.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

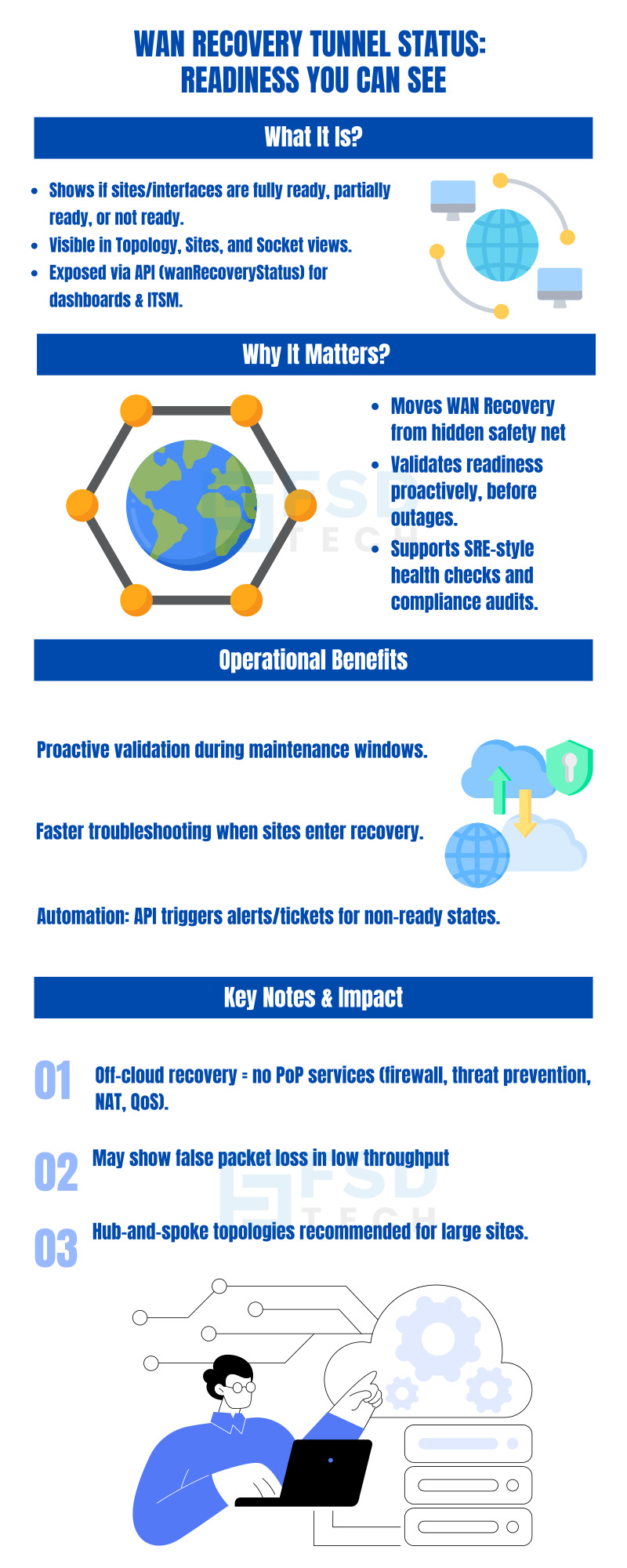
There is a fundamental problem with most enterprise resilience capabilities: you only discover whether they work during an actual outage. A failover mechanism that has silently misconfigured itself, a recovery tunnel that was never properly established, or a hub interface that lacks the readiness state to support its spoke sites — these gaps are invisible during normal operations and become critical during the exact moments when reliability matters most.
For enterprise network and security operations teams running Cato SASE deployments, WAN Recovery has always been the protection layer that maintains site-to-site connectivity when a PoP or middle-mile path becomes unavailable. It is a genuinely important capability — one that keeps branch offices communicating with each other even when their connection to the Cato Cloud is temporarily disrupted.
But until this update, WAN Recovery operated largely as a behind-the-scenes mechanism. There was no systematic, multi-view way to confirm that each site and each WAN interface was actually ready for off-cloud recovery before an event occurred. The readiness of the system was assumed rather than verified, and verifying it required navigating to individual site configurations rather than reviewing posture across the deployment.
Cato's introduction of WAN Recovery Tunnel Status changes that. Readiness becomes visible, measurable, auditable, and automatable — transforming WAN Recovery from a capability you hope is working into a capability you can prove is working.
Before examining the tunnel status visibility update in detail, understanding what WAN Recovery actually does provides the operational context that makes the readiness states meaningful.
WAN Recovery is the mechanism by which Cato Socket sites maintain site-to-site connectivity when a site loses access to the Cato Cloud — typically due to PoP unavailability or a disruption in the middle-mile path between the site and its nearest PoP. Under normal operating conditions, all inter-site traffic flows through the Cato Cloud, where it benefits from the full Cato security stack, QoS enforcement, NAT, and global routing optimization.
When WAN Recovery activates, Cato Sockets at affected sites establish direct DTLS tunnels over the public internet, bypassing the Cato Cloud and connecting directly to peer Sockets at other sites. This preserves traffic flows between sites during the recovery period, maintaining business continuity for applications that depend on site-to-site connectivity.
Several important behavioral characteristics define how WAN Recovery operates:
Default enablement on all Socket sites, with the exception of deployments in China where regulatory and connectivity constraints apply different configurations.
Full mesh topology by default, where each Socket site establishes direct recovery tunnels to all other Socket sites. This provides maximum connectivity options but generates significant tunnel count and probe overhead at scale.
Hub-and-spoke topology as the recommended configuration for large-scale deployments, where spoke sites establish recovery tunnels only to designated hub sites rather than to all peers. This reduces tunnel count and probe overhead substantially, making the recovery infrastructure manageable for enterprises with many sites.
Security service suspension during recovery, where traffic bypassing the Cato Cloud does not receive the PoP-based security services — Internet Firewall, Threat Prevention, NAT, DHCP relay, and QoS — that apply during normal operations. This is an important operational and security consideration that administrators must account for in their recovery planning.
The new Tunnel Status feature builds on this foundation by surfacing the readiness of each site and interface for WAN Recovery as a visible, queryable attribute rather than an assumed background state.
Cato now displays tunnel readiness states—fully ready, partially ready, or not ready—at both the site and WAN interface levels. This information is visible from multiple CMA views and exposed via API for integration with monitoring or ticketing systems.
This update transforms WAN Recovery from a behind-the-scenes capability into an operationally measurable and testable part of the SASE fabric.
WAN Recovery maintains site-to-site connectivity when a site loses access to the Cato Cloud. Sockets establish direct DTLS tunnels over the Internet, preserving traffic flows during rare events like PoP unavailability.
The new Tunnel Status feature builds on this foundation by giving admins a clear readiness signal for each site and interface.
Also Read: Global Access Optimization: The Secret to High-Speed Cloud Networking
Displays readiness for all sites in context, making it easy to spot issues at a glance.
Provides an inventory-style list where readiness can be sorted and filtered, useful for proactive audits.
Offers the most granular visibility, showing readiness at both the site level and individual WAN interfaces.
Historically, admins used the Off-Cloud Status indicator in site configuration to check if links were enabled for recovery. The new feature extends that visibility and standardizes it across multiple views.
Instead of waiting for a failure, admins can confirm readiness during normal operations. Gaps can be fixed ahead of maintenance windows or ISP escalations.
If a site enters recovery, operators already know which interfaces were marked ready. This narrows root cause analysis and avoids false alarms when sites appear “disconnected” in CMA during recovery.
The wanRecoveryStatus parameter allows integration with ITSM or NOC dashboards. Non-ready states can trigger tickets or alerts automatically, embedding recovery checks into broader operational workflows.
Also Read: Visibility and Control in a Cloud-First World: What Enterprises Need to Know
Filter the Sites view for not ready states, drill down into the interface, and resolve misconfigurations before planned downtime.
For large environments, hub-and-spoke topology reduces tunnel scale. Tunnel Status confirms that hub interfaces—the lifelines for spokes—are fully prepared.
Combine readiness with WAN Recovery events (Activated/Stopped) to create complete incident timelines, aligning visibility with recovery outcomes.
This feature elevates WAN Recovery from a hidden safety net to a governed, testable capability. Readiness becomes part of routine audits, change workflows, and compliance reporting. By exposing recovery posture in the CMA and API, Cato enables SRE-style health checks and operational assurance aligned with zero-trust and resiliency goals.
Ready to put WAN Recovery visibility into action?
Schedule a free consultation with our experts today
In the Cato SASE Management Application (CMA), WAN Recovery Tunnel Status is visible in Topology, Sites, and Site Configuration → Socket. The feature shows readiness at both the site and interface levels.
Cato SASE displays sites and interfaces as fully ready, partially ready, or not ready for WAN Recovery. These states help IT teams identify which Cato Socket links are prepared for off-cloud resiliency.
In Cato SASE, Off-Cloud Status indicates if links are enabled for recovery. The newer WAN Recovery Tunnel Status provides enhanced visibility across CMA views and adds granular readiness states for each Cato Socket interface.
Yes. Cato SASE exposes tunnel readiness through the wanRecoveryStatus field in the accountsnapshot API. This allows IT teams to integrate Cato WAN Recovery data into dashboards, ticketing systems, or compliance workflows.
When a site enters WAN Recovery, traffic bypasses the Cato Cloud PoP. As a result, the Cato SASE CMA may show the site as disconnected, even though the Cato Socket is passing traffic through off-cloud tunnels.
For large Cato SASE environments, Cato recommends a hub-and-spoke WAN Recovery topology to reduce tunnel counts and probe overhead. Tunnel Status can then confirm that hub Cato Sockets are fully ready to support spoke sites.
Yes. In Cato SASE, the CMA may misreport low-throughput links with ~4–5% packet loss. Also, certain hardware configurations on Cato Sockets may need special handling during upgrades. Always review the official Cato release notes before deployment.
No. During WAN Recovery, traffic bypasses the Cato Cloud, and PoP-based services—including Cato Internet Firewall, Threat Prevention, NAT, and QoS—do not apply until normal connectivity is restored.

Anas is an Expert in Network and Security Infrastructure, With over seven years of industry experience, holding certifications Including CCIE- Enterprise, PCNSE, Cato SASE Expert, and Atera Certified Master. Anas provides his valuable insights and expertise to readers.
Share it with friends!
share your thoughts