.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

The shift to hybrid work and cloud-first application delivery has permanently dissolved the traditional network perimeter. Legacy firewall-and-VPN architectures were designed for a world where users sat inside a building and applications lived in a data center. Neither assumption holds anymore, and the security gaps created by that mismatch are well-documented in breach statistics and audit findings across every industry.
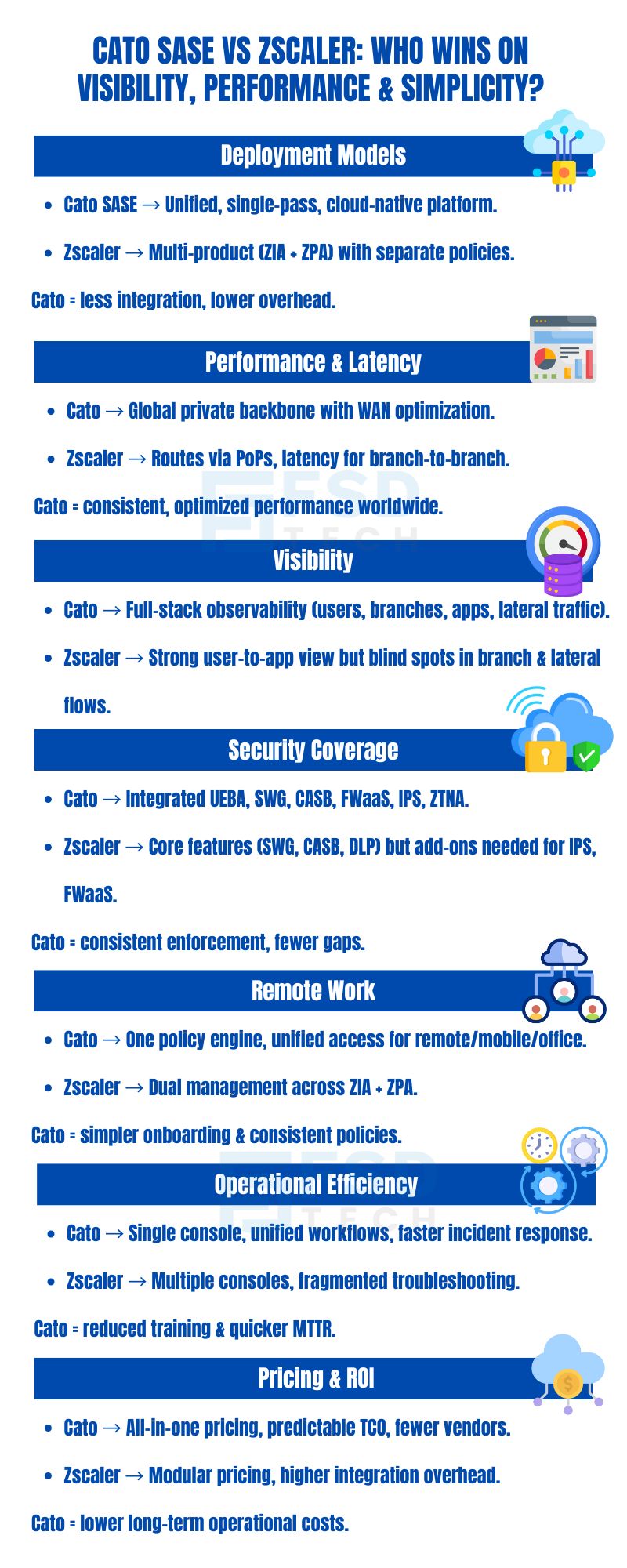
Two platforms consistently lead the enterprise conversation about what replaces that legacy model: Cato Networks SASE and Zscaler Zero Trust Exchange. Both are cloud-delivered. Both claim to provide secure, seamless access for users everywhere. Both have significant enterprise customer bases and credible analyst recognition.
But beneath the surface-level similarities, the architectural philosophies, operational models, and real-world deployment outcomes of these two platforms diverge in ways that have profound implications for CISOs, security architects, and IT leaders making long-term infrastructure decisions.
This comparison goes beyond feature checklists. It examines how each platform actually works — how traffic flows, how policy is managed, how incidents are investigated, and what the true total cost of ownership looks like over a three-to-five year horizon. The goal is to give enterprise decision-makers the factual foundation they need to make a confident, future-proof choice.
Cato SASE is Architected from the Ground-up as a Cloud-Native, Converged platform with Networking (SD-WAN, Routing, WAN optimization) and Security (SWG, FWaaS, CASB, ZTNA, DLP, IPS) are integrated into a single, global service. All policy enforcement, inspection, and routing occur in a single pass, reducing latency and eliminating the operational burden of stitching together point solutions from multiple vendors. As such the salient features include
Zscaler, by contrast, requires organizations to deploy and manage separate products :
While both are cloud-delivered, they operate independently. Customers must coordinate policies, integrations, and troubleshooting across both, increasing the risk of misconfiguration and slowing incident response.
When doing a SASE comparison with Zscaler, Cato consistently highlights the simplicity of Cato’s unified model versus the complexity of Zscaler’s multi-product stack.
| Feature | Cato SASE (Converged) | Zscaler (Multi-Product) |
|---|---|---|
| Architecture | Single-pass, unified | Separate ZIA + ZPA |
| Policy Engine | Centralized | Distributed |
| Integration Required | Minimal | High |
| Operational Overhead | Low | Moderate to High |
Also Read: Reducing IoT Attack Surface with Cato Internet Firewall Policies
Cato operates a global private backbone —a network of interconnected Points of Presence (PoPs) optimized for security and performance. All traffic, whether destined for the internet, cloud, or another branch, is routed over this backbone, benefiting from built-in WAN optimization and traffic engineering.
Zscaler routes user traffic through its global network of PoPs, which act as security inspection points. While effective for user-to-cloud scenarios, this model can introduce additional hops and unpredictable latency, especially for branch-to-branch or east-west traffic.
When we compare SASE platforms on performance, Cato's backbone consistently delivers lower, more predictable latency for global and east-west traffic.
| Scenario | Cato SASE | Zscaler |
|---|---|---|
| Branch-to-Branch | Private backbone, optimized | Routed via PoPs |
| Cloud App Access | Direct, optimized path | Routed via nearest PoP |
| WAN Optimization | Built-in | Not native |
| Latency Control | High | Variable |
Also Read: Cato IoT/OT Device Discovery: Securing What You Can’t Install Agents On
Cato provides full-stack observability across both network and security layers. IT teams can monitor user, branch, and application traffic in real time, correlate events, and rapidly diagnose issues.
Zscaler delivers strong visibility into user-to-app flows , particularly for internet and SaaS access. However, its visibility is limited when it comes to lateral movement, branch-to-branch traffic, or full network observability.
Best SASE solution 2024 evaluations increasingly prioritize platforms offering full-stack observability—an area where Cato excels.
Cato natively integrates a comprehensive set of security services into its platform, including:
All are managed from a single policy engine, ensuring consistent enforcement and eliminating gaps between security layers.
Zscaler offers robust security capabilities, but often relies on bolt-on modules or third-party integrations for full coverage.
Integrated security stack is a key differentiator for Cato, reducing complexity and the risk of misconfiguration.
| Security Feature | Cato SASE (Native) | Zscaler (Bolt-On/Native) |
|---|---|---|
| UEBA | Native | Add-on |
| DLP | Native | Native |
| SWG | Native | Native |
| FWaaS | Native | Add-on |
| IPS | Native | Add-on |
| CASB | Native | Native |
Cato enables consistent security and access policies for all users—remote, mobile, or on-prem—without the need for legacy VPNs or complex ZTNA configurations.
Zscaler’s ZTNA (ZPA) is effective for secure app access, but must be coordinated with ZIA for full internet and SaaS coverage.
ZTNA vs VPN is a common debate, but Cato’s approach eliminates the need for both, simplifying policy enforcement for hybrid workforces.
Cato’s unified platform means fewer components to deploy, manage, and troubleshoot .
Zscaler’s multi-product model can complicate operations.
Unified SASE platform vs multi-vendor stack is a critical consideration for organizations seeking operational agility and efficiency.
| Task | Cato SASE | Zscaler |
|---|---|---|
| Policy Management | Single console | Multiple consoles |
| Incident Response | Unified workflow | Fragmented |
| Logging & Forensics | Centralized | Distributed |
| Troubleshooting | Simplified | Complex |
Cato is often seen as cost-effective over the long term , especially for global organizations.
Zscaler may appear less expensive upfront, but costs can escalate as additional features and integrations are required.
| Aspect | Cato SASE | Zscaler |
|---|---|---|
| Pricing Model | All-in-one | Modular, add-on |
| Integration Costs | Minimal | High |
| Support Model | Unified | Multiple |
| TCO Predictability | High | Variable |
A global consulting firm with 2,000 employees leverages Cato to enforce consistent security policies, regardless of whether users are at home, in the office, or traveling. With Zscaler, IT must coordinate ZIA and ZPA policies, increasing the risk of misconfiguration and operational overhead.
A retail chain with 300 locations uses Cato’s private backbone for direct, optimized branch-to-branch communication. Zscaler routes branch traffic through PoPs, which can add latency and complicate troubleshooting.
A SaaS provider needs to monitor and control lateral movement between cloud applications. Cato’s full-stack observability detects and blocks suspicious activity across the entire network, while Zscaler’s visibility is limited to user-to-app flows, potentially missing critical threats.
| Feature/Capability | Cato SASE | Zscaler |
|---|---|---|
| Deployment Model | Unified, single-pass | Multi-product (ZIA+ZPA) |
| Private Backbone | Yes | No |
| WAN Optimization | Yes | No |
| Full-Stack Visibility | Yes | Partial |
| Integrated Security | Yes | Partial |
| Policy Engine | Centralized | Distributed |
| Remote Access | Native, unified | ZTNA (ZPA) + ZIA |
| Operational Overhead | Low | Moderate to High |
| Pricing Model | All-in-one | Modular, add-on |
| Architecture Aspect | Cato SASE | Zscaler |
|---|---|---|
| Core Design | Cloud-native, converged | Cloud-delivered, modular |
| Inspection Model | Single-pass | Multi-pass |
| Policy Consistency | Global, unified | Product-specific |
| Backbone | Private, optimized | Public PoPs |
| Security Stack | Fully integrated | Bolt-on/add-on |
| Cost Factor | Cato SASE | Zscaler |
|---|---|---|
| Licensing | Unified, per-user/site | Per-product/module |
| Integration | Minimal | Required |
| Support | Single vendor | Multiple vendors |
| Training | One platform | Multiple platforms |
| TCO Predictability | High | Variable |
The honest answer is that both platforms have appropriate use cases, and the right choice depends on your organization's specific architecture, operational maturity, and strategic priorities.
Cato Networks SASE is the stronger choice for organizations that prioritize operational simplicity alongside security depth — particularly those managing distributed branch networks where WAN performance matters, those seeking full-stack visibility for sophisticated threat detection, those with hybrid workforces that need consistent policy enforcement regardless of location, and those pursuing a single-vendor SASE strategy that reduces integration complexity and TCO over time.
Zscaler Zero Trust Exchange remains a credible choice for organizations with a strong existing focus on user-to-internet and user-to-application security scenarios, mature operational teams accustomed to managing multi-product environments, and use cases where ZIA's internet security capabilities are the primary requirement and branch networking optimization is not a priority.
For enterprises evaluating both platforms, the decision criteria that matter most beyond feature parity are: how much operational overhead your team can sustainably manage, whether branch-to-branch and east-west traffic performance is a real requirement in your environment, whether unified full-stack visibility is essential to your security operations model, and what your realistic three-to-five year TCO looks like when integration and operational costs are included alongside licensing.
When those factors are weighed honestly, Cato's converged architecture consistently presents a compelling case for organizations that need both networking performance and security depth without the operational complexity of managing a multi-product stack.
For organizations seeking a future-ready secure access platform that delivers on visibility, performance, and simplicity, Cato SASE stands out. Its unified, cloud-native architecture reduces operational complexity, accelerates incident response, and ensures consistent security everywhere. Zscaler remains a strong contender—particularly for organizations with focused user-to-app requirements—but its multi-product approach introduces complexity that can hinder agility and increase costs over time.
When evaluating Cato SASE vs Zscaler , security and network leaders should look beyond feature checklists to the operational realities of deployment, management, and scale. In that context, Cato’s converged platform offers a compelling path forward for enterprises prioritizing agility, visibility, and long-term ROI.
Book a no-pressure session with a SASE architect. We’ll review your sites, remote users, and critical apps and give you a concrete migration path.
Yes, Cato’s converged platform integrates SD-WAN, FWaaS, SWG, CASB, ZTNA, and more. This reduces the need for multiple vendors, simplifies management, and delivers unified policy enforcement across the entire network.
Cato’s global private backbone optimizes traffic end-to-end, minimizing latency and packet loss—especially for inter-branch and cloud traffic. Zscaler’s PoP-based model may introduce more hops and variable latency, particularly for east-west or branch-to-branch communication.
Cato offers full-stack visibility across users, sites, and applications, enabling holistic monitoring and rapid troubleshooting. Zscaler primarily focuses on user-to-app connections, which may miss lateral movement or branch-level issues.
Zscaler’s ZPA is effective for app access but requires integration with ZIA and additional configuration for full coverage. Cato’s unified platform delivers remote access and security with a single policy engine, streamlining deployment and management.
While Cato may have higher initial costs, its unified architecture reduces long-term operational expenses and integration overhead, delivering better ROI for global organizations. Zscaler’s modular pricing can become costly as additional features and integrations are required.
Yes, Cato SASE enforces consistent security and access policies for all users—remote, mobile, or on-prem—without the need for legacy VPNs or separate ZTNA products. This simplifies policy management and ensures a uniform security posture.
Cato provides a single console for monitoring, policy changes, and forensics, streamlining incident response and troubleshooting. Zscaler’s multi-product model can require navigating multiple dashboards and coordinating across teams, increasing time to resolution.
Cato requires minimal integration, as networking and security are natively converged. Zscaler often requires integration between ZIA, ZPA, and third-party tools to achieve full coverage, increasing operational complexity.
Yes, Cato’s full-stack observability and integrated security stack enable consistent policy enforcement and threat detection across all cloud applications, users, and locations.
Cato’s cloud-native, single-pass architecture enables rapid scaling and policy propagation across the global environment. Zscaler’s multi-product stack can slow down scaling efforts due to integration and configuration overhead.

Anas is an Expert in Network and Security Infrastructure, With over seven years of industry experience, holding certifications Including CCIE- Enterprise, PCNSE, Cato SASE Expert, and Atera Certified Master. Anas provides his valuable insights and expertise to readers.
Share it with friends!
share your thoughts