.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

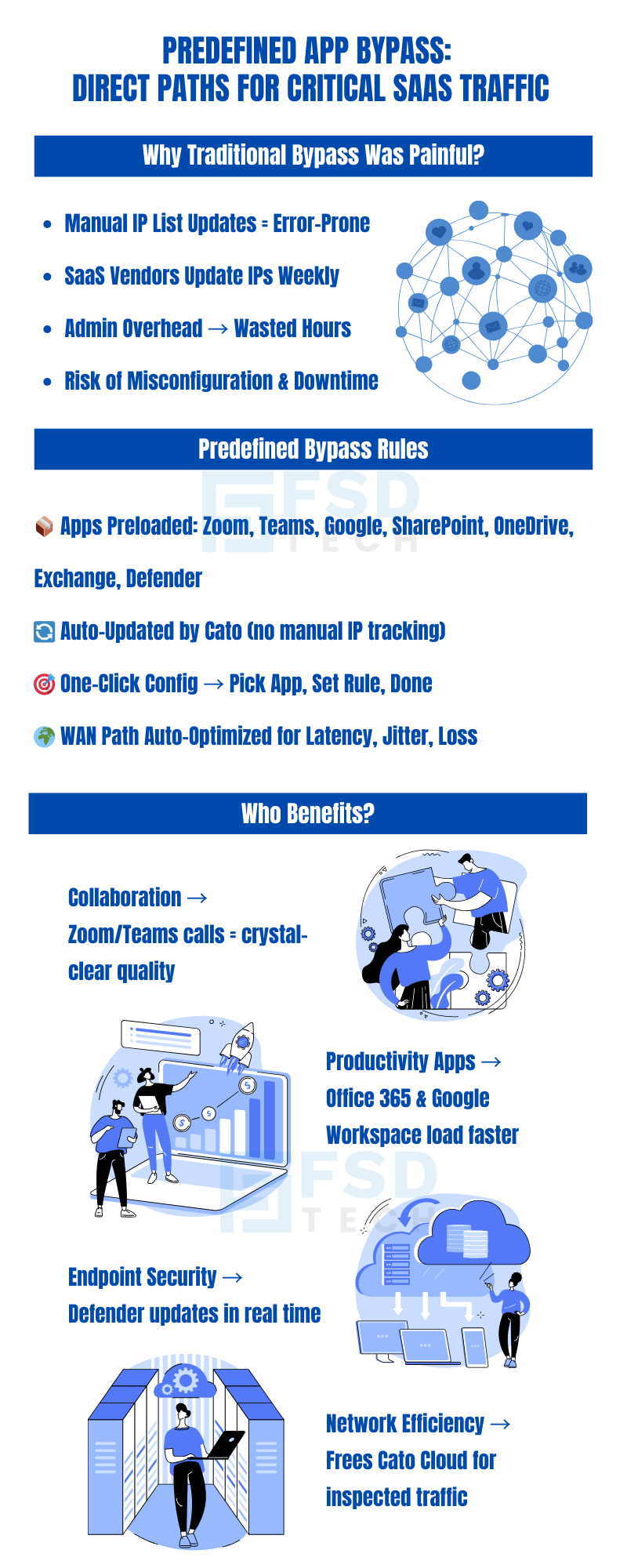
Every network administrator managing a modern enterprise environment knows this pain: you set up a bypass rule for Microsoft Teams or Zoom, everything works smoothly for a few weeks, and then performance degrades. An update somewhere changed an IP range. Your static rule is now routing traffic the wrong way. You spend an afternoon cross-referencing Microsoft's published endpoint lists, updating subnet entries, and hoping you caught everything.
Multiply that across Zoom, Microsoft 365, Google Workspace, SharePoint, and Microsoft Defender for Endpoint — all of which regularly update their infrastructure — and manual IP-based bypass management becomes a significant ongoing operational burden. It is reactive by nature, error-prone under pressure, and entirely disconnected from the business outcome it is supposed to deliver: fast, reliable connectivity for the applications your employees use most.
Cato Networks addresses this directly with Predefined Application Bypass Rules, a capability that eliminates manual IP tracking while preserving the performance benefits of direct internet egress for business-critical SaaS platforms.
Before examining the predefined rules specifically, it is worth understanding the broader capability they build upon.
Bypassing the Cato Cloud allows administrators to configure rules that let selected internet-bound traffic egress directly from Socket and vSocket sites — meaning that traffic takes a straight path to the internet rather than traversing Cato's Points of Presence (PoPs) for inspection and routing.
This matters for a specific category of applications. Cato's global PoP network delivers significant value for most enterprise traffic: threat inspection, application-layer policy enforcement, optimized routing across the backbone, and centralized visibility. But for certain well-known, high-volume SaaS applications — particularly real-time collaboration tools — the additional hop through a PoP can introduce latency that degrades call quality, increases jitter, or slows file sync operations. Direct egress removes that hop for traffic that does not require Cato's inspection to be secure or compliant.
Several important behavioral characteristics apply to bypassed traffic:
Traffic defined in a bypass rule does not pass through Cato Cloud security inspection, nor is it subject to application or category-level policies.
Upstream bandwidth profiles and QoS rules configured at the Socket level remain enforced, maintaining traffic shaping even for bypassed flows.
Downstream QoS is not applied, because bypassed traffic does not pass through a PoP.
The Socket continuously monitors WAN performance metrics — latency, jitter, packet loss, and congestion — and automatically routes bypassed traffic over the best available path.
Administrators can optionally configure a Preferred Socket WAN Role to define a primary path for predictable traffic steering.
This capability is available exclusively for Socket and vSocket sites. It does not apply to clientless or cloud-only deployments.
Also Read: Cato Captive Portal for Guest Networks: Secure, Branded, and Monitored Access
Cato now provides Predefined Application Bypass Rules, which eliminate the need to manage dynamic IP ranges manually. These rules let administrators select specific business-critical applications directly when creating a bypass rule.
Currently supported applications include:
Cato continuously updates the IP definitions for these applications in the background. This ensures bypass rules always remain current without requiring administrator intervention.
Both approaches complement each other, providing flexibility for unique traffic scenarios and efficiency for common applications.
Not sure which bypass strategy fits your environment?
Also Read: Data-Driven Safe TLS Inspection: Smarter Setup, Safer Traffic, Better User Experience
Bypassing the Cato Cloud is a powerful capability that provides direct egress for selected Internet traffic from Socket and vSocket sites. With the introduction of Predefined Application Bypass Rules, administrators gain a streamlined way to optimize traffic for commonly used SaaS platforms—without the operational burden of tracking IP ranges.
By combining traditional Bypass Rules and Predefined Application Bypass Rules, enterprises achieve both flexibility and efficiency, ensuring high performance for critical applications while maintaining centralized control.
Want to see how predefined bypass rules can improve your Teams and Zoom performance?
Book a free consultation with our experts today.
A Bypass Rule is manually configured using IPs, ports, or protocols. A Predefined Application Bypass Rule lets administrators select specific applications from a list maintained by Cato.
No. Traffic defined in bypass rules does not pass through PoP-level security services. Only Socket-level QoS and bandwidth profiles apply.
Yes. Administrators can mix traditional Bypass Rules with Predefined Application Bypass Rules as needed.
No. Bypassing the Cato Cloud applies only to Socket and vSocket sites.
The Socket automatically reroutes traffic to the best available WAN link using real-time performance metrics.
Applications like Zoom and Teams are latency-sensitive. By routing them directly to the Internet, organizations reduce delay and improve quality for voice and video sessions.

Anas is an Expert in Network and Security Infrastructure, With over seven years of industry experience, holding certifications Including CCIE- Enterprise, PCNSE, Cato SASE Expert, and Atera Certified Master. Anas provides his valuable insights and expertise to readers.
Share it with friends!
share your thoughts