.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

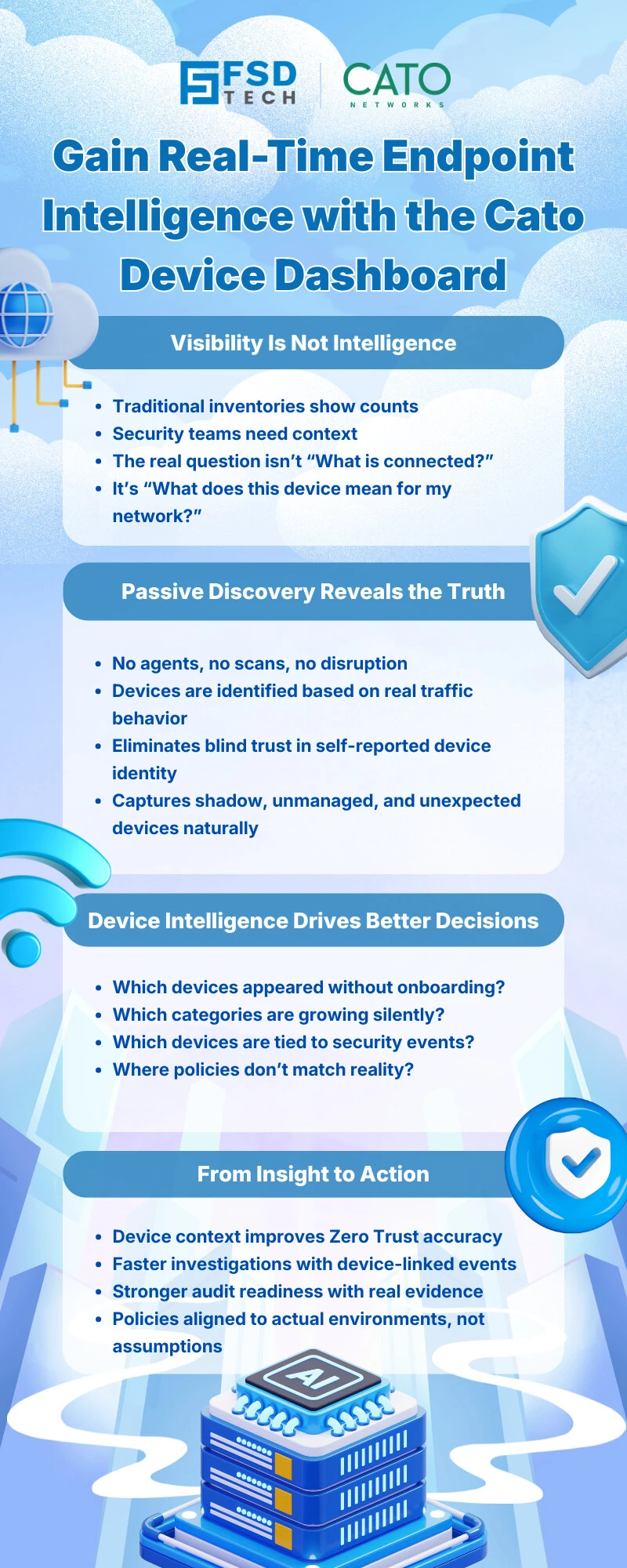
In modern enterprises, security and networking teams face a growing challenge: understanding what is actually connected to the network at any given moment. Laptops, mobile devices, servers, printers, IoT systems, and OT equipment all coexist—often without a single, unified view. Fragmented visibility makes it harder to detect risks, enforce Zero Trust policies, and respond quickly to incidents.
The Cato Device Dashboard addresses this problem directly. Built natively into the Cato Networks SASE platform, the Device Dashboard provides a centralized, real-time view of devices across your environment—turning raw device data into actionable security and operational insight.
This blog explains how the Cato Device Dashboard works, what it shows, and why it plays a critical role in modern Cato SASE–driven security operations.
The Cato Device Dashboard is a visual, analytics-driven interface inside the Cato Management Application (CMA) that summarizes device activity across the network. It is powered by Cato’s Device Inventory engine, which passively analyzes traffic to detect, identify, and classify devices without requiring agents or manual tagging.
Rather than forcing teams to dig through logs or spreadsheets, the dashboard presents at-a-glance intelligence about:
This unified view helps teams quickly understand what devices exist, where risk may be emerging, and which areas need attention.
The Device Dashboard does not operate in isolation. It is tightly integrated into the broader Cato SASE architecture, ensuring that visibility and enforcement go hand in hand.
Cato’s Device Inventory engine continuously analyzes WAN-bound and outbound traffic patterns to identify devices. This passive approach means:
The dashboard aggregates this intelligence and updates it dynamically as devices appear, disappear, or change behavior.
Beyond inventory counts, the Device Dashboard surfaces security-relevant insights, including:
With a single click, administrators can pivot from high-level charts to detailed device views or event logs, accelerating investigation and response.
This section provides a snapshot of:
It helps teams immediately spot unexpected growth or unusual device types on the network.
Charts and tables show devices by:
This visibility supports operational planning, vendor standardization, and security policy alignment within Cato SASE environments.
The dashboard highlights devices associated with:
This allows security teams to quickly identify which devices are driving risk, not just which policies are being triggered.
Instead of reacting only after incidents escalate, teams can proactively spot risky devices based on dashboard indicators. This shortens the time between detection and response.
Unmanaged IoT and OT devices often escape traditional security tools. The Cato Device Dashboard brings these assets into the same visibility plane as laptops and servers.
By consolidating device visibility into the CMA, the dashboard eliminates the need for multiple monitoring tools—supporting the simplicity promise of Cato SASE.
The Device Dashboard is not just a monitoring tool—it supports strategic outcomes:
In essence, the dashboard transforms device visibility from a reactive task into a continuous, proactive discipline.
Unexpected IoT Growth
An operations team notices a spike in IoT devices on the dashboard. A quick drill-down reveals newly added equipment that was never formally onboarded—prompting corrective action.
Investigating Firewall Events
A security admin sees repeated firewall blocks tied to a specific device model. From the dashboard, they navigate directly to event details and isolate the root cause.
Preparing for Policy Enforcement
Before applying device-based firewall rules, teams use the dashboard to validate device categories and manufacturers, ensuring policies align with reality.
Cato SASE is designed around convergence—networking, security, and visibility delivered from a single cloud-native platform. The Device Dashboard embodies this approach by:
It ensures that as environments scale, visibility does not become the weak link.
See every device. Reduce risk. Enforce Zero Trust → Reserve your 30-minute Cato SASE expert consultation now.
The Cato Device Dashboard is a centralized visibility interface in the Cato Management Application that shows device inventory, trends, and security events across the Cato SASE platform.
The Device Inventory page provides detailed per-device records, while the Cato Device Dashboard offers a summarized, visual overview for monitoring trends and risks at scale within Cato SASE.
Yes. The Cato Device Dashboard includes IT, IoT, and OT devices identified by the Device Inventory engine, supporting broad visibility in Cato SASE environments.
Yes. The dashboard highlights devices associated with firewall and IPS events, allowing administrators to pivot directly into detailed event analysis inside the Cato SASE platform.
The Device Dashboard is part of the Device Inventory capabilities, which require the appropriate Device Inventory license within the Cato SASE offering.
By providing continuous visibility into devices and their behavior, the Cato Device Dashboard enables informed, device-aware policy enforcement—a core principle of Zero Trust within Cato SASE.
While not a reporting tool by itself, the dashboard supports audit readiness by maintaining clear visibility into device types, activity, and security events across the Cato SASE environment.
The Cato Device Dashboard transforms device visibility from a static list into living intelligence. By combining passive discovery, real-time analytics, and security context, it empowers teams to operate confidently in complex environments.
For organizations adopting Cato SASE, the Device Dashboard is more than a feature - it’s a foundational capability that ensures visibility, security, and control evolve together.

Anas is an Expert in Network and Security Infrastructure, With over seven years of industry experience, holding certifications Including CCIE- Enterprise, PCNSE, Cato SASE Expert, and Atera Certified Master. Anas provides his valuable insights and expertise to readers.
Share it with friends!
share your thoughts