they can keep stealing data for years.
APT groups have a lot of money and time. They act like a professional business. They have managers and developers. This allows them to stay ahead of basic security tools.
Advanced Persistent Threat definition starts with three main parts. First, it is "advanced" because it uses custom tools. Second, it is "persistent" because it stays active over time. Third, it is a "threat" because a human is driving the attack.
It means your data is at risk from experts. These experts study your staff. They look for weak spots in your software. They even look at your physical office security.
Advanced Persistent Threat describes a shift in how we think about risk. We cannot just build a wall and feel safe. We must assume someone is already inside. This mindset helps you find problems faster.
Advanced Persistent Threat involves a slow and steady approach. Most people think of hacking as a fast event. But an APT is more like a marathon. The attackers take small steps so they do not set off alarms.
Advanced Persistent Threat examples help us see the damage they cause. One of the most famous cases is Stuxnet. This was a worm that attacked industrial systems. It was built to stop a specific nuclear program. It showed that code could cause physical damage.
APT activity was also seen in the Titan Rain attacks. These attacks targeted United States defense systems. The attackers stole huge amounts of data over many years. It was one of the first times people realized how big this problem was.
These groups often target big tech companies too. Operation Aurora is a great example. It targeted companies like Google. The goal was to find source code and access the accounts of activists.
Advanced Persistent Threat attacks also hit the healthcare sector. The Anthem hack exposed the data of millions of people. This shows that APTs do not just want military secrets. They also want personal data they can sell or use for fraud.
What is an Advanced Persistent Threat Attack Lifecycle?
Advanced Persistent Threat attack starts with a stage called reconnaissance. The attackers gather information about your company. They look at social media to see who works for you. They scan your website for bugs.
APT attack then moves to the entry phase. This often happens through a phishing email. An employee clicks a link that looks safe. This link installs a small bit of code on their computer.
APT attack creates a "backdoor" next. This is a secret entrance that the attacker can use later. Even if you patch the first bug, the attacker still has their secret way in.
The attack involves moving through your network. This is called lateral movement. The attacker jumps from one computer to another. They look for the server that holds the most important data.
The attack ends with data exfiltration. The attacker slowly sends your data to their own servers. They do this in small chunks. This helps them avoid detection by your IT team.
Advanced Persistent Threat tools include custom made malware. Attackers do not use the same viruses you find online. They write their own code. This makes it impossible for standard antivirus programs to find them.
The tools often include remote access Trojans. These are called RATs. They let the attacker see your screen. They can also record your keystrokes to steal your passwords.
APT tools also use "living off the land" methods. This means they use the tools already on your computer. They use things like PowerShell or Command Prompt. Since these are normal programs, your security might not see them as a threat.
Advanced Persistent Threat tools help attackers hide their data transfers. They might hide your files inside normal web traffic. To your firewall, it looks like someone is just browsing the internet.
Advanced Persistent Threat is often misunderstood in tests and training. If you ask which statement describes it best, the answer is simple. It is a long-term, targeted attack by a skilled group.
It is not a simple virus that spreads to everyone. It is a surgical strike. It focuses on one victim at a time. It uses manual control rather than just automated scripts.
APT aims for low visibility. While a normal virus might lock your files for a ransom, an APT wants to stay quiet. If you know they are there, they have failed.
It involves a high level of coordination. This is another key way to describe it. Multiple people work together to breach your defenses. They have a clear chain of command and specific objectives.
APT detection requires looking for weird patterns. You should check for logins at odd hours. If an employee logs in from another country at 3 AM, that is a red flag.
Advanced Persistent Threat activity shows up in large data transfers. You should watch your outgoing traffic. If your server is sending huge files to an unknown IP address, you might have a problem.
It groups often leave small traces. These are called Indicators of Compromise. You can look for strange file names or new admin accounts. Checking your logs daily is a vital habit.
APT detection also uses machine learning. New software can learn what "normal" looks like for your office. When something changes, the software alerts you immediately. This is much faster than a human looking at data.
Advanced Persistent Threat protection starts with strong access control. You should use the principle of least privilege. This means employees only get the files they need for their job. If a hacker steals a low-level account, they cannot get to the sensitive stuff.
APT defense needs multi-factor authentication. You should never rely on just a password. Using a phone app or a security key makes it much harder for attackers to move through your network.
APT prevention includes segmenting your network. You should put your most valuable data in a separate "room" with its own locks. This stops an attacker from moving freely if they get inside.
Advanced Persistent Threat strategy must include regular training. You need to teach your team about phishing. Since most APTs start with a human error, your staff is your first line of defense.
Advanced Persistent Threat methods are used for economic gain. Some countries want to steal tech secrets. This lets them build products faster and cheaper. It is a form of digital spying that saves them billions of dollars.
These attacks are also used for political power. Hackers might steal emails to influence an election. Or they might shut down power grids to cause fear. It is a powerful tool for modern war.
APT campaigns can also target activists. Governments use these tools to track people who disagree with them. This is a very dark side of cyber security.
APT work is a long-term investment. While it costs a lot to run these groups, the reward is huge. One successful attack can give an organization an edge for a decade.
Advanced Persistent Threat defense is getting smarter. Machine learning helps identify new threats. It looks at how data flows and finds small errors. This is how we catch the "advanced" part of the threat.
APT actors try to trick these systems. They try to act like normal users. But math is hard to beat. Algorithms can see through the disguise by looking at millions of data points.
APT protection is now a cat and mouse game. As we get better at finding them, they get better at hiding. This is why you must always update your security software.
Advanced Persistent Threat monitoring should be constant. You cannot just check your systems once a month. You need real-time alerts to stop the "persistent" part of the attack before it is too late.
Advanced Persistent Threat is a major risk for everyone today. We live in a world where data is the most valuable thing. Criminals will go to great lengths to take it. You must stay alert and keep your systems strong.
It challenges us to be better. We cannot be lazy with our passwords or our software updates. Every small step you take makes it harder for a thief to live in your digital house.
APT awareness is the first step toward safety. By learning how these groups work, you can spot the signs early. Do not wait for a disaster to happen. Start protecting your future right now.
At our company, we value your peace of mind above all else. We know that security is not just a product. It is a promise to protect your hard work and your reputation. We focus on building tools that empower you to stay safe in an ever changing world. Our team is dedicated to your success and your safety every single day. Let us build a safer digital world together.
Stop Silent Attacks Contact FSD-Tech today

The main goal is usually to steal data or spy on an organization over a long period. Unlike other hackers, they do not want to be noticed.
Most APTs are run by state-sponsored groups or very organized criminal gangs. They have a lot of money and technical skill.
Yes, small businesses are often targets. They might be a "stepping stone" to reach a larger partner or client.
Look for strange network traffic, unusual login times, and new accounts you did not create. You can also use special security tools to scan for hidden backdoors.
No, antivirus is usually not enough. APTs use custom code that antivirus cannot see. You need a mix of tools, training, and monitoring.
An APT can stay in a system for many years. Some have been known to hide for over five years before being found.
Phishing is when an attacker sends a fake email. It looks real, but it has a bad link. This is the most common way APTs get into a network.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts