.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

Alert fatigue is real—and damaging. IT teams either drown in irrelevant notifications or miss critical signals entirely. Atera’s Alert Threshold Profiles offer a smarter way: define exactly what matters, when it should trigger an alert, and how it should behave once triggered.
This blog walks you through creating a smart threshold profile, customizing it, assigning it across environments, and validating that it works in real-world conditions—so you can turn down the noise and amplify the signals that matter most.
Get started with smarter alerts today — share your details and we’ll help you customize your first profile. Click Here
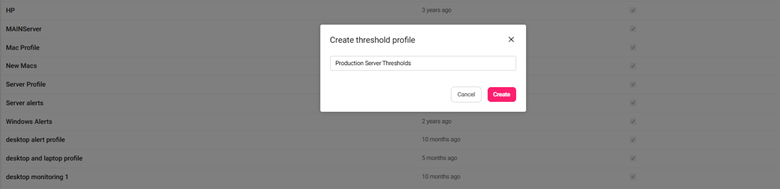
What it does: Lets you define a dedicated set of alert rules grouped under one profile.
Where it lives: Admin > Monitoring and automation > Thresholds
Why you’ll love it: It provides a clean, reusable way to build monitoring rules for different customer tiers, environments, or device roles.
Now the profile is listed and ready for customization.
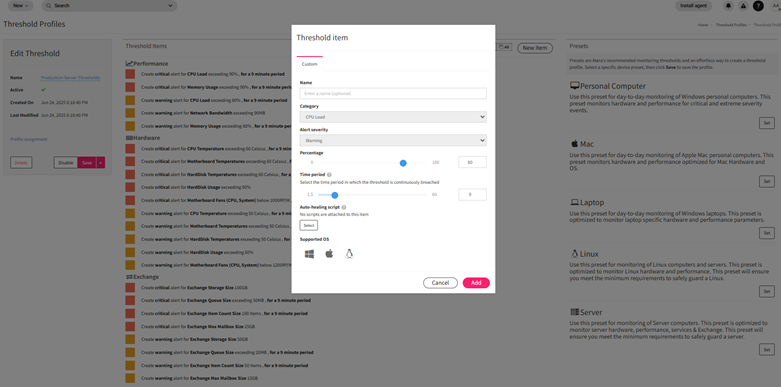
What it does: Allows granular control over what conditions generate alerts and at what severity.
Where it lives: Inside the Threshold Profile editor
Why you’ll love it: You can define exact CPU, RAM, disk usage, and process rules per environment or use case.
What it does: Ensures your threshold profile actively monitors the right endpoints.
Where it lives: Threshold Profiles > Profile Assignment button
Why you’ll love it: One-click assignment lets you scale the same rules across hundreds of endpoints.
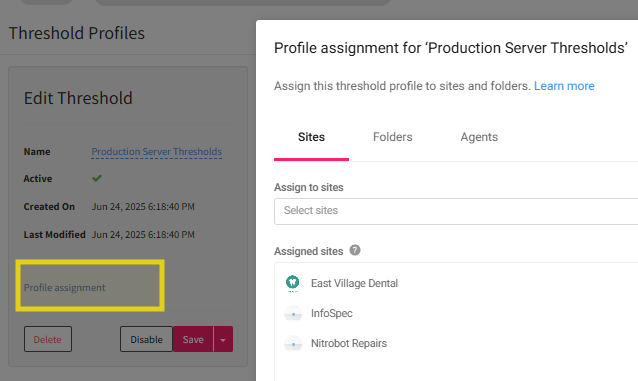
Assigning by customer is ideal for MSPs managing distinct SLA tiers.
What it does: Confirms that alerts trigger as expected and lead to the right actions.
Where it lives: Alerts > Agent Console > Device view
Why you’ll love it: You can catch false positives or missing triggers before rolling out company-wide.
You can also test whether automation rules or auto-ticketing triggers correctly from the alert.
What it does: Lets you track live alerts and make data-backed refinements to your threshold rules.
Where it lives: Alerts page
Why you’ll love it: You’ll eliminate noise, detect blind spots, and continuously tune alert sensitivity.
Refinement is ongoing—revisit your profiles monthly to adjust for seasonal or infrastructure changes.
Head to your Thresholds tab and create your first custom profile. Assign it to a small test group, validate alert behavior, then scale it with confidence. Smarter alerts mean faster resolution times, reduced fatigue, and tighter IT operations.
Book a quick session with our experts to validate your alert setup and avoid missed signals. Schedule Now

No. Only one threshold profile can be assigned per device at a time. If multiple profiles apply, the most recently assigned one will override any previous assignment.
Atera supports three severity levels:
To auto-create tickets from alerts:
Go to Admin > Contacts & Notifications.
Here you can:
Yes. Use the Snooze function to pause alerts temporarily, or configure scheduled maintenance windows from the Alerts page, which suppresses alerts for selected timeframes.
Yes. Go to Threshold Profiles > Assign, then:
Use the Alerts dashboard to:

Anas is an Expert in Network and Security Infrastructure, With over seven years of industry experience, holding certifications Including CCIE- Enterprise, PCNSE, Cato SASE Expert, and Atera Certified Master. Anas provides his valuable insights and expertise to readers.
Share it with friends!
.webp&w=3840&q=75)
🕓 March 25, 2026

🕓 March 22, 2026

🕓 March 20, 2026
share your thoughts