.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

A decade ago, SD-WAN was the answer. Enterprises drowning in MPLS costs and rigid carrier-managed WAN infrastructure found in SD-WAN a practical, cost-effective escape route — one that delivered centralized management, application visibility, and the ability to leverage broadband and LTE alongside or instead of expensive leased lines.
That era is over. Not because SD-WAN failed at what it was designed to do, but because what enterprises need from their networks has changed so fundamentally that SD-WAN's original design assumptions no longer hold. The branch-to-data-center traffic model that SD-WAN optimized for represents a minority of enterprise traffic in 2025. SaaS applications, cloud workloads, and users working from home, hotels, and client sites now dominate the traffic landscape — and SD-WAN was not built for any of them.
For CISOs, Security Architects, Network Architects, and IT infrastructure leaders, this is not an abstract architectural debate. It has direct operational consequences: degraded performance for cloud applications, growing security complexity as point solutions multiply around SD-WAN's edges, and escalating operational overhead managing a fragmented stack of networking and security tools with no unified visibility.
SASE — Secure Access Service Edge — was designed specifically to address these consequences. This comparison examines what SD-WAN does well, where it falls short in the cloud era, and why Cato Networks' converged SASE platform represents the logical next step for enterprises that have outgrown what SD-WAN can deliver.
SD-WAN emerged as a direct response to the cost and inflexibility of MPLS-dominated enterprise WAN architectures. Its core value proposition was compelling and, for its time, genuinely transformative:
Cost-effective routing by leveraging broadband, LTE, and other commodity transports alongside or instead of expensive MPLS circuits, dramatically reducing WAN spending for enterprises with many branch locations.
Centralized policy management that allowed network teams to configure and manage routing policy from a single console rather than configuring individual devices at each site, reducing operational overhead and improving consistency.
Application-layer visibility through Layer 7 awareness that enabled traffic steering and prioritization based on application identity, improving performance for business-critical applications over shared WAN links.
Rapid site deployment that allowed new branches to come online in days rather than weeks, eliminating dependency on carrier provisioning timelines for MPLS circuit activation.
For enterprises with distributed branch networks and predictable, data-center-centric traffic patterns, SD-WAN delivered on its promise. The MPLS replacement use case was a genuine success story for the technology.
The problem is not that SD-WAN stopped working. The problem is that the environment it was designed for stopped being the dominant enterprise reality. Cloud adoption, SaaS proliferation, and distributed hybrid workforces have exposed four structural limitations in SD-WAN's architecture that no amount of configuration optimization can fully address.
Cloud application performance degradation: Most SD-WAN deployments route cloud-bound traffic through data centers before it reaches the internet — a design that made sense when applications lived in data centers but adds unnecessary latency hops for SaaS traffic that could go directly to cloud provider infrastructure. Users accessing Office 365, Salesforce, or Zoom through an SD-WAN architecture that backhauled traffic to a central data center experienced this as slow application performance, video call degradation, and frequent IT complaints.
Security fragmentation through bolt-on complexity: SD-WAN encrypts traffic in transit but does not provide the advanced security capabilities that modern enterprise environments require. To close that gap, enterprises bolt on next-generation firewalls, secure web gateways, cloud access security brokers, and VPN concentrators around their SD-WAN infrastructure. The result is an operational environment with multiple security vendors, multiple management consoles, multiple policy engines, and the inevitable configuration drift that occurs when those systems are not perfectly synchronized.
Limited native cloud integration: SD-WAN was designed for branch-to-data-center connectivity, not for direct-to-cloud access or seamless integration with SaaS and IaaS platforms. Optimizing SD-WAN for cloud access typically requires additional overlay configurations, cloud on-ramp products, or compromises that undermine the clean architecture SD-WAN promised to deliver.
Visibility fragmentation across tools: With networking managed through the SD-WAN platform and security managed through multiple separate tools, achieving unified visibility across the complete traffic landscape requires manual correlation between systems — or investment in yet another layer of monitoring and analytics tooling. Security operations teams investigating incidents frequently cannot see the full picture from any single interface.
The modern enterprise is defined by its cloud-first strategy and decentralized workforce :
These trends demand a new approach to connectivity and security—one that is agile, scalable, and built for the cloud.
With the perimeter gone, security must evolve:
SD-WAN, even when augmented with security appliances, cannot natively deliver these capabilities at the scale and agility required by modern enterprises.
Secure Access Service Edge is a cloud-delivered framework that converges networking and security into a single unified platform. The defining characteristic of SASE is not the presence of any specific capability — it is the convergence of networking and security functions under a common architecture, policy engine, and management plane.
Cloud-native SD-WAN provides dynamic, policy-driven routing across any transport — broadband, LTE, MPLS, or dedicated fiber — optimized for both branch offices and remote users without requiring on-premises appliances at every location.
Firewall-as-a-Service (FWaaS) delivers network-level policy enforcement from the cloud, applying next-generation firewall capabilities including application awareness, identity-based controls, and threat inspection to all traffic without requiring physical firewall appliances.
Secure Web Gateway (SWG) provides real-time inspection of web and internet traffic for malware, phishing content, malicious URLs, and policy violations, applied inline to all users regardless of location.
Cloud Access Security Broker (CASB) delivers visibility and control over SaaS application usage, enforcing data security policies and detecting unauthorized SaaS adoption across the organization.
Zero Trust Network Access (ZTNA) grants application access based on verified user identity, device health, and request context, replacing location-based trust with continuous, explicit verification for every session.
Data Loss Prevention (DLP) monitors and controls sensitive data movement across all traffic types and applications, enforcing data governance requirements consistently regardless of where users and data are located.
Globally distributed Points of Presence interconnect users, sites, and cloud applications through geographically close inspection and routing points, minimizing latency by processing traffic at the edge rather than backhauling it to central inspection points.
The critical distinction is architectural, not just functional. Adding security appliances alongside SD-WAN produces a collection of tools that must be integrated and coordinated to achieve consistent behavior. SASE converges those functions under a shared architecture where they are designed to work together from the ground up — sharing a policy engine, sharing threat intelligence, sharing a management interface, and sharing a data plane.
That convergence produces outcomes that the add-on approach cannot replicate: genuinely consistent policy enforcement across all traffic and users, unified visibility without manual correlation between systems, and operational simplicity from managing one platform rather than many..
Also Read: Client Connectivity Policy in Cato SASE: Controlling Who Can Connect and Why
Many vendors claim to offer SASE by integrating SD-WAN with security appliances—often from multiple vendors. This approach introduces complexity, policy fragmentation, and operational risk.
Cato SASE is different. Cato delivers a unified SASE platform as a single, cloud-native service:
A key differentiator for Cato is its global private backbone :
This approach delivers a secure SD-WAN alternative that is purpose-built for the demands of modern enterprises.
Cato’s security stack is fully integrated and cloud-delivered:
Security updates and threat intelligence are applied globally, ensuring all users benefit from the latest protections—without manual intervention.
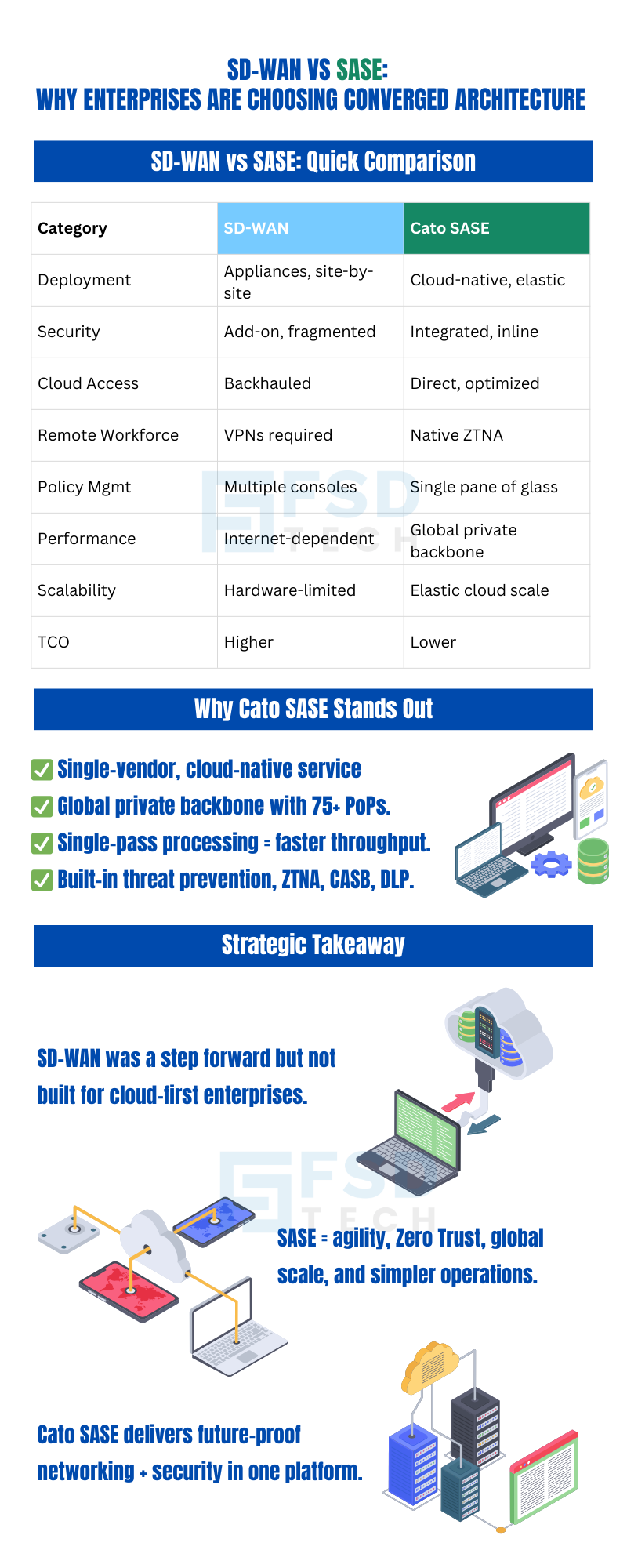
| Feature/Capability | SD-WAN (Standalone) | Cato SASE (Converged) |
|---|---|---|
| Architecture | Appliance-based overlay | Cloud-native, single-vendor |
| Deployment Model | On-premises appliances | Cloud-delivered, lightweight edge devices or clientless for remote users |
| Cloud Integration | Limited, often backhauled | Native, direct-to-cloud via global PoPs |
| Scalability | Hardware-dependent | Instantly scalable, elastic |
SD-WAN requires deploying and managing physical or virtual appliances at every site. Scaling to support new locations or remote users often means more hardware, more configuration, and more complexity. In contrast, Cato SASE uses lightweight edge devices (or clientless access for remote users) and cloud-based orchestration, enabling rapid, elastic scaling with minimal operational overhead.
| Security Aspect | SD-WAN (Standalone) | Cato SASE (Converged) |
|---|---|---|
| Integrated Security | No (requires add-ons) | Yes (NGFW, SWG, CASB, ZTNA, DLP) |
| Zero Trust | Not native | Built-in |
| Policy Consistency | Fragmented, device-based | Unified, cloud-delivered |
| Threat Prevention | Variable, appliance-based | Inline, always-on |
Standalone SD-WAN encrypts traffic but relies on external appliances for advanced security. This creates policy gaps and increases the risk of misconfiguration. Cato SASE delivers a unified SASE platform with security built-in, ensuring consistent policy enforcement and comprehensive threat protection everywhere.
| Operational Factor | SD-WAN (Standalone) | Cato SASE (Converged) |
|---|---|---|
| Management | Multiple consoles, vendors | Single pane of glass |
| Troubleshooting | Siloed, complex | End-to-end visibility |
| Total Cost of Ownership | Higher (multiple tools, vendors, support contracts) | Lower (converged platform, reduced hardware, unified support) |
Cato SASE simplifies operations by consolidating networking and security into a single platform. IT teams gain deep visibility, unified policy management, and streamlined troubleshooting—reducing both operational overhead and risk. The result is a lower total cost of ownership compared to piecemeal SD-WAN plus security stacks.
Also Read: Advanced Posture in Cato Client: Continuous Compliance Without User Friction
A regional retail and distribution giant with more than 50 sites struggled with ongoing challenges in its SD-WAN deployment.
After migrating to Cato SASE, the manufacturer achieved:
Simplified operations: One platform, one support team, and no more hardware sprawl.
The enterprise perimeter is gone. Applications and users are everywhere. SD-WAN, while transformative in its day, cannot meet the demands of the modern, cloud-first enterprise.
Cato SASE is the next logical step—a converged, cloud-native platform that delivers secure, optimized access for every user, everywhere. The benefits are clear:
For CISOs, Security Architects, Network Architects, and IT Infrastructure Leads, the path forward is clear:
Also Read: Handling Unsupported or Legacy Clients in Cato Device Security Policies
Transitioning from SD-WAN to SASE does not require a big-bang cutover. Most organizations migrate incrementally, validating the platform at each stage before expanding adoption. The following sequence provides a practical framework for a phased migration.
Stage 1 — Inventory and Assessment Map all sites, remote users, applications, and current security controls comprehensively. Document performance baselines, security policy inventories, and compliance requirements. Identify the pain points in your current environment that migration should resolve.
Stage 2 — Define Success Metrics Establish the KPIs against which migration success will be measured — application performance improvement, reduction in security incidents, decrease in mean time to resolution, operational overhead reduction, and TCO impact. These metrics provide the quantitative foundation for both validating the migration and communicating its value to executive stakeholders.
Stage 3 — Select Pilot Sites and Users Choose a subset of locations and a representative sample of remote users for the initial pilot deployment. Select sites that include the traffic patterns and use cases most relevant to your organization — a mix of cloud-heavy users, branch-to-branch communication requirements, and remote access scenarios provides the most useful validation data.
Stage 4 — Deploy Cato Edge Devices and Remote Access Connect pilot sites to the Cato platform using lightweight edge devices. Provision remote pilot users through the Cato client. Verify connectivity to the nearest PoPs and confirm that application performance meets or exceeds baseline measurements.
Stage 5 — Migrate Security Policies Translate existing firewall rules, VPN access policies, and application access controls into Cato's unified policy engine. This is the most analytically demanding stage of the migration — policies that were distributed across multiple separate systems must be rationalized into a coherent single-engine policy set. Use the migration as an opportunity to simplify and rationalize policy rather than replicating legacy complexity.
Stage 6 — Monitor, Validate, and Optimize Run the pilot deployment under observation for a defined validation period. Use Cato's analytics and visibility tools to confirm that policy is being applied as intended, that performance metrics are meeting targets, and that security coverage is complete. Address any gaps or performance issues before expanding the deployment.
Stage 7 — Expand Adoption by Wave Onboard additional sites and user populations in waves, expanding from the pilot cohort to broader adoption as legacy contracts expire or as validation results justify acceleration. Prioritize sites where current SD-WAN limitations are most acute.
Stage 8 — Decommission Legacy Infrastructure As Cato SASE coverage expands, systematically retire the hardware and software it replaces — SD-WAN appliances, VPN concentrators, standalone firewall devices, and the management tools and support contracts associated with them. Document the operational and cost benefits realized at each stage.
Stage 9 — Continuous Optimization Use Cato's ongoing analytics and visibility capabilities to continuously refine the deployment — adjusting QoS policies, tightening access controls as Zero Trust maturity develops, and incorporating new Cato capabilities as they are released.
At the heart of Cato’s platform is its single-pass architecture . Unlike traditional solutions that process traffic multiple times—once for networking, again for security—Cato inspects and routes each packet only once. This delivers:
How it works:
1. Traffic enters the nearest Cato PoP —from a branch, remote user, or cloud connector.
2. Single-pass engine inspects traffic: Applies NGFW, SWG, CASB, ZTNA, and DLP policies in one streamlined process.
3. Traffic is routed over Cato’s private backbone to its destination—another site, a cloud service, or the internet.
4. End-to-end visibility and analytics are captured for every flow, enabling real-time monitoring and rapid troubleshooting.
This architecture is a cornerstone of Cato’s ability to deliver cloud-first network security at scale.
An India- and GCC-based IT/ITES company with thousands of remote and hybrid employees was struggling with growing challenges in its SD-WAN approach.
By adopting Cato SASE, the enterprise achieved:
Key Differences:
| Category | SD-WAN (Standalone) | Cato SASE (Unified SASE Platform) |
|---|---|---|
| Deployment | Appliance-based, site-by-site | Cloud-native, global PoPs |
| Security | Add-on, fragmented | Integrated, inline |
| Cloud Access | Often indirect/backhauled | Direct, optimized |
| Remote Workforce | VPN required, complex | ZTNA, seamless |
| Policy Management | Multiple consoles | Single pane of glass |
| Performance | Public internet dependent | Global private backbone |
| Scalability | Hardware-limited | Elastic, cloud-scale |
| Total Cost of Ownership | High (multiple vendors) | Lower (converged, single vendor) |
The debate of SD-WAN vs SASE is not just about technology—it’s about enabling the business to move faster, stay secure, and deliver a superior user experience in a cloud-first world. SD-WAN was a critical step forward, but its limitations are now clear. The future belongs to platforms that converge networking and security, eliminate complexity, and scale with the needs of the modern enterprise.
Cato SASE explained: Cato’s single-vendor, cloud-native SASE platform delivers on this vision—providing a secure SD-WAN alternative that is built for agility, security, and simplicity. With a global private backbone, integrated security stack, and unified management, Cato empowers IT leaders to replace SD-WAN with SASE and future-proof their networks.
Strategic Takeaway: SD-WAN is no longer enough. The next logical step is a unified SASE platform that delivers cloud-first network security, Zero Trust Network Access, and operational excellence—everywhere your business operates.
Ready to move beyond SD-WAN? Contact FSD-Tech for a personalized assessment and see how converged SASE can transform your enterprise network.
No. While SASE incorporates SD-WAN’s connectivity, it natively integrates a full security stack—firewall, ZTNA, CASB, SWG, DLP—and delivers both networking and security as a unified, cloud-native service. This convergence enables consistent policy enforcement, deep visibility, and operational simplicity that cannot be achieved by simply bolting security onto SD-WAN.
Yes. Many organizations choose to replace SD-WAN with SASE in phases. You can start by onboarding select sites or remote users to Cato SASE, validate the architecture, and then expand adoption as legacy contracts expire or as business needs evolve. This incremental approach reduces risk and disruption.
Cato’s global private backbone provides predictable latency, high availability, and optimized routing between all connected sites and users. Unlike SD-WAN solutions that rely on the variable public internet, Cato’s backbone is SLA-backed and connects directly to major cloud providers, ensuring consistent performance for critical applications.
Cato SASE enables secure, optimized access for users everywhere—branch, home, or on the go. By replacing legacy VPNs with Zero Trust Network Access (ZTNA), users benefit from seamless, direct-to-cloud connectivity with integrated security. This improves user experience, reduces IT support tickets, and strengthens the overall security posture.
Yes. SASE is purpose-built for cloud-first organizations, delivering direct, secure access to SaaS and IaaS applications without backhauling or performance bottlenecks. Integrated security and unified management further reduce risk and operational overhead compared to traditional SD-WAN solutions.
SASE simplifies compliance by enforcing consistent security policies, access controls, and data protection measures across all users and locations. Centralized visibility and reporting make it easier to demonstrate compliance with regulations such as GDPR, HIPAA, and PCI DSS.
Cato SASE delivers ZTNA as a core component of its platform. Access is granted based on user identity, device posture, and context, with continuous verification for every session. This ensures that only authorized users and devices can access sensitive resources, regardless of location.
Yes. Cato SASE provides a fully integrated security stack—including NGFW, SWG, CASB, ZTNA, and DLP—delivered as a cloud service. This allows organizations to retire legacy firewalls, VPN concentrators, and web gateways, consolidating security into a single, unified platform.
Moving to a unified SASE platform like Cato dramatically simplifies operations. IT teams manage networking and security from a single console, with end-to-end visibility and analytics. Automated updates, global policy enforcement, and integrated threat intelligence reduce manual effort and operational risk.
Cato’s global private backbone and distributed PoPs enable organizations to connect new sites and users anywhere in the world with minimal effort. The platform scales elastically, ensuring consistent performance and security regardless of geographic location. This makes it ideal for supporting mergers, acquisitions, and rapid business growth.

Anas is an Expert in Network and Security Infrastructure, With over seven years of industry experience, holding certifications Including CCIE- Enterprise, PCNSE, Cato SASE Expert, and Atera Certified Master. Anas provides his valuable insights and expertise to readers.
Share it with friends!
share your thoughts