.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
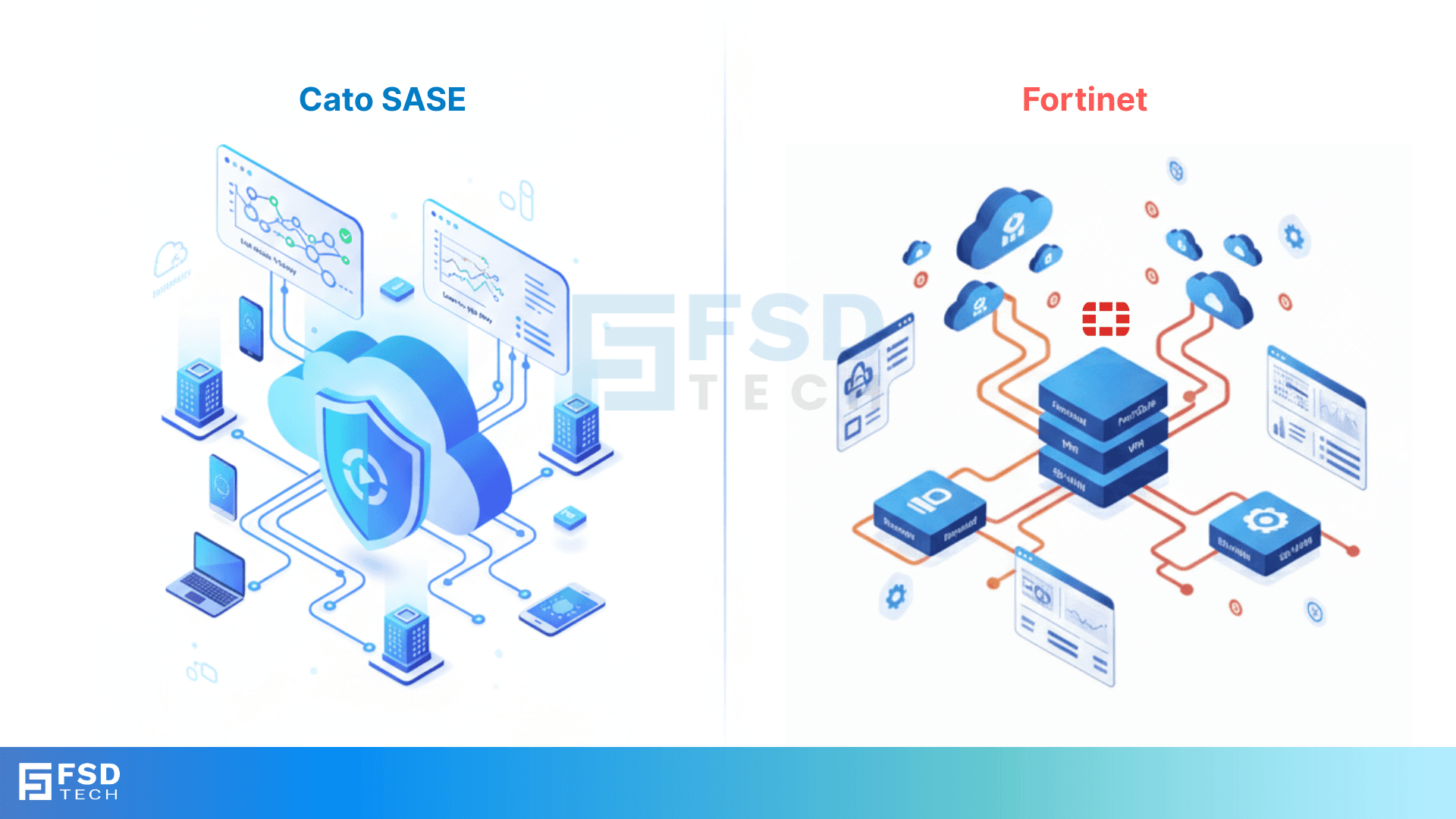
Every enterprise IT leader evaluating SASE in 2025 faces the same core question: do you want a platform that was built for convergence, or one that was assembled toward it?
The answer determines more than your vendor contract. It determines how fast you can onboard new sites, how consistently you can enforce security policy across a distributed workforce, how much operational overhead your team carries, and how quickly you can respond when the threat landscape shifts.
Cato Networks and Fortinet are both recognized in the 2025 Gartner Magic Quadrant for SASE. Both offer SD-WAN, ZTNA, SWG, CASB, and FWaaS. But their architectural philosophies are fundamentally different — and those differences produce dramatically different operational outcomes at scale.
This guide examines every major dimension of the Cato SASE vs Fortinet SASE decision: architecture, deployment complexity, security integration, performance, hybrid work support, customer experience, and total cost of ownership. It is written for CISOs, security architects, and IT leaders who need a technically honest, vendor-agnostic assessment to inform a high-stakes platform decision.
Before comparing vendors, it's worth anchoring the evaluation criteria. Gartner defines SASE as the convergence of WAN and network security services — including SWG, CASB, ZTNA, FWaaS, and DLP — into a single, cloud-delivered platform. The operative word is convergence, not collection.
A true SASE platform should:
These criteria are the lens through which the Cato vs. Fortinet comparison becomes most useful.
| Feature/Capability | Cato SASE Cloud Platform | Fortinet SASE (FortiGate/FortiOS) |
|---|---|---|
| Architecture | Cloud-native, unified, single-pass | Modular, appliance-centric, multi-product |
| Deployment | Fully cloud-delivered, minimal hardware | Requires appliances, multiple tools |
| Security Integration | Native, integrated stack | Stitched across modules |
| Policy Consistency | Centralized, global | Varies by module/location |
| Performance Backbone | Private global backbone | Edge routing/ISP dependent |
| Hybrid Work Support | Seamless, consistent | Requires integration/configuration |
| Customer Experience | Above average | Below average |
| Pricing Transparency | Bandwidth-based, less transparent | Modular, can be complex |
Cato Networks was designed as a cloud-native SASE platform from the ground up — not retrofitted from a firewall or SD-WAN product. Every networking and security function — SD-WAN, SWG, CASB, ZTNA, FWaaS, DLP, IPS, Anti-Malware, DNS Security — is delivered as a converged service from a global private backbone.
Traffic from branches, remote users, and cloud resources is routed to the nearest Cato PoP (Point of Presence), where a single-pass processing engine inspects, secures, and optimizes every packet simultaneously. There is no sequential chaining of security modules. There is no separate networking layer and security layer. It is one system.
What this means operationally:
Fortinet's SASE offering is built atop its FortiGate firewall and SD-WAN appliances — products with a strong market reputation, particularly in enterprise firewall and branch networking. Cloud-delivered security modules (SWG, CASB, ZTNA) extend the FortiGate foundation, with FortiOS providing software-level unification.
In practice, however, real-world Fortinet SASE deployments require integrating multiple discrete products:
Each product has its own licensing model, firmware update cycle, and configuration interface. FortiOS creates a degree of coherence, but it does not eliminate the operational overhead of managing a multi-product stack across a distributed environment.
The core architectural difference: Cato converges networking and security into a single cloud service. Fortinet integrates networking and security across a portfolio of products. Both can deliver SASE outcomes — but the operational path to get there is very different.
Also Read: Advanced Posture in Cato Client: Continuous Compliance Without User Friction
Cato SASE is engineered for low-touch, rapid deployment. New sites connect to the nearest PoP. Remote users install a lightweight agent or access resources through a browser-based client. Cloud resources are onboarded through standard connectors.
There is no hardware to ship, rack, or configure at the branch level unless optional Cato edge devices are desired for specific local breakout scenarios. A global retailer with 300+ sites can migrate from a legacy environment to Cato SASE in weeks rather than months — with IT provisioning access centrally and remote users connecting without complex VPN configurations.
Fortinet SASE deployments follow a more traditional IT procurement and implementation cycle:
For a financial services firm expanding into new markets, each new branch means a hardware procurement cycle — introducing delays that have no equivalent in Cato's PoP-based model.
The deployment difference is significant. The ongoing management difference is where total cost of ownership diverges most sharply over time.
Cato SASE ongoing management:
Fortinet SASE ongoing management:
Also Read: Handling Unsupported or Legacy Clients in Cato Device Security Policies
Security integration is where Cato's single-pass architecture produces the most tangible operational benefit. Because all security functions — IPS, Anti-Malware, CASB, SWG, ZTNA, DLP — run within the same processing engine, there is no question of whether policies are consistent between the firewall and the CASB, or whether the IPS signature applied at the branch matches what remote users receive.
A remote user, a branch employee, and a cloud-hosted workload all receive identical security inspection and policy enforcement. This consistency is not a configuration achievement — it is an architectural property.
Fortinet's security capabilities are individually strong. FortiGate's firewall and IPS have well-established enterprise track records. But in a SASE context, the security value depends not just on the strength of each module, but on how reliably they work together.
In distributed Fortinet environments, policy drift is a real operational risk:
None of these are theoretical problems — they are documented pain points in enterprise Fortinet deployments at scale.
Network performance in SASE is not just a security concern — it directly affects user productivity and application experience. Cato operates a global private backbone interconnecting its PoPs with SLA-backed, optimized links. Traffic is steered over this backbone, bypassing congested public internet paths.
For a multinational organization with users in Dubai, London, Singapore, and São Paulo, this means:
Fortinet SASE relies primarily on edge routing and third-party ISPs for WAN connectivity. While FortiGate's SD-WAN capabilities can intelligently select between available ISP links, the quality ceiling is determined by those ISP links — not by a private backbone.
For organizations with branches in regions where ISP quality is variable — which includes much of the GCC, Africa, and Southeast Asia — this dependency introduces performance risk that Cato's backbone model eliminates by design.
Also Read: Cato ZTNA in Practice: Combining Identity, Device, and Context in One Policy Engine
Both Cato and Fortinet offer ZTNA. The functional difference is in how it's delivered and how consistently it applies across user types.
Cato ZTNA:
Fortinet ZTNA:
For organizations building a zero trust architecture in 2025, the integration tax of Fortinet's modular approach is a legitimate operational concern. The more components required to deliver zero trust, the more potential failure points exist in the policy enforcement chain.
Hybrid work is no longer an exception scenario — it is the default operating model for most enterprises. Cato's global PoP network and lightweight agent design mean that a user connecting from a hotel in Frankfurt or a home office in Riyadh receives the same security posture and application performance as a user sitting in headquarters.
Fortinet can deliver a strong remote access experience with FortiClient, but consistency across the full hybrid workforce — particularly in regions without a nearby Fortinet cloud node — depends heavily on configuration quality and ISP performance.
Cato Networks consistently receives above-average customer satisfaction ratings in analyst surveys and peer review platforms. The most frequently cited strengths are deployment simplicity, unified management, and the platform's rate of improvement over time.
Fortinet receives below-average customer experience ratings in the SASE category specifically — a notable contrast to its strong reputation in the firewall and SD-WAN markets. Common feedback themes include deployment complexity, fragmented management across multiple consoles, and support challenges for multi-product configurations.
Cato's cloud-native architecture enables rapid rollout of new platform capabilities without customer-side intervention. New security features, threat intelligence updates, and AI-driven analytics enhancements are delivered automatically. Customers benefit from improvements immediately, without planning maintenance windows or coordinating firmware updates.
Fortinet continues to invest in AI and automation across its platform — particularly in FortiAI and threat analytics. However, the appliance-centric model means that some innovations require hardware upgrades or firmware deployment cycles before customers can benefit from them.
Cato uses a bandwidth-based pricing model. Organizations pay for the capacity they use rather than purchasing per-feature licenses. This model bundles networking and security into a single contract, eliminating the need to separately license SWG, CASB, ZTNA, and DLP.
Operational savings come from:
Note: Cato's pricing can become less predictable as bandwidth needs grow. Organizations should model bandwidth growth scenarios carefully during the evaluation process.
Fortinet's entry-level SASE pricing can appear competitive, particularly for organizations with existing FortiGate investments. However, total cost of ownership expands as security capabilities are added:
For organizations evaluating a 3–5 year TCO, the appliance and licensing complexity of Fortinet SASE typically results in higher total spend than the initial license comparison suggests.
A global retailer with over 300 locations faces fragmented security, inconsistent enforcement between branches, and a slow onboarding process for new sites. After evaluating SASE options, the organization migrates from a Fortinet appliance-based environment to Cato's cloud-native platform.
Outcomes:
A financial services firm with distributed branches across the GCC uses FortiGate appliances and SD-WAN for branch connectivity. As the firm expands cloud adoption and grows its remote workforce, operational friction accumulates:
The firm begins evaluating converged, cloud-native alternatives — with Cato SASE's single-platform model as the primary candidate.
Cato SASE uses a bandwidth-based pricing model. While this can be cost-effective for organizations seeking agility and operational savings, some customers note that pricing transparency can be a challenge, especially as bandwidth needs grow.
Fortinet SASE offers competitive pricing for core SD-WAN and firewall functions. However, total cost of ownership can rise quickly as organizations add security modules, licenses, and appliances. The modular approach can introduce hidden costs and complicate budgeting.
Cato SASE delivers operational savings by eliminating hardware dependencies, streamlining management, and reducing the need for specialized training. Organizations benefit from faster time-to-value and lower ongoing maintenance costs.
Fortinet SASE may offer lower upfront costs for organizations with existing Fortinet investments, but long-term operational efficiency can be hindered by the complexity of managing multiple appliances, licenses, and interfaces.
A global retailer with over 300 sites faces challenges with fragmented security, inconsistent policy enforcement, and slow onboarding of new locations. After evaluating SASE vendor comparison options, the retailer migrates from a Fortinet appliance-based environment to Cato’s cloud-native SASE.
Results:
A financial services firm uses Fortinet’s SD-WAN and firewall appliances to secure its branch network. As the firm expands into cloud services and supports a growing remote workforce, operational challenges emerge:
The firm recognizes the limitations of a modular SASE deployment and begins evaluating converged, cloud-native alternatives.
Choose Cato SASE if:
Consider Fortinet SASE if:
The honest assessment: For most enterprises evaluating SASE in 2025 — particularly those with distributed workforces, multi-cloud environments, or rapid growth — Cato's converged architecture delivers better operational outcomes. Fortinet remains a strong choice for organizations with mature Fortinet estates and primarily on-premises architectures, but the gap in SASE-specific operational simplicity is real and widening.
For security and network leaders, the choice between Cato SASE vs Fortinet SASE is ultimately a decision about architectural philosophy and operational outcomes.
Key takeaways for SASE vendor comparison:
The Cato SASE vs Fortinet SASE decision ultimately comes down to this: do you want a platform that was architected for convergence, or one that approximates it through integration?
Cato Networks delivers a cloud-native, single-pass SASE platform that provides consistent security policy, predictable global performance, and operational simplicity that compound in value as organizations scale. For enterprises prioritizing agility, unified visibility, and true zero trust across a distributed workforce, it sets the benchmark for what SASE should deliver.
See how Cato SASE stacks up in real-world scenarios for enterprises like yours.
Schedule a free consultation with our experts today

No, Cato SASE is fully cloud-native and can be deployed without dedicated on-premises hardware. Optional edge devices are available for specific use cases, such as local breakout or enhanced failover, but are not required for core functionality.
Fortinet’s SASE offering is unified at the operating system level (FortiOS), but real-world deployments often require integration across multiple appliances and management tools. This can complicate operations and introduce policy inconsistencies.
Both Cato and Fortinet offer Zero Trust Network Access (ZTNA). Cato’s single-pass, cloud-native architecture enables more consistent policy enforcement across all user types and locations, while Fortinet’s ZTNA may require additional configuration and integration, especially in distributed environments.
Cato SASE’s centralized, cloud-native management and global private backbone make it particularly well-suited for hybrid and remote work scenarios. Policy enforcement and user experience are consistent regardless of location.
Cato’s bandwidth-based pricing can be less transparent, especially as bandwidth needs grow. Fortinet’s modular licensing may introduce hidden costs as requirements expand, particularly when adding new security modules or appliances.
Cato SASE enforces policies centrally, ensuring that all users, devices, and locations receive identical security inspection and access controls. Policy changes are propagated instantly across the global network, reducing risk of drift or misconfiguration.
Yes. Cato leverages a global private backbone for optimized, predictable performance, minimizing reliance on third-party ISPs. Fortinet typically depends on edge routing and public internet paths, which can introduce variability in latency and application experience.
Managing multiple Fortinet appliances and modules increases operational overhead, requiring coordination across different interfaces, firmware versions, and support contracts. This can slow response to incidents and complicate policy enforcement.
Yes. Cato’s cloud-native design enables rapid onboarding of new sites, users, and cloud resources without the need for hardware procurement or complex configuration. Organizations can scale globally in weeks rather than months.
Cato SASE is recognized for ongoing innovation, particularly in AI-driven security analytics and automated management. The cloud-native platform allows for rapid feature rollout. Fortinet continues to evolve its platform, but the modular, appliance-centric model can slow adoption of new capabilities and increase operational burden.
The main limitations include increased deployment complexity, risk of policy inconsistency, reliance on multiple management consoles, and potential for hidden costs as new modules or appliances are added. This can hinder agility and operational efficiency, especially in fast-growing or highly distributed organizations.
Yes, both Cato and Fortinet include SD-WAN as a core capability within their SASE offerings. However, Cato’s SD-WAN is fully integrated into its cloud-native platform, while Fortinet’s SD-WAN is typically delivered via FortiGate appliances and may require additional integration for full SASE functionality.
Cato SASE provides consistent security and connectivity for users accessing resources across multiple clouds, with centralized policy and visibility. Fortinet can support multi-cloud environments, but integration and policy consistency may require additional configuration and management effort.
Cato SASE’s unified, cloud-native management reduces the need for specialized training and simplifies day-to-day operations. Fortinet’s modular stack may require IT teams to develop expertise across multiple products and interfaces, increasing training requirements and operational risk.
Cato SASE’s cloud-native, converged architecture is best suited for organizations experiencing rapid growth or frequent change. It enables fast onboarding, centralized management, and seamless scaling without the friction of hardware procurement or complex integration.

Anas is an Expert in Network and Security Infrastructure, With over seven years of industry experience, holding certifications Including CCIE- Enterprise, PCNSE, Cato SASE Expert, and Atera Certified Master. Anas provides his valuable insights and expertise to readers.
Share it with friends!
share your thoughts