.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
Predictive maintenance logic acts like a crystal ball for modern machines, telling us exactly when a part might fail before it actually happens. Have you ever wondered why some factories run like clockwork while others constantly face broken belts or smoking motors? It usually comes down to how they handle repairs. Most people wait for things to break, but we’re going to look at a smarter way. In this guide, we’ll explore how data helps us stay ahead of the curve.
To understand predictive maintenance logic, we first need to look at the "why" behind it. In the past, we had two choices. You could fix things when they broke (reactive) or fix them on a schedule (preventive). Both have flaws. Fixing broken stuff is expensive and messy. Fixing things on a schedule often means throwing away perfectly good parts.
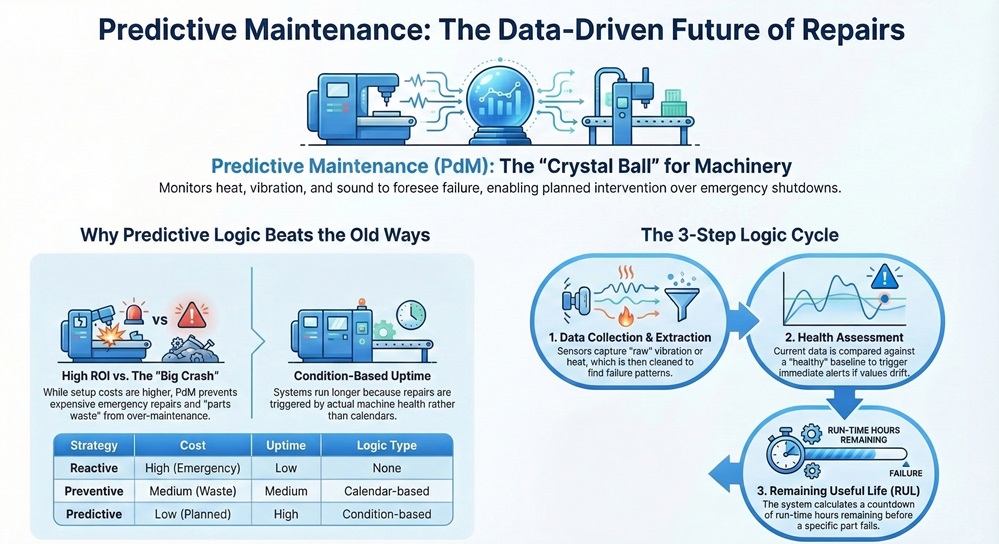
Here is the thing: PdM (Predictive Maintenance) uses sensors to listen to the machine. It looks at heat, vibration, and sound. By using specific logic, the system decides if the machine is healthy or needs a "doctor."
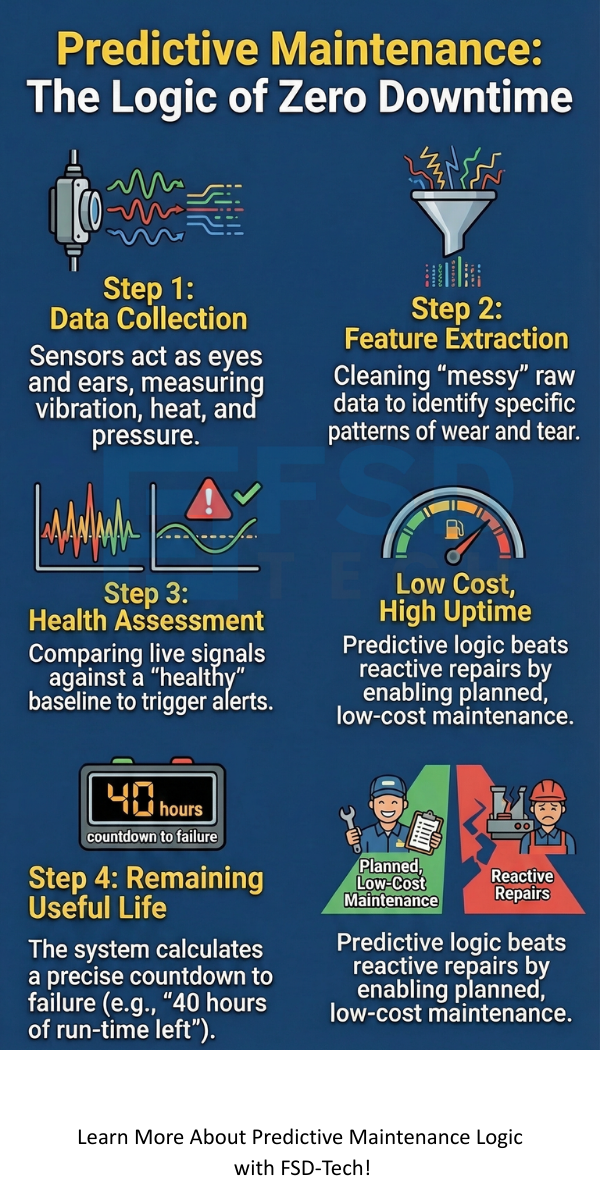
How does a computer actually "think" about a machine? It follows a very specific path. In my experience, most successful systems follow these four steps:
1. Data Collection
We start by gathering signals. Sensors act like the ears and eyes of the system. They measure:
2. Feature Extraction
Raw data is messy. If you look at a vibration graph, it looks like a bunch of squiggly lines. Predictive maintenance logic involves "cleaning" this data. We look for specific patterns, like a certain frequency that indicates a worn-out gear.
3. Health Assessment
Now, the system asks: "Is this normal?" We compare current data against a baseline of a healthy machine. If the data drifts too far, the logic triggers an alert.
4. Remaining Useful Life (RUL)
This is the holy grail. The system calculates a countdown. It tells you, "You have roughly 40 hours of run-time left before this bearing fails."
Also Read: How Remote Browser Isolation Protects Your Team from Web Threats?
To be honest, the old ways are draining your budget. When we use a systematic approach, we save money. Imagine a train system. If a signal fails, the whole line stops. Thousands of people are late. But if the predictive maintenance logic sees a battery voltage dropping slowly over a week, we can swap it during a planned break.
Does it cost more to set up? Yes. But the ROI (Return on Investment) is huge because you avoid the "big crash."
| Feature | Reactive | Preventive | Predictive |
|---|---|---|---|
| Cost | High (Emergency) | Medium (Parts waste) | Low (Planned) |
| Uptime | Low | Medium | High |
| Logic Type | None | Calendar-based | Condition-based |
A digital twin is a virtual copy of your machine. When we apply predictive maintenance logic to a digital twin, we can run "what-if" scenarios. We've all been there where we wonder if a machine can handle an extra shift. With a digital twin, we test it in the computer first.
This model uses math to simulate wear and tear. If the virtual machine breaks after 10 hours of high-speed use, we know not to push the real machine that hard. It’s like having a practice run for reality.
In the world of Indian Railways or large power plants, data loggers are the unsung heroes. These devices record every "event." For example, every time a relay clicks, the logger notes the time and the electrical current.
The predictive maintenance logic then scans these logs. It looks for "intermittent faults." These are tiny glitches that don't stop the machine but suggest a bigger problem is coming. Have you ever noticed your car lights flicker just once? That’s an intermittent fault. In a factory, ignoring that flicker leads to a total blackout.
Also Read: Database Fingerprinting: Secure Your Data Assets
Building these models isn't just for scientists. We can break it down into simple logic blocks.
Step A: Identify Failure Modes
What usually breaks? Is it the belt? The motor? Focus your sensors there first. Don't try to monitor every single bolt; it’s a waste of time and money.
Step B: Choose the Right Algorithm
We use different math for different problems.
It sounds perfect, right? But it's not always easy. One big issue is "Data Silos." This happens when the sensor data is in one computer and the repair logs are in another. If the two systems don't talk, the predictive maintenance logic fails.
Another hurdle is "False Positives." Sometimes a sensor gets dusty and sends an alarm. You stop the factory, check the machine, and find nothing is wrong. This loses trust. That’s why we need to refine our logic to be "smarter" over time.
Also Read: What is Software-Defined Perimeter? The Expert Guide to SDP and Zero Trust
In dynamic systems, like a jet engine or a high-speed train, things change fast. The temperature outside might be 10°C in the morning and 40°C at noon. The logic must account for this. A "hot" engine in the desert is normal, but a "hot" engine in the arctic is a disaster.
Modern predictive maintenance logic uses "Contextual Data." It looks at the weather and the workload before deciding if a temperature reading is dangerous. This is where the "AI" part really shines. It learns that "hot + desert = okay" and "hot + snow = stop."
If you are thinking about starting a PdM program, keep these points in mind:
We are moving toward "Prescriptive Maintenance." This is the next level. Not only does the system tell you it will break, but it also orders the part and schedules the technician. It might even slow the machine down automatically to make it last until the part arrives.
Isn't it amazing how far we've come from just hitting things with a wrench? We are now using the power of math and physics to keep the world moving.
At our core, we believe that technology should make life easier and businesses more efficient. Our focus is always on the client's success. By moving toward smarter maintenance, we help you protect your assets and your bottom line. We're here to guide you through every step of this digital shift. Let’s build a more reliable future together.
A: The initial setup for sensors and software is an investment. However, it usually pays for itself within a year by preventing one or two major breakdowns.
A: Yes! You can "retrofit" old machines with external sensors like vibration pads or thermal cameras to bring them into the digital age.
A: Not necessarily. Many modern software tools have built-in predictive maintenance logic that is user-friendly for engineers.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts