.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

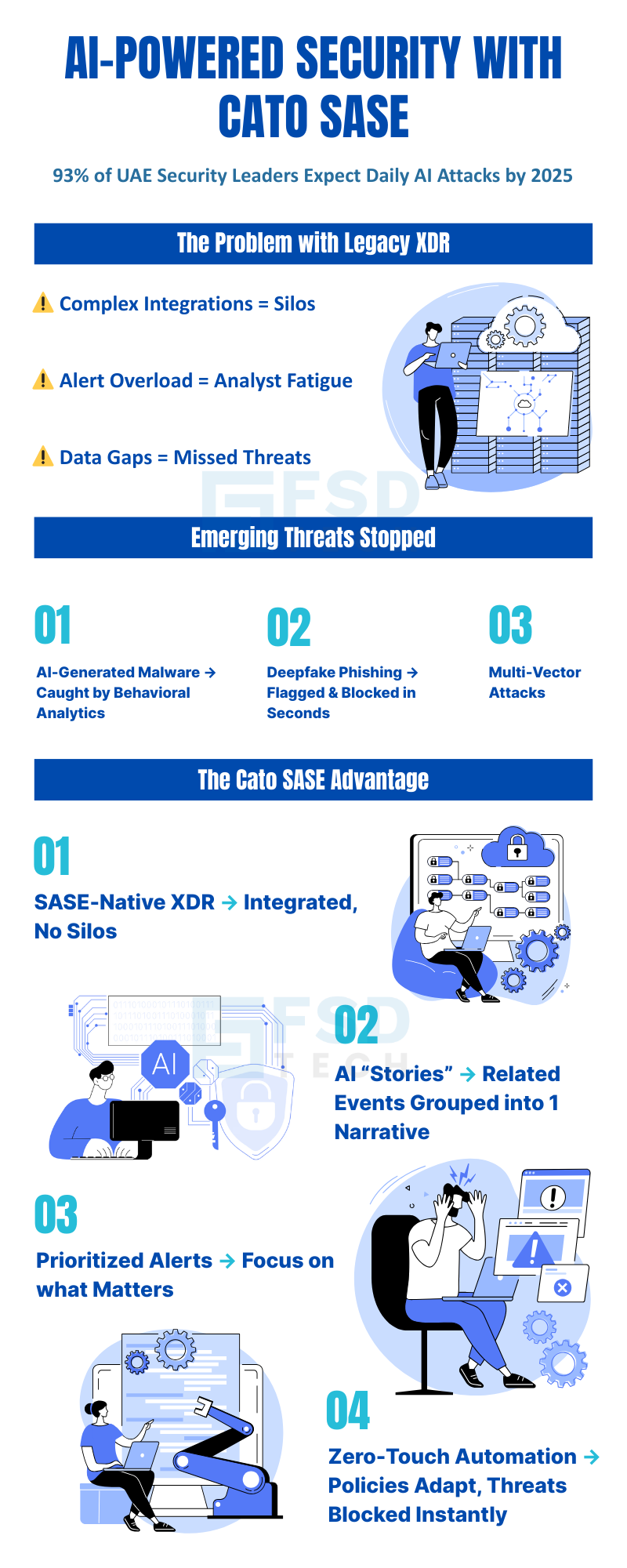
The AI-powered security scene in the UAE and GCC is moving faster than ever before. As we push into a digital-first world across finance and government, hackers are getting smarter. They now use generative AI to launch quick, sneaky attacks that old tools just can't catch. Did you know that 93% of regional security leaders expect to fight off AI threats every single day by 2025? It's a scary thought, right?
To stay safe, you can't rely on slow, manual steps anymore. Companies in Dubai and Abu Dhabi need automated tools that talk to each other. This is where Cato Networks and their SASE platform come in. By mixing AI with a unified network, they help you stop threats before they cause chaos.
To be honest, we've all felt the stress of a mounting "alert mountain." Why not let the machines handle the noise so your team can focus on growth?
Legacy XDR solutions were designed to aggregate and correlate security data from disparate sources—endpoint, network, cloud, and more. However, these tools often suffer from:
As attackers leverage AI to automate and scale their campaigns, legacy tools simply cannot keep pace.
Looking to simplify complex, siloed security operations? Share your details and our team will guide you with a tailored solution roadmap.
SASE, as defined by Gartner and pioneered by Cato Networks, converges networking and security into a single, cloud-native platform. This architectural shift enables:
With SASE as the backbone, enterprises can now leverage advanced AI/ML capabilities for automated, real-time threat detection and response.
Also Read: Top Strategies to Address Multi-Cloud Security Risks with Cato SASE
In early 2024, Cato Networks introduced Cato XDR—the world’s first SASE-based, extended detection and response solution. Unlike traditional XDRs that bolt onto existing infrastructure, Cato XDR is natively embedded within the Cato SASE Cloud platform, offering several key advantages:
This integrated approach is particularly valuable for UAE enterprises, where regulatory requirements and business agility demand both security and operational efficiency.
One of Cato XDR’s most innovative features is its AI/ML-powered incident correlation engine. Instead of bombarding SOC teams with isolated alerts, the platform:
Example: A UAE telecom operator experiences a spike in anomalous login attempts. Instead of generating hundreds of separate alerts, Cato XDR correlates these events into a single “Story,” flags it as high-risk, and triggers an automated containment workflow—saving hours of manual investigation.
Cato XDR’s automation capabilities extend beyond detection and correlation. The platform delivers:
Hypothetical: A Dubai-based bank is targeted by a deepfake voice phishing attack. Cato’s anomaly detection identifies unusual outbound traffic, correlates it with known deepfake patterns, and automatically blocks the connection—preventing data exfiltration in seconds.
Curious how AI-driven ‘Stories’ can cut through alert fatigue and speed up response? Let us know and we’ll send you a customized insight report for your organization.
Attackers are increasingly using generative AI to craft polymorphic malware that evades traditional signature-based defenses. Cato XDR counters this by:
Real-World: A GCC financial institution detects a previously unseen malware variant. Cato XDR’s AI correlates anomalous process creation, network connections, and privilege escalation, triggering an immediate response that isolates the affected endpoint.
Deepfake technology enables attackers to impersonate executives or trusted partners with alarming realism. Cato XDR’s AI-driven detection includes:
Scenario: Attackers launch a coordinated campaign involving phishing emails, credential stuffing, and lateral movement across a bank’s network.
This level of automation and intelligence is essential for organizations facing fast-moving, AI-powered threats.
FSD Tech’s expertise lies in mapping enterprise network telemetry—ensuring that all relevant data flows into Cato XDR for comprehensive visibility. This includes:
UAE and GCC organizations must comply with stringent data protection and cybersecurity regulations. FSD Tech ensures that:
Example: FSD Tech deploys Cato XDR for a Dubai financial institution, customizing incident response playbooks to meet UAE Central Bank guidelines and ensuring all data remains within approved jurisdictions.
A leading Dubai-based bank partnered with FSD Tech to modernize its security operations. Key outcomes included:
Also Read: Simplifying IT Operations with Cato SASE: Reducing Complexity and Enhancing Performance
Cato Networks’ leadership in the 2025 Gartner Magic Quadrant for SASE Platforms validates its innovation and effectiveness. The platform’s AI capabilities, unified architecture, and global reach make it the preferred choice for enterprises seeking to enhance security and simplify operations.
By adopting Cato SASE and XDR, UAE organizations achieve:
Ready to explore AI-powered security for your enterprise? Schedule a Free consultation with FSD Tech’s experts and see how it fits your environment.
SASE (Secure Access Service Edge) converges networking and security into a single cloud-native platform, delivering consistent protection and performance for distributed enterprises. For UAE organizations, SASE is critical to support rapid digital transformation, enforce uniform security policies across locations, and meet the demands of sectors like finance, telecom, and government.
Cato XDR is natively integrated into the Cato SASE Cloud, eliminating the need for complex integrations and data normalization. This unified approach provides high-fidelity, real-time telemetry and enables seamless, AI-driven threat detection and response—unlike legacy XDRs that rely on stitching together disparate tools.
Cato XDR identifies a wide range of threats, including AI-generated malware, deepfake phishing, insider threats, and advanced persistent threats. Its behavioral analytics and real-time AI/ML correlation allow it to detect both known and unknown attack vectors.
FSD Tech specializes in mapping enterprise network telemetry, customizing Cato’s AI-driven detection workflows, and operationalizing automated response in compliance with UAE and GCC regulations. Their regional expertise ensures smooth deployment and ongoing support for local enterprises.
Yes. Cato SASE’s compliance-ready architecture, combined with FSD Tech’s deep knowledge of UAE regulatory frameworks, makes it ideal for highly regulated sectors. The platform supports data sovereignty, privacy, and audit requirements.
The “Stories” feature uses AI/ML to correlate related security events into a single incident narrative, prioritizing high-risk alerts and reducing the volume of noise. SOC teams can focus on actionable threats, improving response times and reducing burnout.
Zero-touch automation refers to autonomous policy tuning, agentless enforcement, and automated threat hunting. For UAE-based organizations, this means less manual intervention, faster incident containment, and more efficient use of security resources.
Yes. FSD Tech configures Cato SASE and XDR to align with UAE regulatory requirements, including data residency and incident reporting. Automated workflows and dashboards simplify compliance audits and regulatory submissions.
Cato SASE and XDR can be deployed in a matter of days or weeks, thanks to their cloud-native architecture and FSD Tech’s local integration expertise. This rapid deployment is a significant advantage over legacy solutions that can take months to implement.
Cato XDR leverages behavioral analytics and real-time correlation to spot deviations from normal activity, even when malware signatures are unknown. This is critical for detecting polymorphic, AI-generated threats that evade legacy defenses.
FSD Tech ensures that all security data and incident response workflows adhere to UAE data sovereignty laws. They configure Cato SASE deployments so that sensitive data remains within approved jurisdictions, supporting compliance and audit readiness.
Cato SASE uses AI-driven behavioral analytics to detect anomalies in communication patterns, such as changes in voice or email signatures. Automated response mechanisms can block suspicious sessions or communications in real time, protecting against deepfake-based threats.
Organizations can expect reduced risk of breaches, faster incident response, improved operational efficiency, and full compliance with local regulations. Real-world deployments in the UAE have shown dramatic reductions in alert volume and incident response times.
Cato SASE provides secure, consistent access to applications and data for users anywhere—whether in the office, at home, or on the move. Its cloud-native delivery and unified security policies are ideal for supporting distributed workforces across the GCC.
Cato SASE combines market-leading AI-driven security with a unified, cloud-native architecture. FSD Tech’s regional expertise ensures deployments are tailored for UAE and GCC requirements, delivering rapid ROI, regulatory compliance, and peace of mind for security leaders.

Anas is an Expert in Network and Security Infrastructure, With over seven years of industry experience, holding certifications Including CCIE- Enterprise, PCNSE, Cato SASE Expert, and Atera Certified Master. Anas provides his valuable insights and expertise to readers.
Share it with friends!
share your thoughts