.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
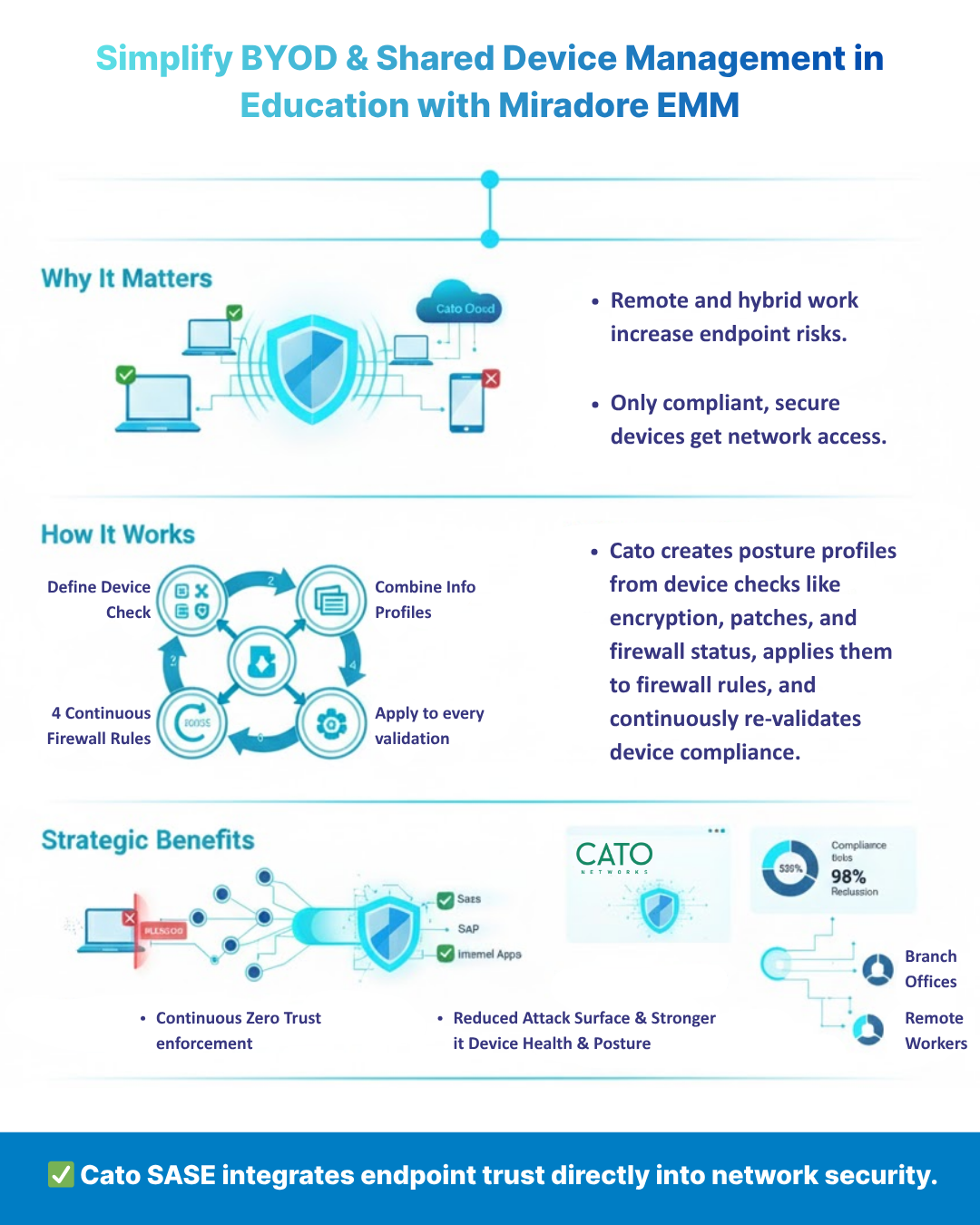
As enterprises expand hybrid work and remote access, verifying that every connected endpoint meets corporate security standards has become essential. Cato SASE’s Device Posture Profiles and Device Checks enable this verification by embedding device health validation directly into WAN and Internet Firewall rules, ensuring only compliant, secure endpoints gain network access.
Within the Cato SASE platform, Device Posture Profiles serve as the foundation of Zero Trust Network Access (ZTNA) enforcement.
Instead of granting access solely based on user identity or network location, Cato continuously evaluates the security posture of each device — validating whether anti-malware, disk encryption, patch management, and firewall configurations meet defined standards.
This posture verification ensures access is conditional and dynamic, maintaining alignment with organizational compliance frameworks such as ISO 27001 or NIST principles.
Cato’s Device Checks define individual endpoint health criteria (for example, “Disk Encryption = Enabled” or “Anti-Malware = Latest Version”).
Administrators can combine multiple checks into a single Device Posture Profile, then associate that profile with WAN or Internet Firewall rules inside the Cato Management Application (CMA).
This workflow ensures a unified enforcement model whether users connect remotely or through an on-premises Cato Socket.
Cato SASE supports a wide array of posture checks, with minimum Cato Client versions required for each OS.
| Device Check | Windows | macOS | Linux | Notes |
|---|---|---|---|---|
| Anti-Malware | v5.2 | v5.2 | v5.1 | Vendor/product/version match |
| Firewall Status | v5.4 | v5.2 | v5.1 | macOS version = firewall version |
| Disk Encryption | v5.5 | v5.6 | — | Software-based only |
| Patch Management | v5.5 | v5.2 | v5.2 | Supports “greater than” operator |
| Device Certificate | v5.5 | v5.4 | v5.1 | RSA certificates only |
| DLP Agent | v5.9 | v5.4.3 | v5.2 | — |
| Running Process | v5.11 | v5.7 | — | Uses Thumbprint/Team ID |
| Registry Key / plist Check | v5.11 | v5.7 | — | Windows = Registry, macOS = plist |
Only software-based encryption is supported for Disk Encryption checks, and checks are periodically validated every 10 minutes or at custom intervals defined in policy.
Cato employs both AND and OR relationships to evaluate posture and device criteria efficiently:
Example:
A firewall rule allowing access only to Windows devices AND located in India AND meeting Profile 1 ensures precise, policy-driven access control.
Unsupported Clients can either skip or fail the check depending on administrator configuration — a recommended policy is to minimize exemptions.
The Cato Management Application provides multiple tools to monitor posture compliance and troubleshoot enforcement issues:
If inconsistent posture detection occurs, Cato advises verifying Client version compliance and contacting Support for deeper investigation.
Cato’s Device Posture Profiles extend firewall intelligence beyond IPs and users — integrating endpoint trustworthiness into every access decision.
By continuously verifying device compliance and integrating with Cato ZTNA, organizations gain measurable benefits:
If You Need Further Details On Implementing Device Posture Profiles, Configuring Device Checks, Or Strengthening Zero-Trust Enforcement In Your Organization, Please Feel Free To Schedule a No-Obligation Requirement-Gathering Virtual Meeting With Our Cato SASE Experts. Schedule Now
Cato SASE enforces endpoint compliance by evaluating each device against defined posture checks such as anti-malware, disk encryption, and patch management. These checks are embedded within firewall rules to ensure only secure devices can access network resources.
Cato SASE supports Anti-Malware, Firewall Status, Disk Encryption, Patch Management, Device Certificate, DLP, Running Process, Registry Key, and Property List (plist) checks. Each check validates specific endpoint configurations to maintain Zero Trust compliance.
Yes. Administrators can attach posture profiles to both WAN and Internet Firewall rules within the Cato Management Application, applying identical security policies to internal and external traffic flows.
Minimum versions: Windows v5.7, macOS v5.8, and Linux v5.3 for devices behind a Socket. For continuous posture checks (Advanced Posture), Windows v5.15 + and macOS v5.9 + are required.
Cato Device Posture Profiles provide continuous verification of device integrity, a core ZTNA principle. By ensuring every device meets security posture requirements before and during access, organizations achieve true “never trust, always verify” enforcement.
An SDP (ZTNA) license is required for the Cato Client as an identity agent, and a Device Inventory license is needed only when combining posture profiles with device attributes in firewall rules.
Administrators should review the Access Overview dashboard and Events page in the CMA. Failures are logged under Client Connectivity Policy events, allowing quick isolation of version mismatches or misconfigured checks.
Because endpoint states change dynamically — updates fail, antivirus gets disabled, encryption lapses — Cato SASE’s continuous posture validation ensures any drift from compliance is immediately detected and access is adjusted in real time.

Anas is an Expert in Network and Security Infrastructure, With over seven years of industry experience, holding certifications Including CCIE- Enterprise, PCNSE, Cato SASE Expert, and Atera Certified Master. Anas provides his valuable insights and expertise to readers.
Share it with friends!
share your thoughts