.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
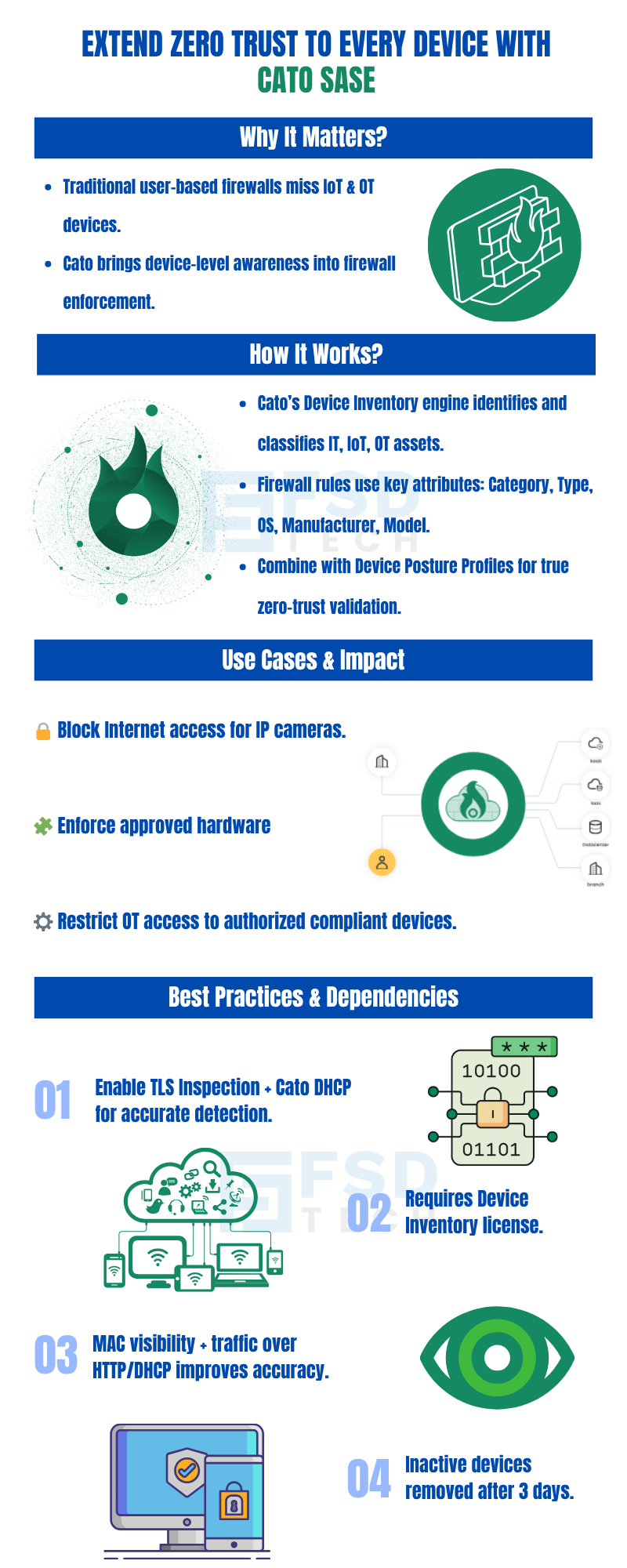
Modern businesses deal with a massive attack surface thanks to the rise of IoT, OT, and unmanaged gadgets. To be honest, relying only on user names or office locations for security just doesn't cut it anymore for zero-trust access. Cato SASE fixes this by letting you plug Device Inventory attributes right into your firewall rules.
This brings "device awareness" to your WAN and Internet policies, making sure every connection is checked not just by who is logging in, but exactly what tool they are using.
Cato’s Device Inventory engine passively analyzes network traffic using AI/ML to detect, classify, and profile IT, IoT, and OT devices. These device characteristics can then be enforced in firewall policies to achieve granular control.
Supported Device Attributes
Firewall rules can be built on the following device attributes:
To enable this feature, organizations must activate the Device Inventory license, which unlocks the Device Inventory page and attribute-based firewall enforcement.
Cato points out a few smart ways to use these tools:
Integrating Device Inventory into your firewall gives you some big wins:
While this is a powerhouse tool, there are a few "gotchas." The rules need a MAC address to work, and they rely on protocols like DHCP or HTTP for accuracy. To get the best results, we suggest using Cato as your DHCP server and turning on TLS Inspection. Also, remember that if a device is quiet for three days, it will drop off the list.
Also Read: Top Benefits of Implementing SASE in Your Enterprise
Cato SASE allows security teams to build multi-layered firewall rules by combining:
The rule logic is as follows:
This ensures administrators can enforce policies that verify not only the type of device but also its real-time security posture.
Integrating Device Attributes into firewall rules provides several advantages:
Also Read: Why is SASE Essential for Cloud-Era Network Security?
While powerful, administrators must account for some constraints:
If You Need Further Details On How To Implement Device Attribute-Based Firewall Policies Or Strengthen Zero-Trust Architecture In Your Organization, Please Feel Free To Schedule a No-Obligation Requirement-Gathering Virtual Meeting With Our Cato SASE Experts.
By putting device awareness into your firewall, Cato SASE makes your zero-trust network architecture (ZTNA) much tougher. Decisions aren't just about a username anymore; they include the device type and its safety status. We’re obsessed with helping our clients stay one step ahead of threats. If you want to see how to build these policies for your team, chat with our experts today for a quick strategy session.
Cato SASE allows admins to enforce granular policies on IoT/OT devices by using Device Attributes in firewall rules. For example, Internet firewall rules can block IP cameras from accessing the Internet, while WAN rules can restrict OT devices to authorized users.
Cato supports six key attributes: Category, Type, Manufacturer, Model, OS, and OS Version. These are automatically populated by the Device Inventory engine.
Yes. Administrators can create firewall rules that require both device identity (e.g., Manufacturer = Dell) AND compliance posture (e.g., anti-malware enabled). This layered approach enforces zero-trust verification.
A Device Inventory license is required to access this feature. Without it, the Device Attributes condition will not appear in firewall configuration.
Documented scenarios include:
Yes. Limitations include MAC address dependency, protocol restrictions, data merging/duplication, and device removal after inactivity.
Using Cato DHCP ensures MAC address visibility, while TLS inspection enables deeper traffic analysis for accurate device classification. Both are best practices recommended by Cato.
By combining device identity with posture and user conditions, Cato SASE enforces strict least-privilege policies. This ensures only trusted, compliant devices gain access to corporate resources, a cornerstone of Zero Trust.

Anas is an Expert in Network and Security Infrastructure, With over seven years of industry experience, holding certifications Including CCIE- Enterprise, PCNSE, Cato SASE Expert, and Atera Certified Master. Anas provides his valuable insights and expertise to readers.
Share it with friends!
share your thoughts