.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

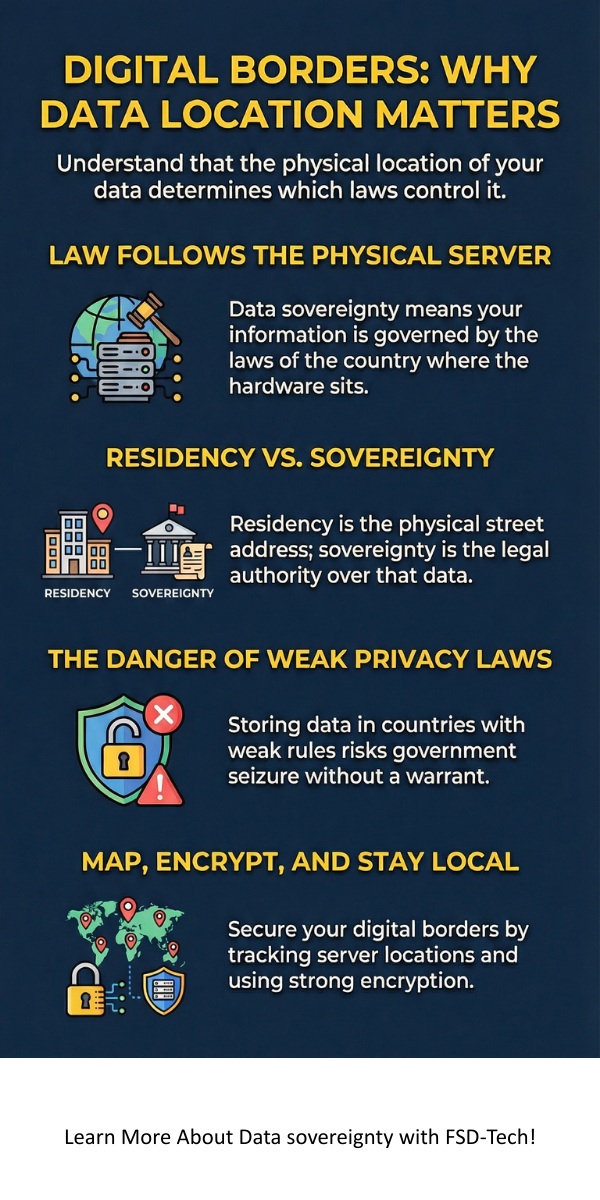
Data sovereignty is the idea that digital information is subject to the laws of the country where it is located. Have you ever wondered where your customer photos or bank details actually live? Most people think of "the cloud" as a floating, borderless space. To be honest, it’s actually a network of very real servers sitting on very real ground. Because that ground belongs to a specific nation, that nation's laws apply to your data.

In my experience, many business owners realize too late that their data has crossed a legal border. Think about a company in Singapore using a server in Virginia. Which country’s privacy rules apply? This isn't just a tech problem; it’s a legal puzzle. As we move more info online, knowing the rules of the road becomes vital.
This guide will help you grasp the basics of data sovereignty without the heavy jargon. We’ll look at why it matters for your privacy and how it keeps your business safe.
When we talk about data sovereignty, we are talking about control. If you lose control over where your data sits, you lose control over who can see it. Many countries now pass laws that require data to stay within their borders. This is called data residency.
Here is the thing: if your data moves to a country with weak privacy laws, your information is at risk. Governments might seize it without a warrant. Or, a foreign court might demand access to your trade secrets. We've all been there—agreeing to terms of service without reading the fine print. But for a business, that "fine print" could mean losing legal protection.
Secure Your Digital Borders Today
Roughly ten years ago, the internet felt like the Wild West. Today, it feels more like a map of fenced-in gardens. Why the change? Nations want to protect their citizens. They want to ensure that if a local company handles your data, they follow local rules like the GDPR in Europe or the CCPA in California.
Does this make things harder for tech companies? Yes. But it makes things safer for you. By keeping data local, countries can enforce security standards that keep hackers at bay.
You can understand data sovereignty as a digital passport. Just as you need a visa to enter a country, data must follow the rules of the land it enters. To be clear, this affects everything from your email to complex bank records.
Cloud Computing and the Location Trap
Most of us use cloud services like Google or Amazon. These companies have data centers all over the world. When you upload a file, it might end up in Ireland, India, or Iowa. If that file contains private health info, and it lands in a country with no privacy laws, you might be in trouble.
In my view, the biggest mistake is assuming "Cloud" means "Safe." You must ask your provider exactly where your servers are. If they can’t tell you, that’s a red flag.
The Role of International Data Spaces
Groups like the International Data Spaces Association (IDSA) are trying to set standards. They want to make sure you can share data without losing ownership. Imagine you are a car maker. You want to share engine data with a parts supplier. You need to know they won't sell that data to a rival. That is what sovereignty provides: the right to set terms on how your data is used.
Also Read: What is Geofencing Technology? All You Need to Know
People often mix these two up. Let's keep it simple. Data residency is about where the data sits physically. It’s the street address of the server. Data sovereignty is about the laws that govern that data because of its location.
It is a subtle shift, but a big one. You might satisfy residency by moving a server to London, but you only achieve sovereignty when you comply with the UK's legal demands.
Managing data sovereignty isn't always a walk in the park. For small businesses, the costs can add up. If you have customers in ten different countries, you might need to follow ten different sets of rules.
1. High Compliance Costs
Following the law costs money. You might need to hire a Data Protection Officer (DPO) or buy specialized software. For a startup, this can feel like a heavy weight. However, the cost of a data breach or a legal fine is much higher.
2. Conflicting Laws
What happens when Country A says "Keep this secret" and Country B says "Give us the records"? This happens more than you'd think. We call this a "conflict of laws." Large tech firms often find themselves caught in the middle of these digital tug-of-wars.
3. Tech Limitations
Not every cloud provider offers "local" storage. If you live in a small nation, there might not even be a high-quality data center near you. This forces you to send data abroad, which brings us back to the sovereignty risk.
Also Read: What is Network Access Control (NAC)? with Process
For some sectors, the rules are even stricter. Banks and defense agencies can't afford a single mistake.
Protecting Financial Records
Banks handle the most sensitive info we have. If a bank in Singapore stores its data in the US, the US government could technically subpoena those records. To prevent this, the Association of Banks in Singapore (ABS) has strict guidelines. They prefer local storage to ensure that only local regulators can peek at the books.
National Security and Defense
In defense, data sovereignty is a matter of life and death. Military data must stay under the control of the home nation. If a foreign power can access troop locations or weapon designs through a cloud server, the game is over. Defense agencies use "sovereign clouds" which are disconnected from the public internet to stay safe.
How do you protect your business? It starts with a plan. You don't need to be a tech genius to get this right.
As we look ahead, data sovereignty will only become more common. More nations are drafting "Data Acts" to reclaim control from big tech companies. We are moving toward a world where your data stays close to home.
This might seem like a hassle now, but it’s a win for human rights. It means your private life isn't subject to the whims of a foreign government you didn't vote for. It keeps power in the hands of the people who actually own the data: you.
At our core, we believe that your data is your most valuable asset. Protecting it isn't just a legal chore—it’s a commitment to your customers' safety. Navigating the world of data sovereignty can be tricky, but you don't have to do it alone. By focusing on local storage and smart encryption, we help you stay compliant and secure. Our mission is to put you back in the driver’s seat of your digital future. Ready to secure your borders?
The goal is to ensure that data is handled according to the laws of the country it resides in. This protects citizen privacy and national security.
Yes, the General Data Protection Regulation (GDPR) has strict rules about moving data outside the EU. It is one of the strongest examples of sovereignty in action today.
No. Even small businesses can face fines if they handle foreign customer data incorrectly. It’s best to be safe and use local storage options.
A sovereign cloud is a cloud service where the infrastructure and data stay within one country. It is managed by local staff to ensure foreign entities can't gain access.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts