.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
.webp&w=3840&q=75)
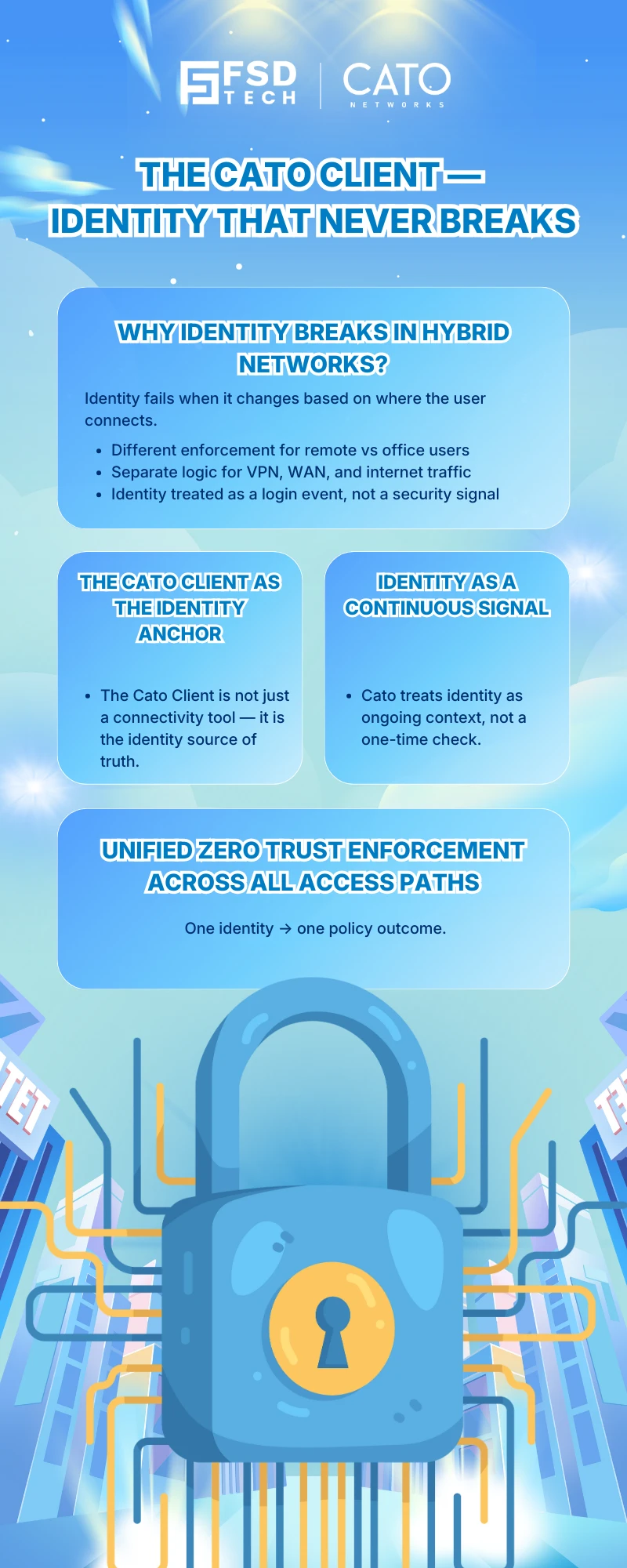
Modern enterprises no longer operate from a single network perimeter. Users work remotely, move between offices, and access applications hosted across data centers and cloud platforms. In this reality, traditional network-based trust models collapse—not because security tools fail, but because identity becomes fragmented.
Cato SASE addresses this challenge by treating identity as a continuous signal rather than a static attribute. At the center of this model is the Cato Client, which functions as the identity anchor for Zero Trust enforcement ensuring that access decisions remain consistent, verifiable, and enforceable regardless of where the user connects from.
This blog explains how the Cato Client enables identity-driven Zero Trust access across the entire Cato SASE platform and why this approach simplifies security operations while strengthening control.
In many environments, identity enforcement changes depending on where a user connects:
This inconsistency creates gaps where policies are duplicated, relaxed, or bypassed—directly undermining Zero Trust principles.
True Zero Trust requires that identity remains authoritative everywhere, not just during authentication.
The Cato Client is not simply a connectivity agent. Within Cato Networks, it serves a broader purpose:
it establishes and maintains a trusted identity signal that is continuously evaluated by the Cato SASE policy engine.
Once connected, the client allows Cato to apply identity-aware policies uniformly across:
This ensures the same security logic applies whether a user is remote or behind a site.
Traditional security models treat identity as a one-time validation step.
Cato’s approach is different.
With the Cato Client:
This allows Cato SASE to enforce Zero Trust decisions dynamically, not just at the point of access.
The Cato Client ensures that:
all reference the same user identity context, eliminating enforcement drift.
Security teams no longer need separate logic for:
Identity is enforced once and applied everywhere.
By anchoring identity to the client:
This reduces both risk and administrative overhead.
The Cato Client does not operate in isolation. It works alongside:
Identity becomes the control plane that ties all these signals together, allowing Cato SASE to apply policies that are:
This layered approach strengthens Zero Trust without adding operational burden.
By using the Cato Client as the identity anchor, organizations achieve:
Rather than bolting identity onto network security, Cato SASE embeds it directly into policy enforcement.
Zero Trust fails when identity enforcement is inconsistent.
Cato SASE succeeds because identity is built into the fabric of the platform, not layered on top.
The Cato Client makes Zero Trust practical by ensuring that:
This is what allows organizations to move from Zero Trust theory to Zero Trust execution.
Turn the Cato Client into your Zero Trust control plane → Schedule a free 30-minute Cato SASE identity session.
The Cato Client acts as an identity anchor by providing a continuous, trusted user identity signal to the Cato SASE platform. This allows Zero Trust policies to be enforced consistently across WAN, Internet, and application access without relying on network location.
Yes. Identity-based Zero Trust enforcement in Cato SASE relies on the Cato Client to associate user identity with traffic flows and apply identity-aware security policies.
Cato SASE applies the same identity context from the Cato Client regardless of whether the user is remote or behind a site, enabling uniform policy enforcement across all access paths.
Unlike traditional VPNs that authenticate identity only at login, the Cato Client maintains identity context throughout the session, allowing Cato SASE to enforce Zero Trust policies continuously.
Identity-driven Zero Trust enforcement requires the Cato Client. Without it, Cato SASE cannot reliably associate traffic with user identity for advanced policy decisions.
By centralizing identity enforcement, the Cato Client reduces duplicate policies, simplifies troubleshooting, and ensures predictable security outcomes across the entire Cato SASE environment.

Anas is an Expert in Network and Security Infrastructure, With over seven years of industry experience, holding certifications Including CCIE- Enterprise, PCNSE, Cato SASE Expert, and Atera Certified Master. Anas provides his valuable insights and expertise to readers.
Share it with friends!
share your thoughts