.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

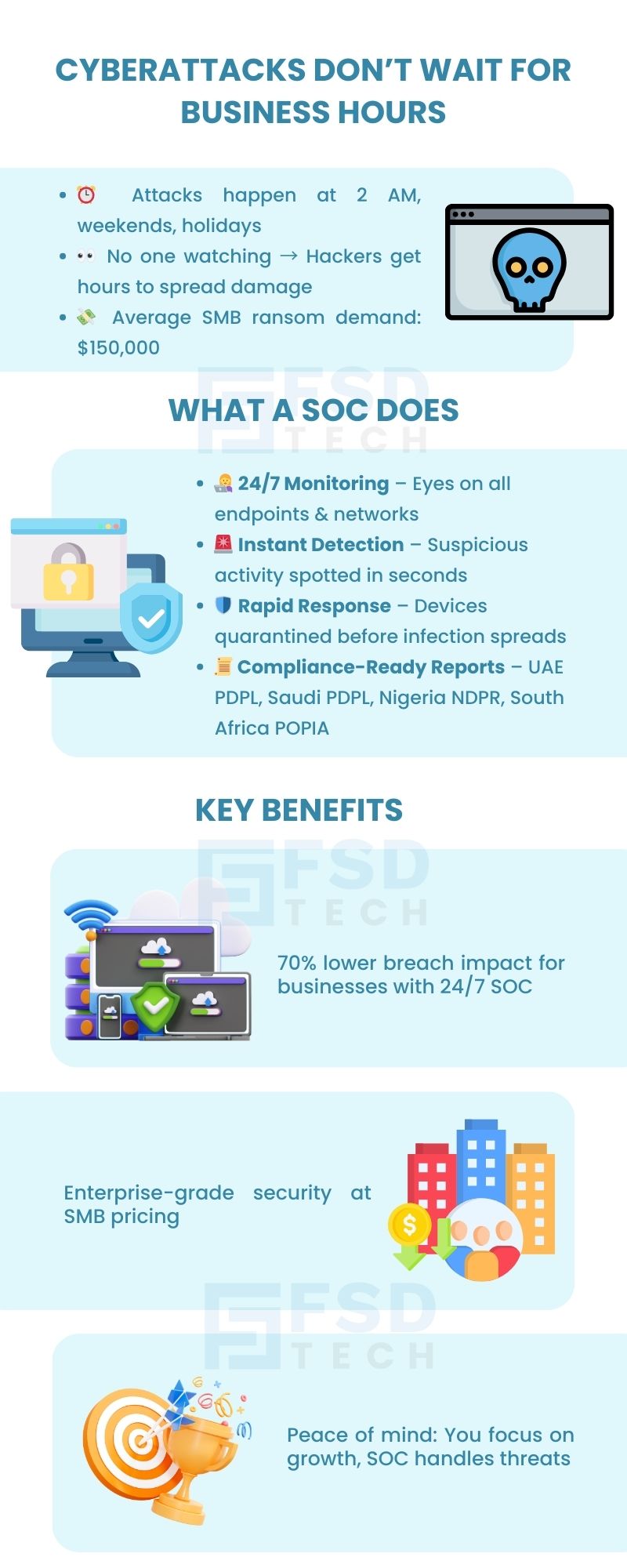
It was 2:37 AM in Lagos when the CEO of a mid-sized logistics company was woken up by a frantic call from his IT manager. The company’s ERP system — which handled customer orders, fleet schedules, and supplier invoices — had suddenly gone offline.
By the time the sleepy IT manager logged in remotely, he saw that multiple servers were encrypting files at lightning speed. It was a ransomware attack.
The attackers had chosen their time carefully: the middle of the night, when the two-member IT team was fast asleep. No one was watching. By morning, customer orders were delayed, suppliers couldn’t process shipments, and employees couldn’t even log in. The ransom demand: $150,000.
This isn’t a one-off story. Across GCC and Africa, cybercriminals deliberately target off-hours — evenings, weekends, or even religious holidays. Why?
Relying on “business hours security” is like locking your office at 6 PM but leaving the back door wide open all night.
This is where a Security Operations Center (SOC) becomes critical. A SOC ensures your business never has blind spots, because your cybersecurity runs 24/7 — even when your team doesn’t.
Worried your business is unprotected after hours? Request a Free Security Health Check today.
Think of a Security Operations Center as the “nerve center” of your cybersecurity.
If your business was a city, the SOC would be the command-and-control hub: the place where surveillance cameras feed in, alarms ring, and trained guards respond in real-time.
But instead of monitoring streets and buildings, the SOC:
In other words, a SOC is your 24/7 cybersecurity team, but without the cost of hiring one in-house.
Imagine having security cameras in every room of your office. Now imagine those cameras are watched live, every second of every day.
That’s what SOC monitoring does for your digital environment.
The SOC collects signals from:
This continuous stream of data is analyzed in real time by both machines and human experts.
Cyberattacks rarely announce themselves. Instead, they hide in plain sight. SOC analysts are trained to notice red flags such as:
These are signals that something is very wrong — and without a SOC, they’d often go unnoticed until it’s too late.
Speed is everything in cybersecurity. The difference between catching an attack in minutes versus hours can mean the difference between a minor hiccup and a business-crippling disaster.
With SOC and Zero Dwell Containment:
This isn’t just detection. It’s real-time containment and action.
Most businesses rely on alerts. The SOC goes further.
SOC analysts proactively hunt for threats that haven’t triggered alarms yet. They comb through logs, traffic patterns, and user behavior looking for stealthy intruders — much like detectives patrolling even when the alarms are silent.
This is critical because many modern cyberattacks (especially fileless malware or insider threats) don’t trigger standard alerts.
In GCC and Africa, compliance is becoming a board-level issue. Laws like:
require businesses to demonstrate continuous monitoring and strong data protection.
The SOC provides audit-ready reports that prove your business is compliant — saving your CFO and legal team from sleepless nights.
Cybercriminals deliberately time their attacks at 2 AM, during Eid holidays, or on weekends. Without SOC, those hours become your biggest weakness.
Most SMBs can’t afford to hire a 24/7 cybersecurity team. Even large enterprises struggle with staffing. SOC provides that round-the-clock coverage as a service, giving you the strength of a global enterprise team without the cost.
Every hour an attacker remains undetected increases recovery costs. Studies show that businesses with 24/7 SOC reduce breach impact by up to 70%.
Auditors and regulators now expect proof that your business is actively monitoring threats at all times. SOC gives you the evidence and confidence to pass compliance checks without stress.
Need to prove compliance? Download Your Free SOC Compliance Readiness Checklist.
On their own, tools are powerful. Together, they’re unstoppable.
Analogy:
Think of EDR as your burglar alarm, Zero Dwell as your automatic door locks, and SOC as the trained guard team that responds, investigates, and strengthens your defense for next time.
One evening, a retail chain with stores across Nairobi faced repeated login attempts from an IP address in Eastern Europe.
Without SOC: Those attempts may have gone unnoticed until the next day, giving attackers time to steal data.
With FSD-Tech’s SOC:
Outcome: No downtime, no breach, and the business avoided what could have been a $250,000 loss.
Partnering with FSD-Tech means more than just outsourcing.
In short: We don’t just monitor. We protect, respond, and manage.
Cybersecurity is no longer just about having tools. It’s about having the right people watching those tools 24/7.
With FSD-Tech’s SOC powered by Xcitium, you get:
While you focus on growing your business, our SOC ensures hackers never get the chance to slow you down.
Ready to see SOC in action? Book a Free Strategy Call with Our Experts. Schedule Now
SOC stands for Security Operations Center — a team of security experts who watch over your business systems 24/7, detect threats, and take action instantly.
Because cyberattacks can happen anytime — not just during office hours. SOC ensures someone is watching your systems day and night, ready to stop threats before they cause damage.
Antivirus and EDR are tools. SOC is people + process. SOC experts monitor those tools, investigate alerts, and take action immediately, ensuring nothing slips through the cracks.
Yes. SOC teams can detect ransomware behavior early, isolate the affected device, and prevent it from spreading — often within minutes.
No — SMBs and mid-market businesses benefit the most from SOC because they usually can’t afford a full in-house security team. SOC provides that expertise as a service.
MDR is a managed service focusing on detecting and responding to threats on endpoints. SOC is a broader security team monitoring your entire IT environment — endpoints, networks, cloud, and more.
Yes — SOC generates audit-ready security reports for UAE PDPL, Saudi PDPL, Nigeria NDPR, South Africa POPIA, and other regulations.
SOC analysts review every alert from your security tools, confirm if it’s a real threat, and take immediate action if needed — reducing false alarms and wasted time.
No — SOC monitoring works in the background without affecting performance. You won’t even notice it’s there, but it’s always protecting you.
Yes — SOC monitors all devices, whether in the office, at home, or on the road, ensuring full protection for today’s remote workforce.
FSD-Tech’s SOC can detect and contain threats within minutes, preventing widespread damage and costly downtime.
SOC is offered as a subscription service, making it affordable for SMBs. The cost is far less than recovering from a single cyberattack.
SOC works alongside your IT team, focusing on security monitoring and incident response while your team handles day-to-day tech support.
We combine Xcitium EDR + Zero Dwell Containment with regional cybersecurity expertise, 24/7 monitoring, and compliance support — tailored for GCC & African SMBs.

Anas is an Expert in Network and Security Infrastructure, With over seven years of industry experience, holding certifications Including CCIE- Enterprise, PCNSE, Cato SASE Expert, and Atera Certified Master. Anas provides his valuable insights and expertise to readers.
Share it with friends!
share your thoughts